🔥 Fire Hunter 🔥
@fireh7nter
Enthusiastic about #infosec #security #offensive
Cyber Security Consultant at @niiconsulting
Tweets are my own
ID: 1078598905
https://fireh7nter.com/ 11-01-2013 05:33:28
3,3K Tweet
314 Followers
1,1K Following

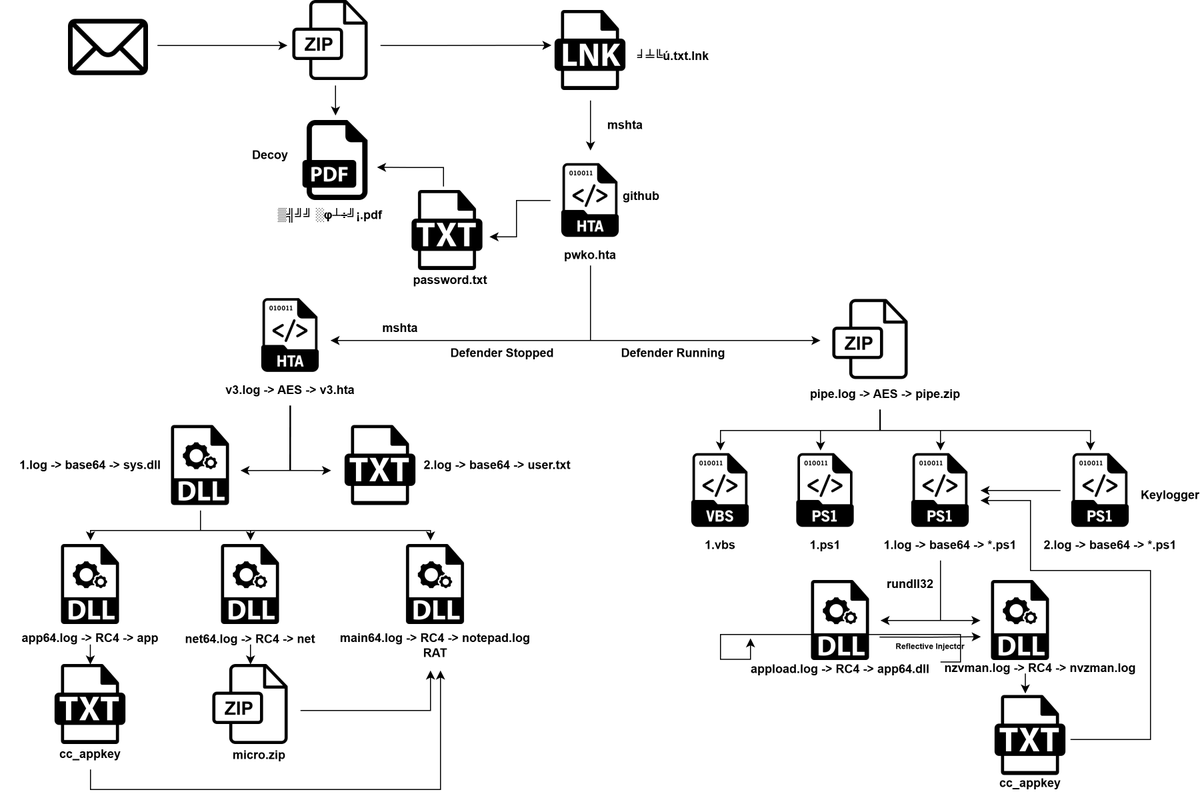
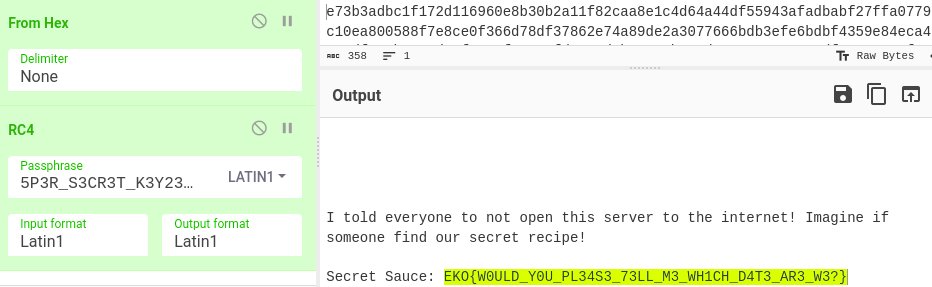
My write-up for the Kaspersky challenge from Ekoparty | Hacking everything #CTF is online. This was very nice challenge - #network traffic analysis, exploitation, #malware, #reverseengineering and #crypto malwarelab.eu/posts/ekoparty… #EKOPARTYCTF #networksecurity #malwareanalysis #cyberchef

