Przemek Skowron
@evilrez
Move && Eat && Hunt && Repeat. My tweets are my own.
ID: 37994501
https://linkedin.com/in/pskowron 05-05-2009 19:13:37
1,1K Tweet
943 Followers
2,2K Following


🚨#cti #jobs #hiring 🚨We are looking for folks to join the brand new Client & Third Party Intelligence team at Standard Chartered. Please see the details below :) This is a very exciting opportunity for analysts who would like to have the best of both worlds:

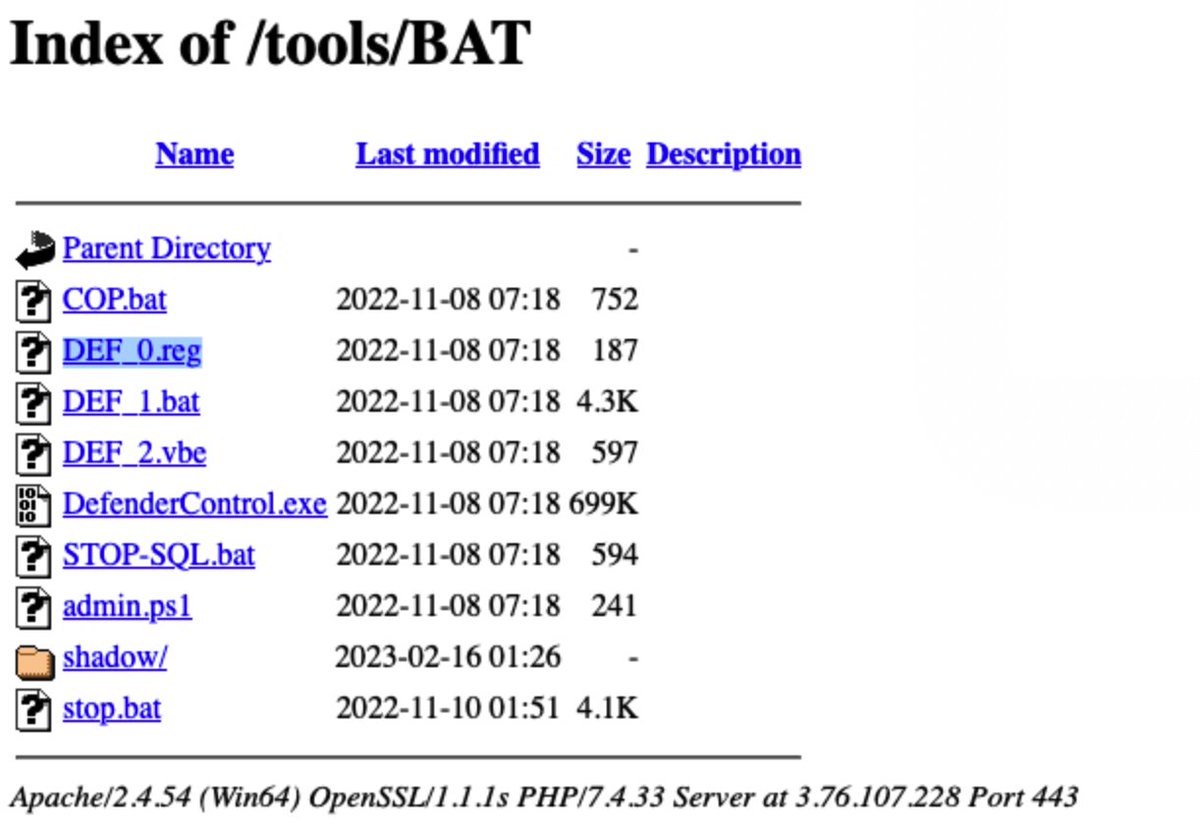
Next week, we're excited to add several new modules/lessons, bringing our March total to around 37 lessons. Want to access this training for free? academy.intel-ops.io/courses/huntin… Simply repost, like, and share in the comments how this training could benefit your career or day-to-day