H2Lab
@h2lab_org
H2Lab is a hardware harcking association targetting IoT and embedded devices security and design
ID: 1219329837107642369
https://www.h2lab.org 20-01-2020 18:45:02
153 Tweet
255 Followers
116 Following


[Tool] Ghidralligator: Emulate and fuzz code running on various CPU architectures (ARM, MIPS, PPC, x86, Apple Silicon M1/M2...) Based on #GHIDRA (libsla C++). #AFLplusplus, snapshot fuzzing, code coverage, ASAN cyber.airbus.com/17300/ github.com/airbus-cyber/g… GuillaumeOrlando



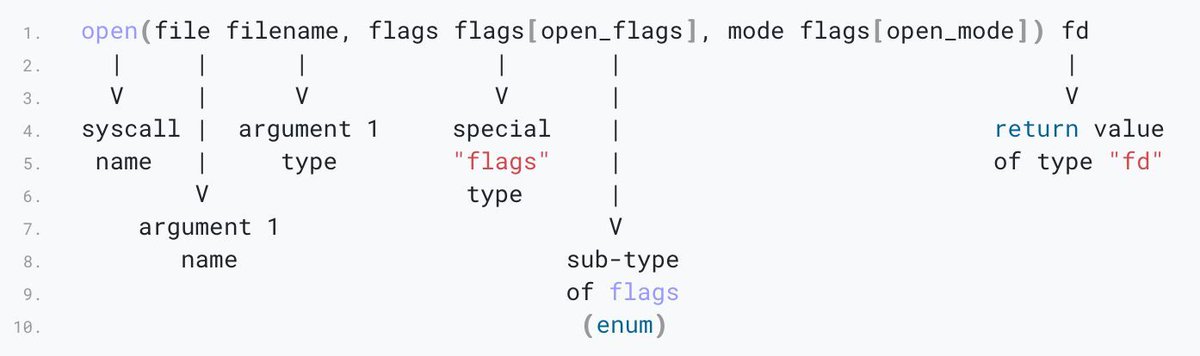
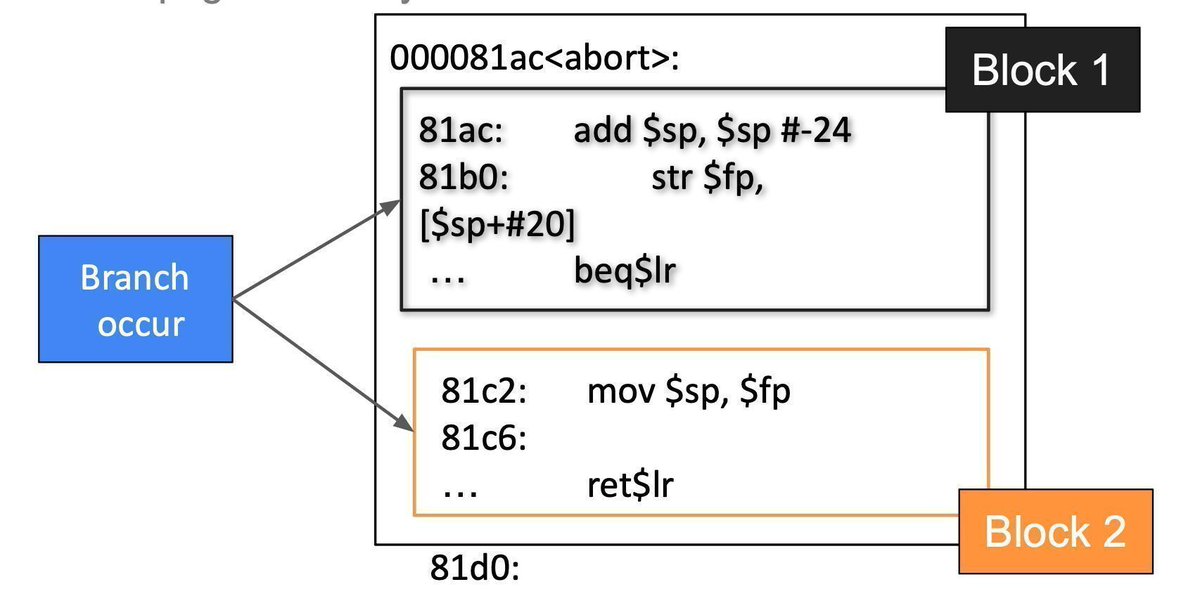
Bare metal firmware reverse engineering Introduction series by Ragnar Security Part 1: ragnarsecurity.medium.com/reverse-engine… Part 2: medium.com/geekculture/re… Part 3: medium.com/geekculture/re… #iot #embedded #reverseengineering #infosec #cybersecurity



