
Himash
@himashonline
Views expressed are my own
ID: 167371603
16-07-2010 12:19:43
543 Tweet
20 Takipçi
644 Takip Edilen






New Blog! And the first of a new ‘adversary infrastructure profile’ blog series I am starting with TEAM CYMRU 😁 I’ve shared an explanation of the types of infra routinely used by threat groups, as well as Team Cymru Scout queries for investigations: team-cymru.com/post/scattered…

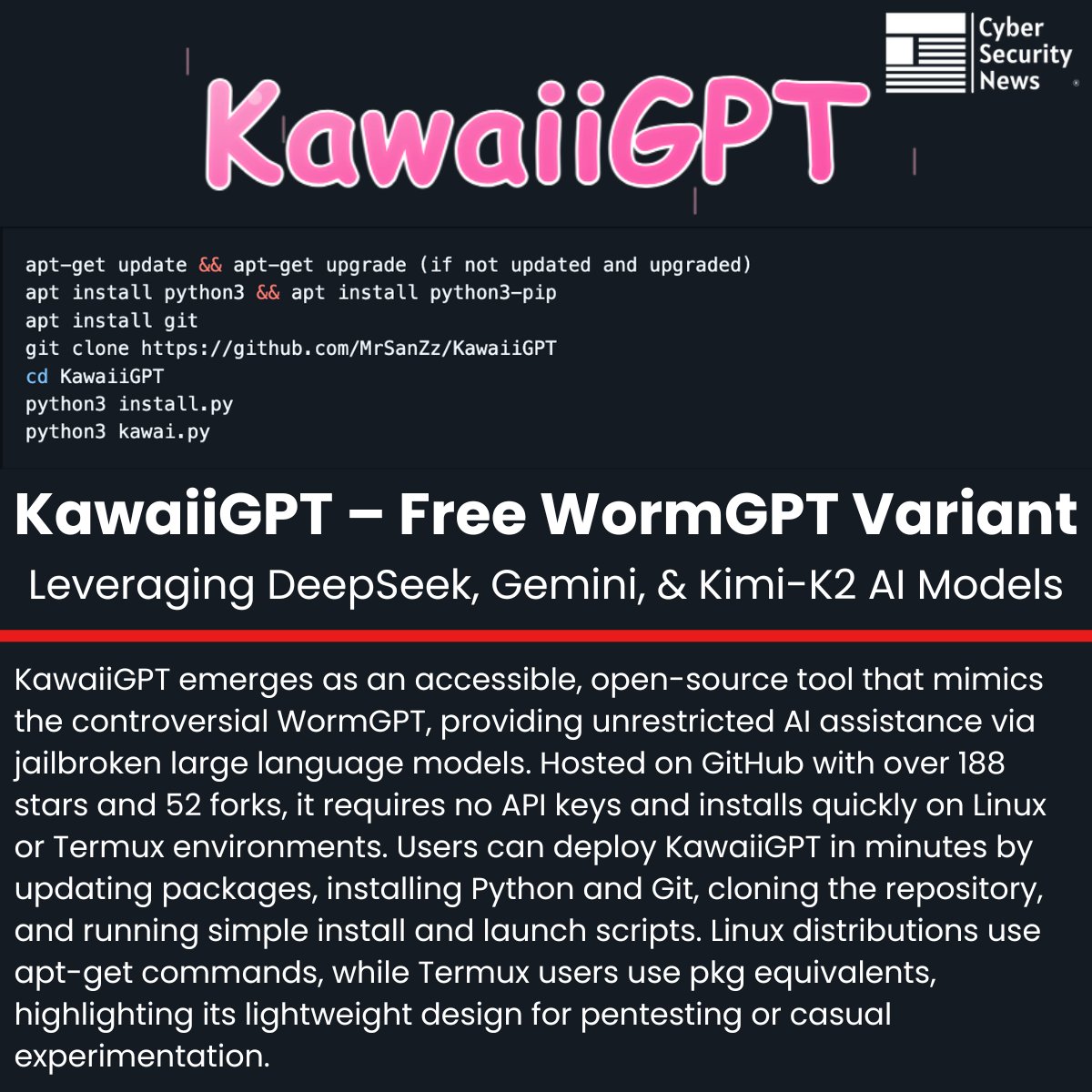
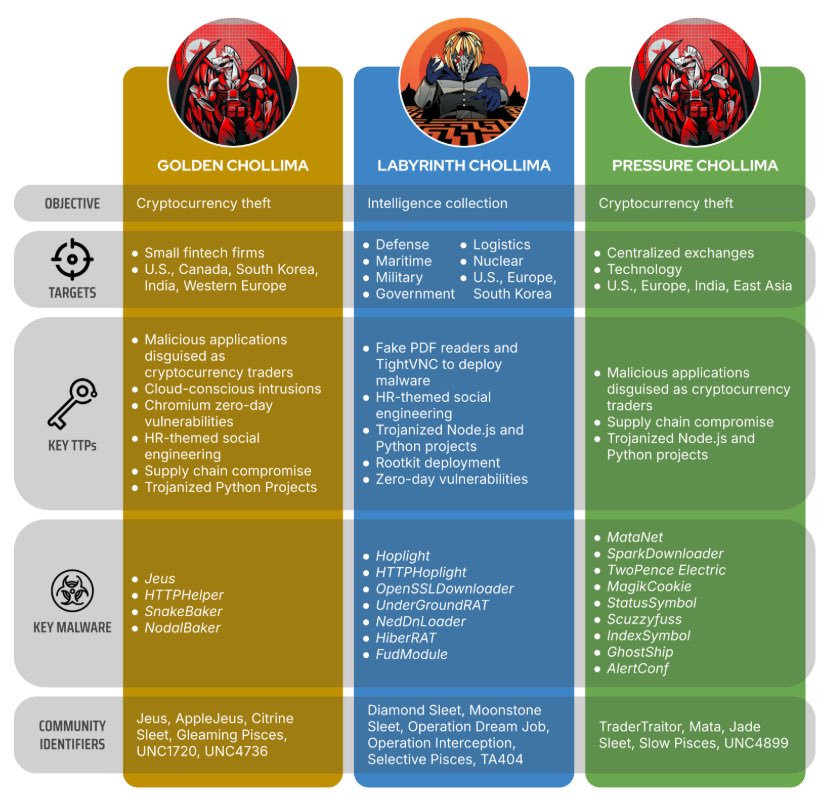
"PurpleBravo’s Targeting of the IT Software Supply Chain" published by Recorded Future. #BeaverTail, #ClickFix, #ContagiousInterview, #GolangGhost, #PurpleBravo, #PylangGhost, #DPRK, #CTI recordedfuture.com/research/purpl…





THE CHINESE GOVERNMENT USED MICROSOFT WARBIRD APIS FOR OBFUSCATION > proof-of-concept by Michael B. in 2023 > 30 stars on GitHub > 62 likes on Xitter This is fucking FIRE research. Insanely slept on research. I am FLABBERGASTED.










![Group-IB Threat Intelligence (@groupib_ti) on Twitter photo Infrastructure overlap confirms it: The #C2 server for GhostFetch (promoverse[.]org) shares HTML artifacts with a known MuddyWater domain from Oct 2025. Meanwhile, the HTTP_VIP C2 server stores victim geolocation and security products in a SQL DB. Read the full technical Infrastructure overlap confirms it: The #C2 server for GhostFetch (promoverse[.]org) shares HTML artifacts with a known MuddyWater domain from Oct 2025. Meanwhile, the HTTP_VIP C2 server stores victim geolocation and security products in a SQL DB. Read the full technical](https://pbs.twimg.com/media/HBmGtqeagAEEGio.jpg)

