Famous
@famous_a_a
Cybersecurity in progress 💻 | Chelsea forever 💙 | Crypto believer | Documenting the grind
ID: 1077597724822917125
25-12-2018 16:11:33
6,6K Tweet
329 Followers
1,1K Following





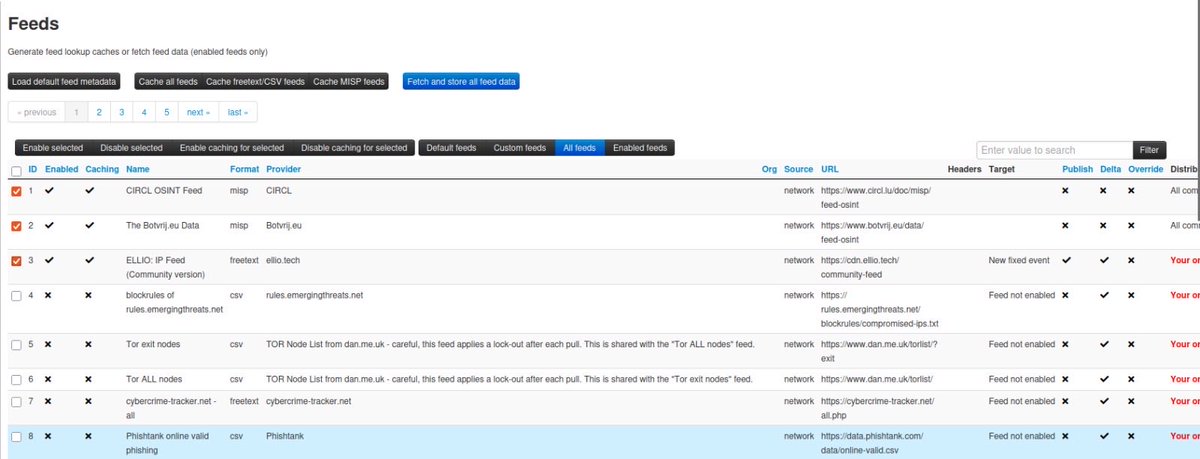
#BlueTeamer #100DaysOfCybersecurity Day 99 In preparation for the task ahead, I completed some basic rooms on LetsDefend ; IT Security basics for Corporate VirusTotal for SOC Analyst How to investigate a SIEM alert and Cyber Threat Intelligence zʇunH ʎɐſ ɐsɐɟnW 🦁🦁🦁🦁 Dr Iretioluwa Akerele Cisco Nerd





I just completed my 100 Days of Cybersecurity challenge. Big thanks to my accountability partner Famous for the check-ins and support, really helped me stay on track. Showing up every day was not always easy, but I did it. Dr Iretioluwa Akerele Temitope Sobulo🛡️ Ṣẹ́gunfúnmi😎 zʇunH ʎɐſ ɐsɐɟnW 🦁🦁🦁🦁





Day 100/100 🔥🔥🔥 #100DaysOfCyberSecurity Ended my day with Community meeting on how to Position yourself on LinkedIn for Job opportunities Hosted by Chinelo Olebunne DsL_a ʚїɞ ® zʇunH ʎɐſ ɐsɐɟnW 🦁🦁🦁🦁 Ṣẹ́gunfúnmi😎