Excellent collection of material for learning a bit about QEMU internals Credits Airbus Security Lab airbus-seclab.github.io/qemu_blog/ #qemu #emulation



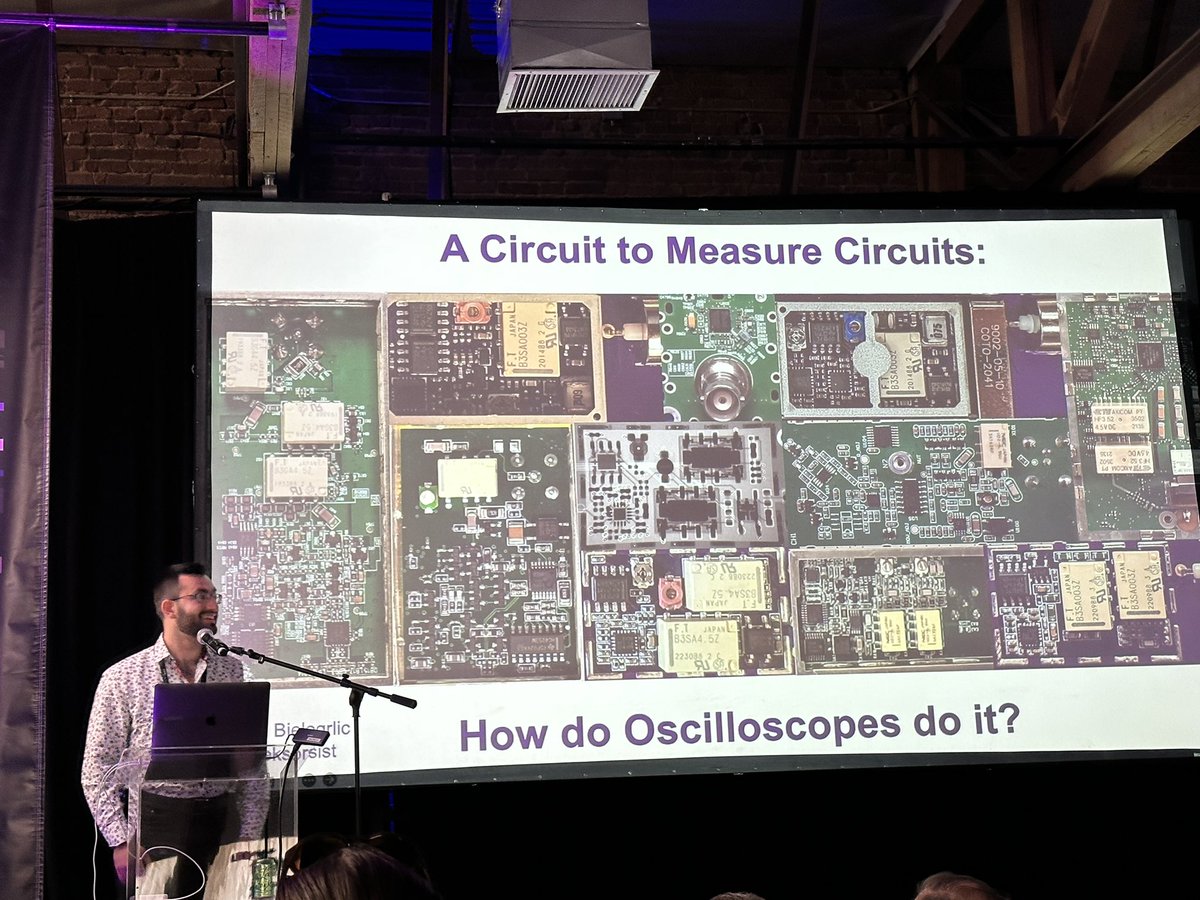
blackhat.com/us-23/briefing… Why testing fault injection attacks on integrated circuits matters? ⚡️🚗🔐 At BlackHat 23, a research team from TU Berlin: Christian (Christian Werling), Niclas, Hans and Oleg will show voltage glitch attack against AMD Secure Processor (ASP) used in Tesla cars!



