ThreatHunter-Playbook
@hunterplaybook
I document #ThreatHunting playbooks in the form of #jupyter notebooks and share them with the world! github.com/OTRF/ThreatHun… @Cyb3rWard0g
ID: 1071463197486473218
https://threathunterplaybook.com/ 08-12-2018 17:55:07
86 Tweet
6,6K Takipçi
7 Takip Edilen

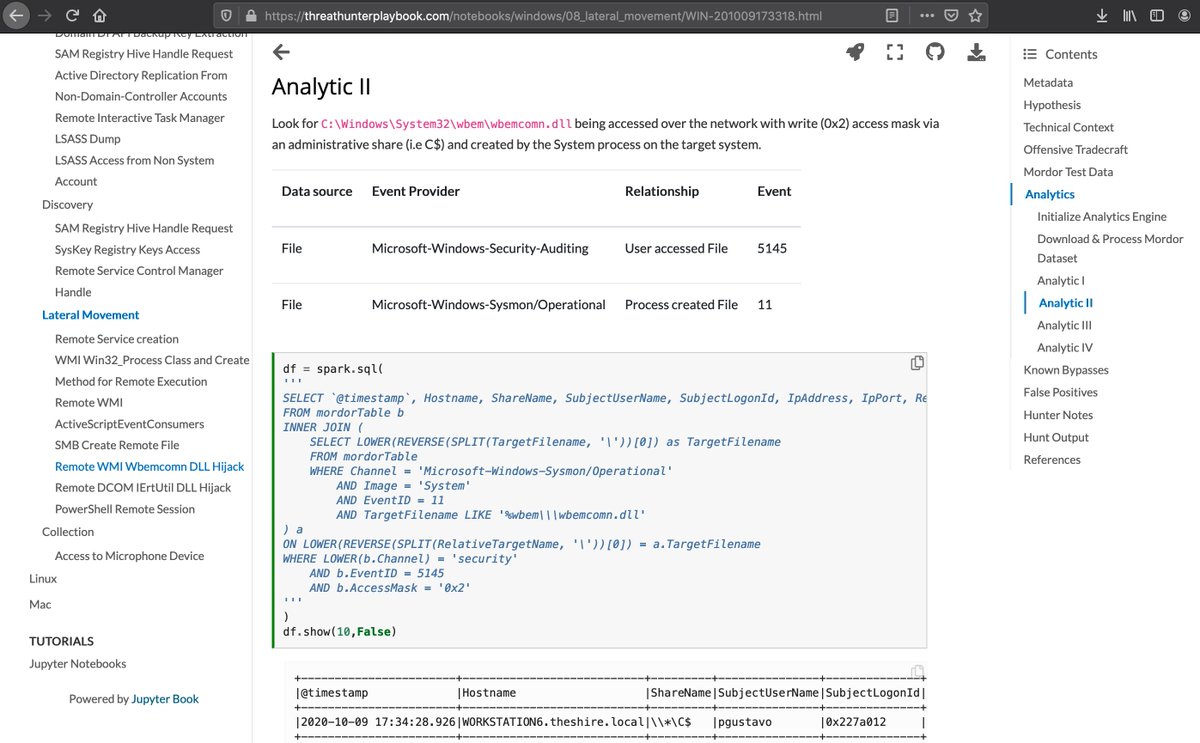
Check out mordordatasets.com/notebooks/smal… and threathunterplaybook.com/notebooks/wind… - Mordor Dataset and Playbook entry for wuauclt.exe abuse with many thanks to Roberto Rodriguez 🇵🇪 🤜 for his epic work as ever! Will be updating blog with these links too for reference 💪

HOW to contribute a @Mordor_Project dataset in 2 mins ⏳w/ the help of Red Canary, a Zscaler company ART & then contribute to sigma after exploring the data! Open Threat Research ♻️ Clear, Exec & Collect: youtu.be/6iteEfbuwU8 😈 Data: mordordatasets.com/notebooks/smal… 🏹 Rule: github.com/OTRF/sigma/blo…

