ROBOT 321
@iamrobot321
ID: 288326642
26-04-2011 17:11:12
7,7K Tweet
122 Followers
1,1K Following




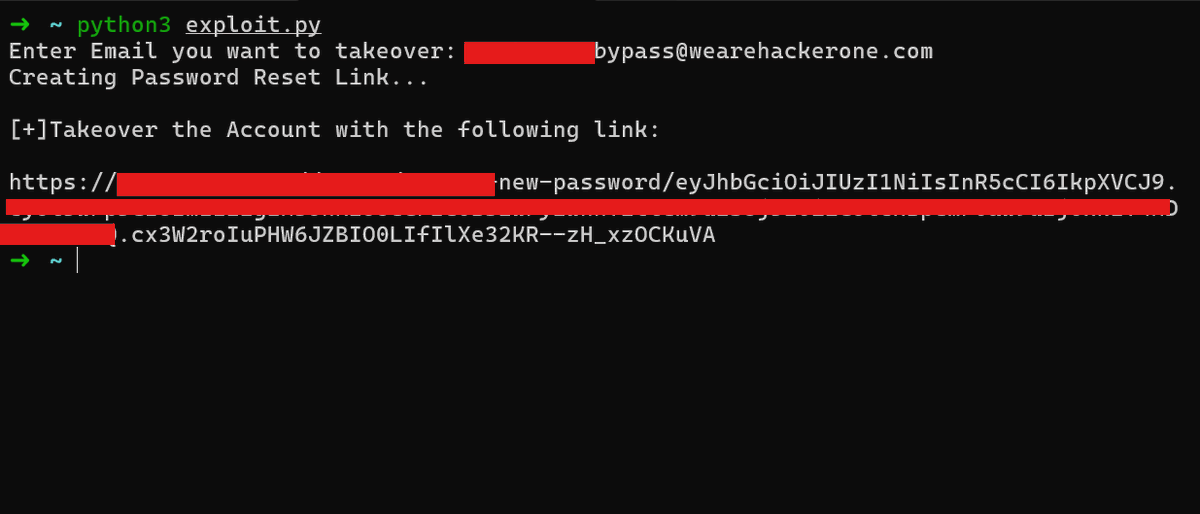
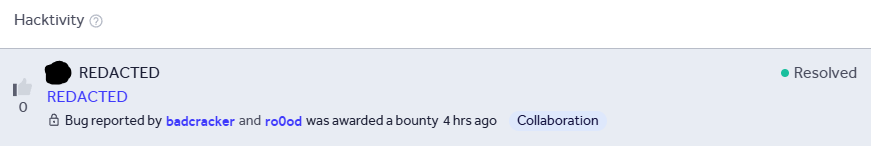
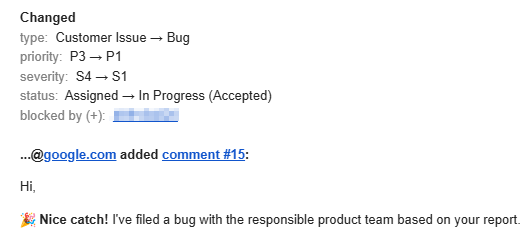
Auth bypass gave access to an internal AI chatbot and exposed sensitive internal data 🔥 with mhmd berro (badcracker) #BugBounty






Just got a reward for a high vulnerability submitted on YesWeHack ⠵ -- Improper Authentication - Generic (CWE-287). yeswehack.com/hunters/mrzhee… #YesWeRHackers #BugBounty #vulnerability #hacker #hackers







Day TWO of FIVE days of celebrating our 2 year ARCANUM-VERSARY! Arcanum Information Security 3rd Giveaway = FOUR seats to our new course by the_IDORminator "Zero to [BAC] Hero" ! 👍 1 Like = 1 Entry! ♻️ 1 Share = 2 Entries! Winners announced 1/21! Syllabus link below 👇
![Jason Haddix (@jhaddix) on Twitter photo Day TWO of FIVE days of celebrating our 2 year ARCANUM-VERSARY! <a href="/arcanuminfosec/">Arcanum Information Security</a>
3rd Giveaway = FOUR seats to our new course by <a href="/the_IDORminator/">the_IDORminator</a> "Zero to [BAC] Hero" !
👍 1 Like = 1 Entry!
♻️ 1 Share = 2 Entries!
Winners announced 1/21! Syllabus link below 👇 Day TWO of FIVE days of celebrating our 2 year ARCANUM-VERSARY! <a href="/arcanuminfosec/">Arcanum Information Security</a>
3rd Giveaway = FOUR seats to our new course by <a href="/the_IDORminator/">the_IDORminator</a> "Zero to [BAC] Hero" !
👍 1 Like = 1 Entry!
♻️ 1 Share = 2 Entries!
Winners announced 1/21! Syllabus link below 👇](https://pbs.twimg.com/media/G-j5313bQAAkTIK.jpg)

Yeay, I was awarded for a valid submission on HackenProof hackenproof.com #hackenproofed #bugbounty






![𐰚𐰼𐰇𐱅 (@ynsmroztas) on Twitter photo First report of 2026 🥳🥰🌹
Sometimes services behave as if they have authentication, it's just a matter of how it's added. For those in JSON format, definitely try this: "--headers="Content-Type: application/json\nAuthorization: Bearer [TOKEN_HERE]" \"
payload ; First report of 2026 🥳🥰🌹
Sometimes services behave as if they have authentication, it's just a matter of how it's added. For those in JSON format, definitely try this: "--headers="Content-Type: application/json\nAuthorization: Bearer [TOKEN_HERE]" \"
payload ;](https://pbs.twimg.com/media/G9pYzPcXQAAY2xM.jpg)