Gh05T50litary
@gh05t50litary
ID: 1074667714411548673
17-12-2018 14:08:44
185 Tweet
8 Followers
343 Following





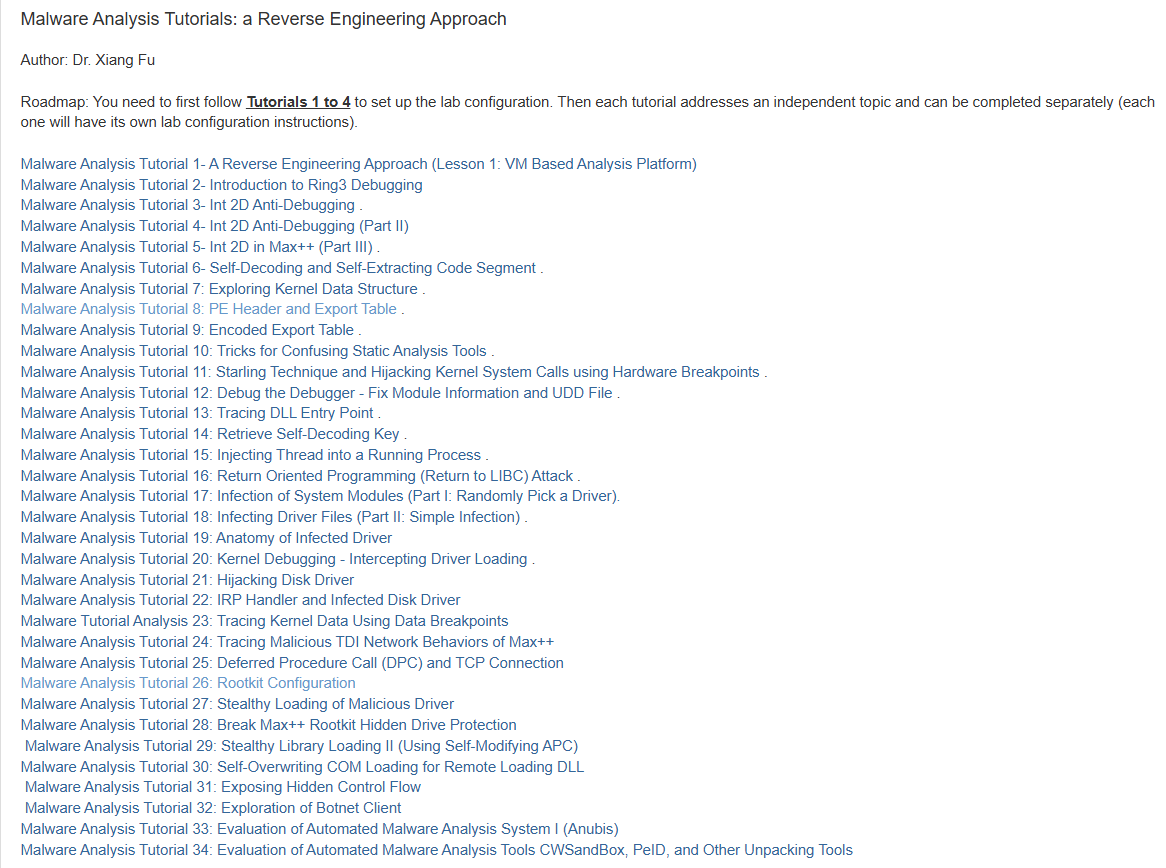
AV/EDR Lab Environment Setup A curated list of various resources helpful in building own malware-centric research lab. A post by Udayveer Singh (Udayveer Singh) Source: an0nud4y.notion.site/AV-EDR-Lab-Env… #redteam #blueteam #maldev #malwaredevelopment





