Hritik Sharma
@iamhritiksh
Hacker | Bug Bounty Hunter | BugCrowd MVP | bugcrowd.com/hritiksh | hackerone.com/hritiksh | Detectify Crowdsource
ID: 833160635269672960
https://hritiksh.medium.com/ 19-02-2017 03:45:49
1,1K Tweet
547 Followers
345 Following







Crafting a Full Exploit RCE from a Crash in Autodesk Revit RFA File Parsing: Trend ZDI researcher Simon Zuckerbraun shows how to go from a crash to a full exploit - & he provides you tools to do the same, including his technique used to get ROP execution. zerodayinitiative.com/blog/2025/10/6…



Serious bugs often occur in third-party components integrated by other software. Ivan Fratric 💙💛 and I found this vulnerability in the Dolby Unified Decoder. It affects Android, iOS and Windows among other platforms, sometimes 0-click. project-zero.issues.chromium.org/issues/4280754…



With only 48 hours remaining in a bug bounty event, I used Hacktron AI CLI to perform large-scale analysis of several JDBC drivers. Netting $85,000 in total rewards. This write-up shows how AI-assisted vulnerability research is speeding up the work of researchers and leading to





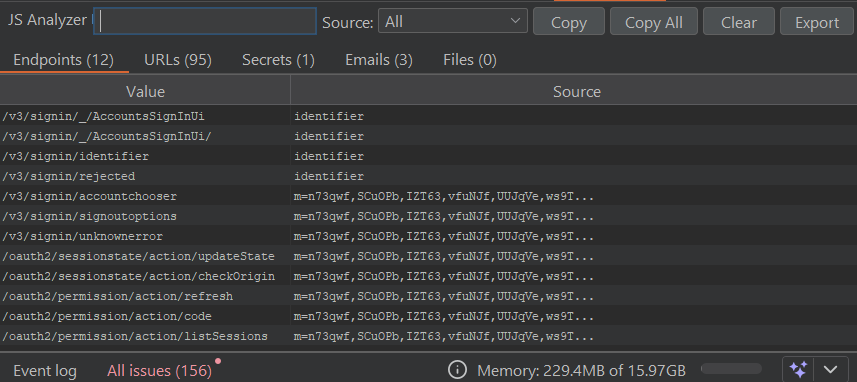
As soon as I saw this come across my feed, I had to throw something together quickly to make use of this, as it will be a major help during recon for bug bounty. Thanks The Hacker's Choice (@[email protected]) . Here is a simple python tool with a couple features that will use their API to help in your