Toyota confirms breach after Medusa ransomware threatens to leak data - Bill Toulas bleepingcomputer.com/news/security/… bleepingcomputer.com/news/security/…


For anyone interested in learning Windows binary reverse engineering, these are excellent resources by Alexandre Borges (Alexandre Borges) Article 01: exploitreversing.files.wordpress.com/2023/04/exploi… Article 02: exploitreversing.files.wordpress.com/2024/01/exploi… #infosec #windows
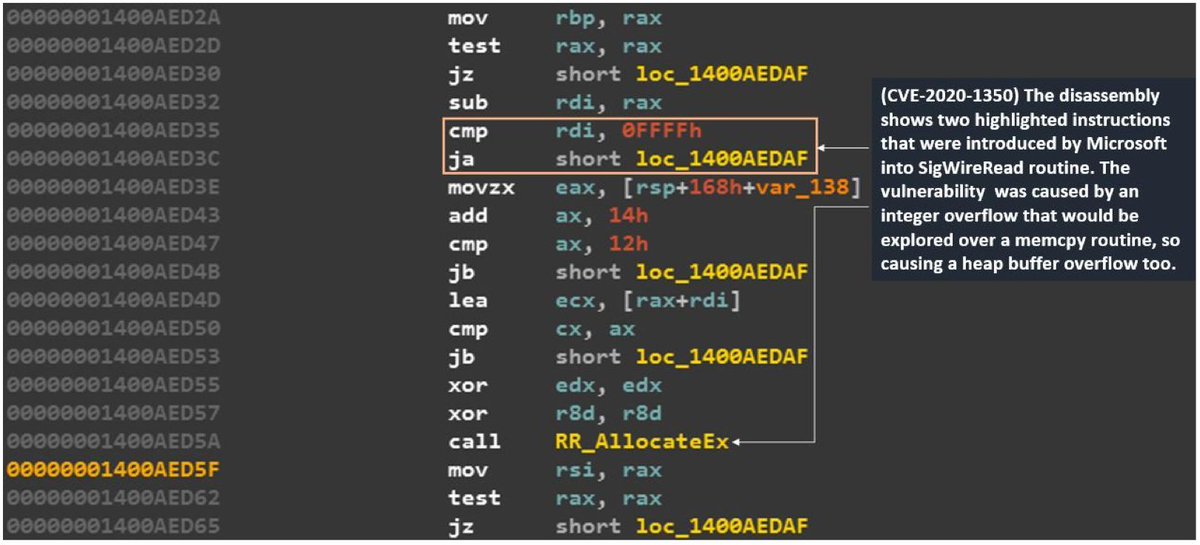













𝗘𝗫𝗣𝗟𝗢𝗜𝗧 𝗗𝗘𝗩𝗘𝗟𝗢𝗣𝗠𝗘𝗡𝗧 🐌 🔗 Part 1 : Intro :- 0xninjacyclone.github.io/posts/exploitd… 🔗 Part 2 : Understanding Stack Memory :- 0xninjacyclone.github.io/posts/exploitd… 🔗 Part 3 : Understanding Heap Memory :- 0xninjacyclone.github.io/posts/exploitd… 🔗 Part 4 : Understanding Binary Files :-