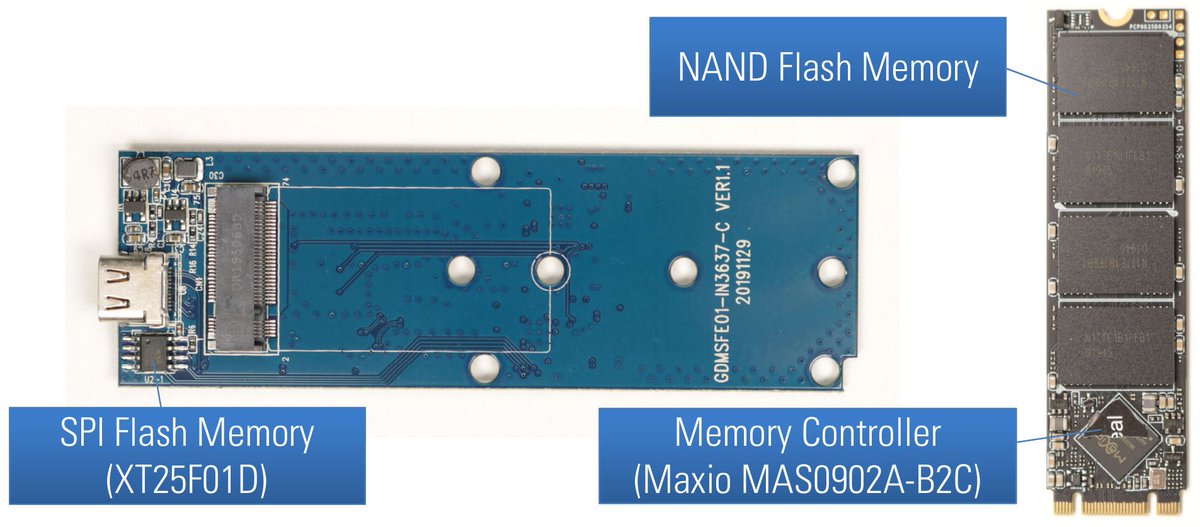
Reverse engineering of USB flash drives with AES hardware encryption Credits Matthias Deeg blog.syss.com/posts/hacking-… blog.syss.com/posts/hacking-… #embedded #hardware #infosec #cybersecurity






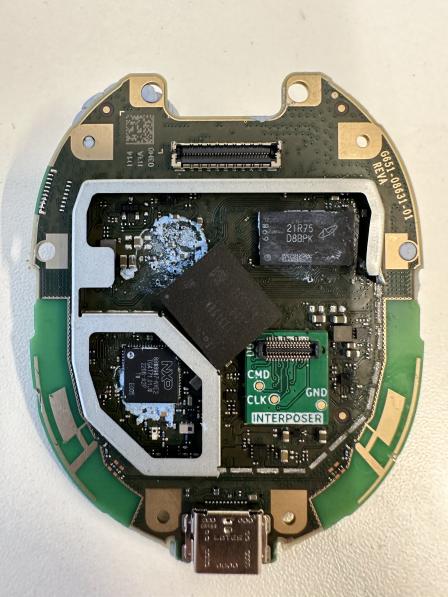
Today thanks to Twisted Wires and Mathieu RENARD we have launched a new production batch for our LEIA board! #smartcard #PowerAnalysis #glitching #ChipWhisperer . Pre-Order: shop.h2lab.org #EMVco #IPTV #ITSEF #SetTopBox