Hacking the Cloud
@hackingthcloud
The official Twitter account for Hacking the Cloud, the open-source encyclopedia of offensive security techniques in the cloud. Created by @frichette_n
ID: 1754918175991267328
https://hackingthe.cloud/ 06-02-2024 17:21:54
89 Tweet
210 Followers
1 Following



Want to learn more about Administrative Unit attack paths in Azure? Check out Katie Knowles's talk about it from SpecterOps Con! youtube.com/watch?v=oxD7-U…
👾 It's up!! Everything you ever wanted to know about Entra Administrative Unit attack paths, from my talk at SpecterOps SO-CON: youtube.com/watch?v=oxD7-U…


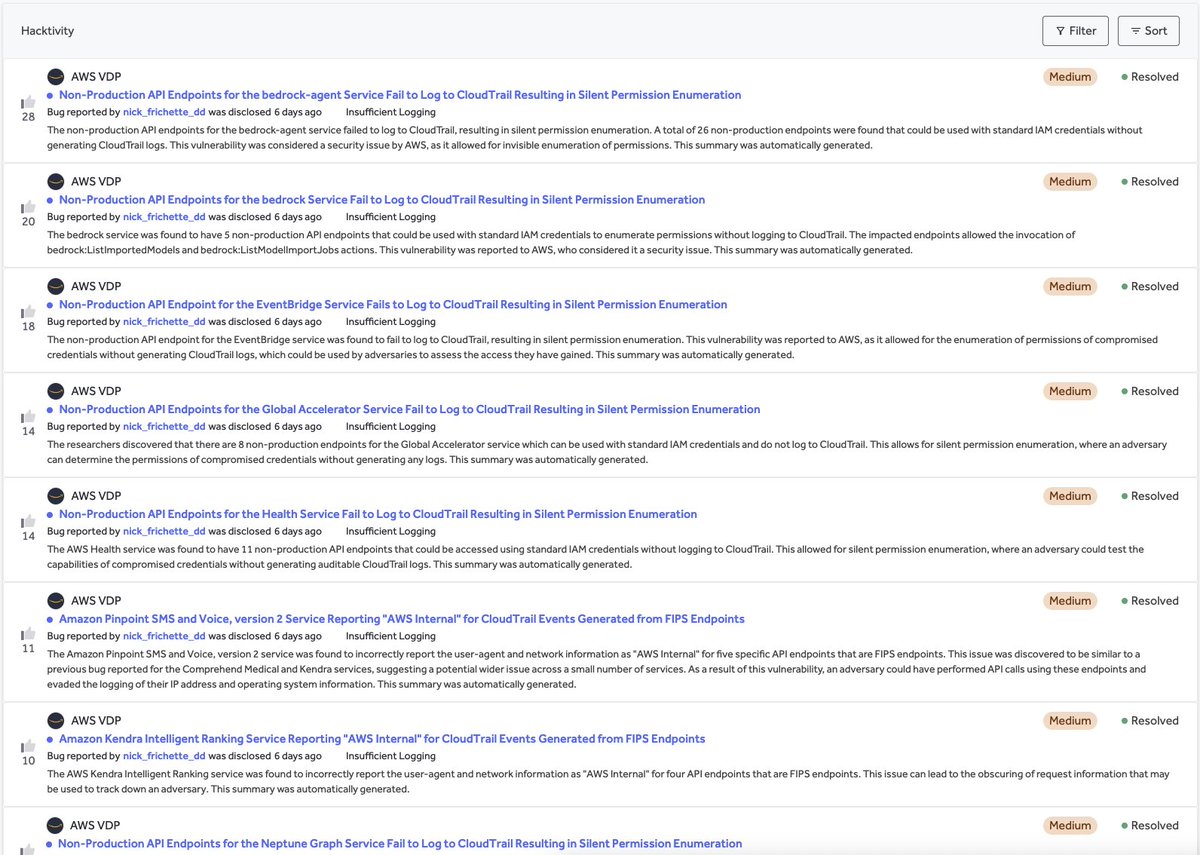
🤩 I just came across this fascinating talk by Nick Frichette at fwd:cloudsec: “Hidden Among the Cloud: A Look at Undocumented AWS APIs.” youtube.com/watch?v=f7AuDx…





Safe travels to everyone coming to fwd:cloudsec! It’s the densest concentration of cloud security nerds in the world!

It’s a month and a half away but I’m already super excited for fwd:cloudsec EU! If you’ll be there in Berlin, come find me for limited edition, holographic, Hacking the Cloud stickers!


Cloud attackers keep evolving. So should defenses. Enumeration through AWS Resource Explorer used to be invisible. Not anymore. Breakdown from Datadog, Inc.: securitylabs.datadoghq.com/articles/enume…
Great write up from the Cyber Security News on our latest open-source tool, #Inboxfuscation, in their newsletter today. "A new open-source tool named Inboxfuscation can create malicious inbox rules in Microsoft Exchange that are difficult for security tools to detect. Developed by

New on Hacking the Cloud! A great post by Federico Lucini on bypassing AWS Network Firewall egress filtering! hackingthe.cloud/aws/post_explo…


After years of hacking on Azure it feels great to finally get 1st 🥇 Thanks Microsoft Security Response Center ❤️