If you are wondering what this might look like in Sysmon, we got you covered with a new small dataset. You can simply download it from the link below and explore it with PSH as shown in the second image below 😊 Thank you Johnny Shaw ! 😈 mordordatasets.com/notebooks/smal…



💥😱 James Forshaw added "named pipe RPC client transport" to NtObjectManager 🔥 Thank you very much James for all your work 👏! I'll create PS scripts to cover a few scenarios 🍻 (Img 4) If anyone would like to help me, let me know 😉 Open Threat Research github.com/Cyb3rWard0g/Wi…


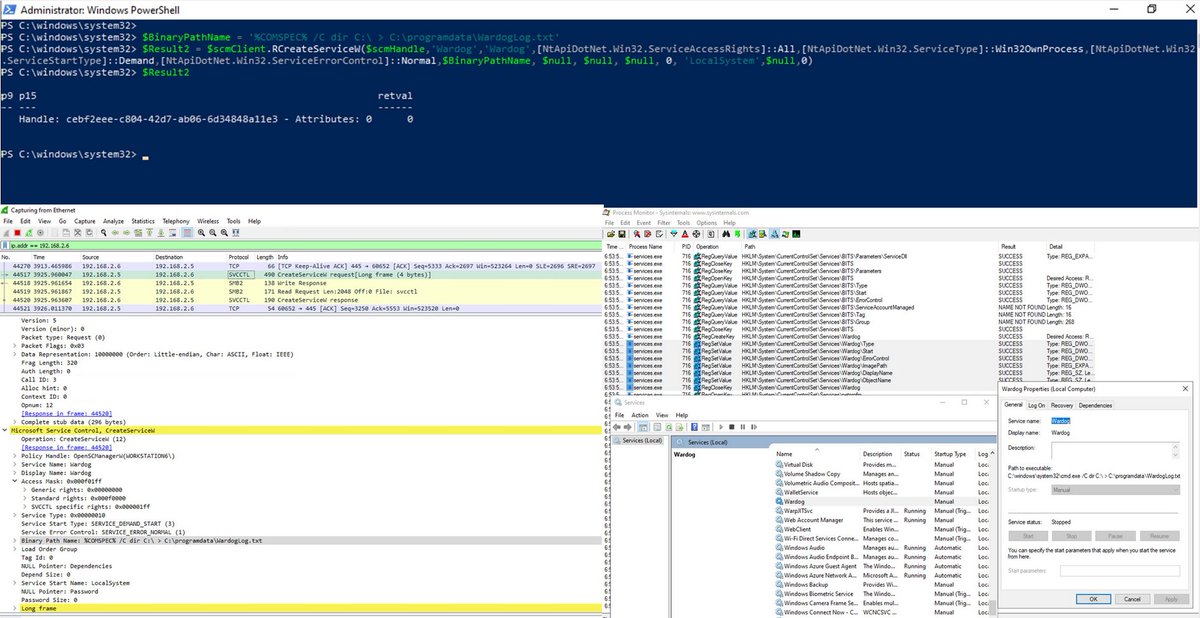
Looking for anything to do this weekend? 😉 🔥 A way to create and start services remotely using the amazing NtObjectManager from James Forshaw leveraging the latest support for named pipes RPC clients 🔥 Help us to create more PS scripts Open Threat Research blog.openthreatresearch.com/ntobjectmanage…