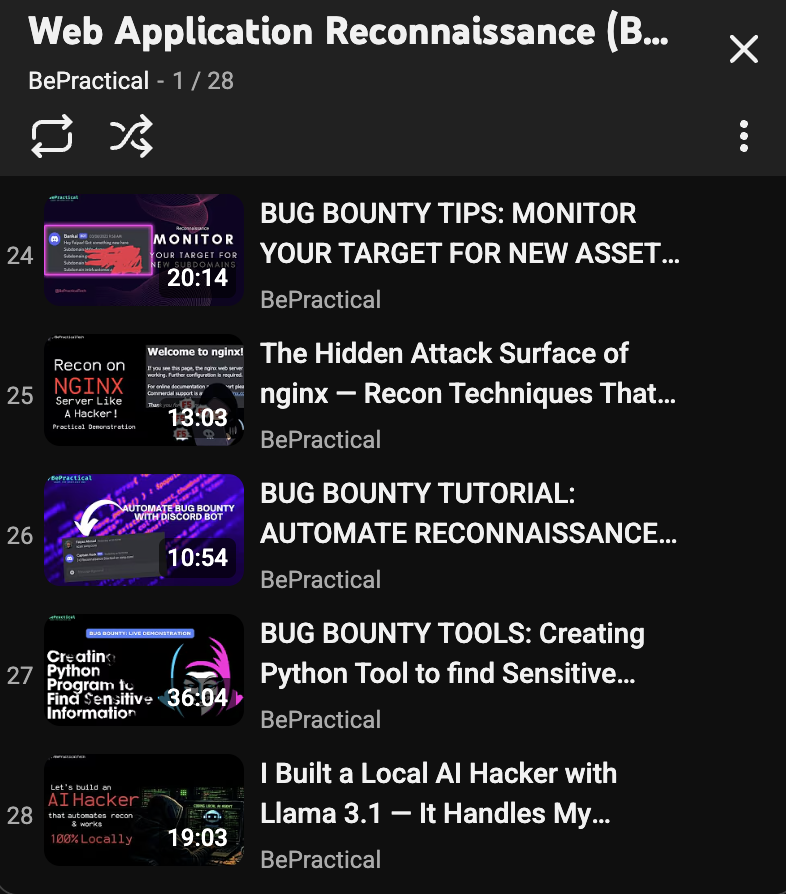
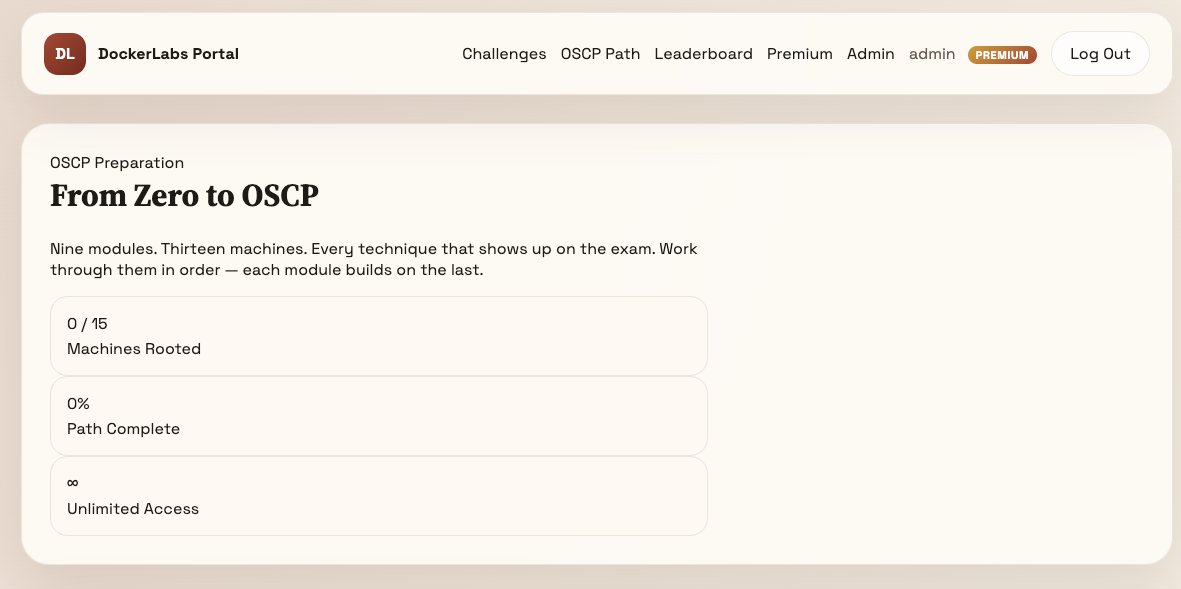
OSCP LIVE DEMO OffSec Live: Active Information Gathering OffSec Live: Passive Information Gathering OffSec Live: Web Application Attacks OffSec Live: Live Terminal Sessions OffSec Live: SQL Download Link: mega.nz/folder/kykEDaJ… Follow kelvinlina𖤍💜✨ for more