Now that #ProxyLogon POCs are public, help defenders learn the underlying behavior? The weekend isn't over yet! Roberto Rodriguez 🇵🇪 1⃣ Azure Sentinel Env: github.com/OTRF/Azure-Sen… 2⃣ Install 🐍, ⬇️ &💥 POC 4⃣ Share @Mordor_Project datasets, sigma rules, Project Jupyter notebooks
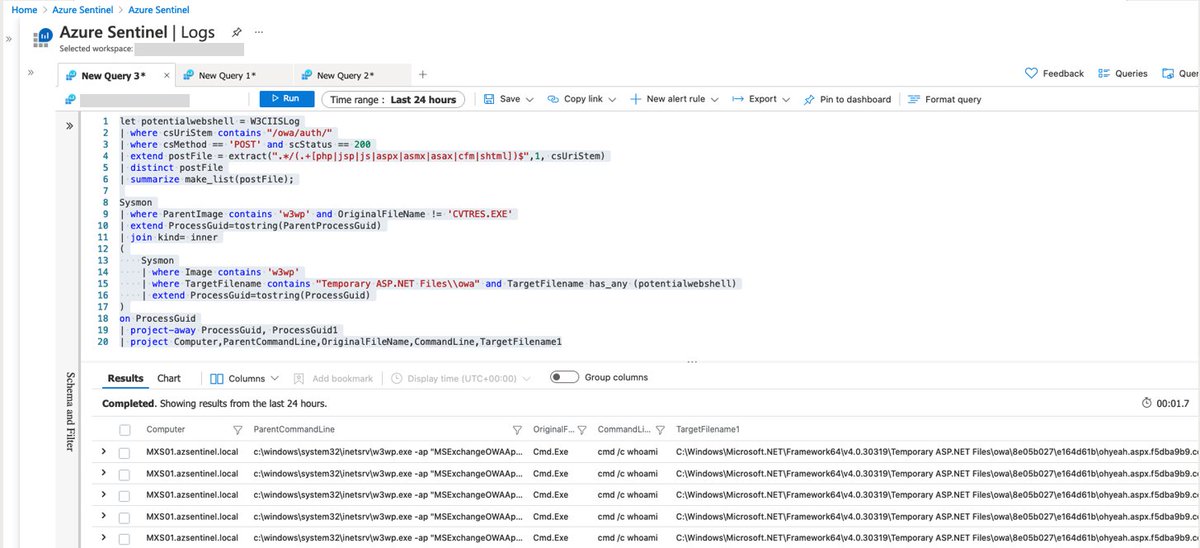
Roberto Rodriguez 🇵🇪 @Mordor_Project Open Threat Research sigma Project Jupyter Jack Halon Melvin langvik Mauricio Velazco CVE-2021-27065 - sigma rule to detect adversaries modifying the offline address book (OAB) virtual directory in Exchange and setting the ExternalUrl property to script. #ProxyLogon chain event PR: github.com/SigmaHQ/sigma/…


This morning Starship SN15’s nosecone is heading into the high bay. It appears that SpaceX is not wasting any time in preparing SN15 to roll to the launch site ASAP.🔥🚀🔥 NSF - NASASpaceflight.com


Sharing @Mordor_Project datasets for "Getting AD FS Database Config Remotely" (Security, Sysmon & PCAP) Roberto Rodriguez 🇵🇪 🍻🙏 mordordatasets.com/notebooks/smal… 1⃣ A few tool-based comments at the host level 2⃣ Group hosts & processes connecting to AD FS server over port 80 (Usually 443)


🚨 New version of the Windows Security Events connector from #AzureSentinel reached public preview Looking for a way to test & filter the collection of event logs via XPath queries? I got you! 💜🍻 Microsoft SIEM and XDR #MSTIC Open Threat Research OSSEM techcommunity.microsoft.com/t5/azure-senti…



🚨 Learning how to install #Sysmon for Linux 🐧 & send security events to #AzureSentinel in a research lab environment!! 🧪 #MSTIC #Microsoft 📡 Sysmon (SysinternalsEBPF) -> Syslog -> SIEM 🚀 ✅ Scripts ✅ ARM templates ✅ Sysmon configs and more.. techcommunity.microsoft.com/t5/azure-senti…

🚨 #InfosecJupyterthon going live 🔴 in 24hrs 😎 Dec 2nd and 3rd at 8:30 AM (PST) 🗓️ The agenda for this year is 🔥🔥 aka.ms/Jupyterthon202… Live Streams 📺(FREE virtual event) Day 1: aka.ms/Jupyterthon202… Day 2: aka.ms/Jupyterthon202… Open Threat Research #MSTIC #Jupyter 🙏



Thank you for sharing Dr. Nestori Syynimaa 😎! A process that is NOT Lsass attempting to access ("CloudDomainJoin" OR "WorkplaceJoin") AND "Ngc\KeyTransportKey" before exporting the Device certificate and transport key is interesting 😉 ✅ SACL ✅ Detection Idea: github.com/Azure/Azure-Se…