Dmitriy Evdokimov
@evdokimovds
Оbservability, visibility, security of containerised apps and K8s. eBPF fan.
ID: 120566960
06-03-2010 21:13:12
2,2K Tweet
4,4K Followers
995 Following


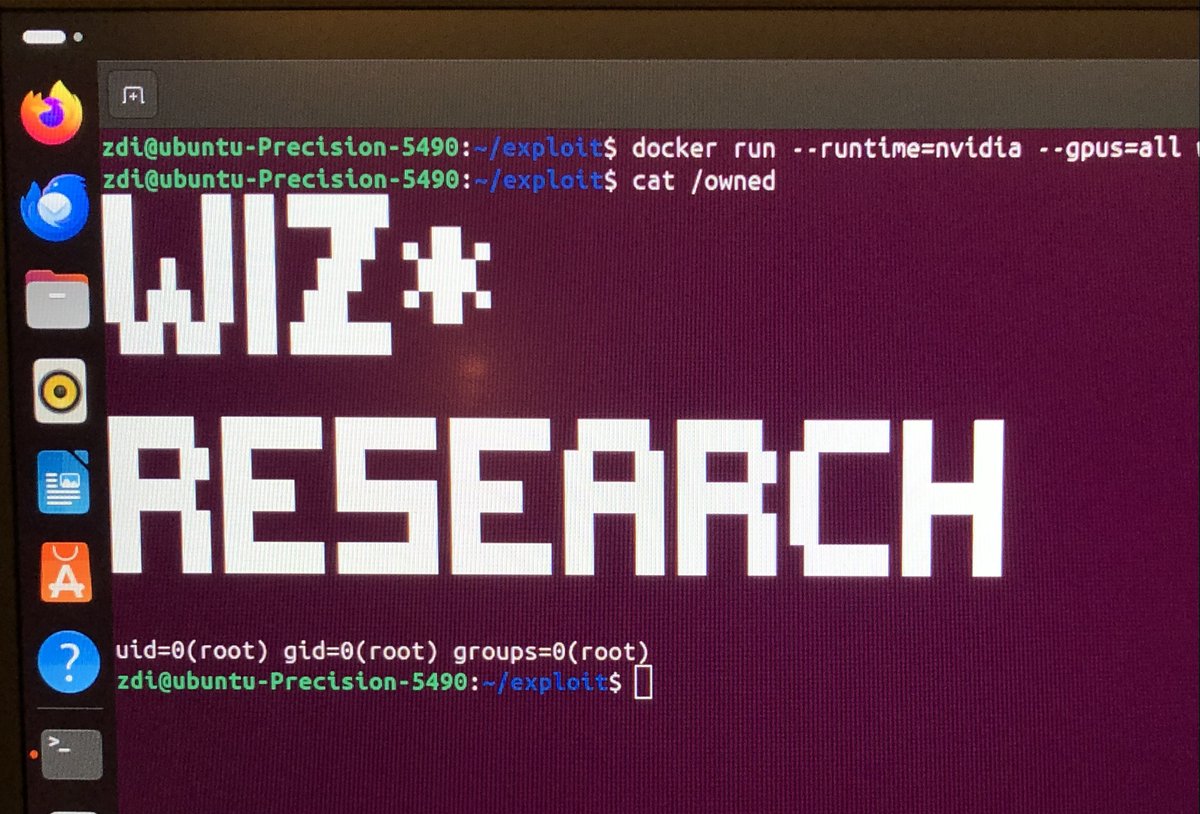
I tried my hand at exploiting an nday on the Google Container Optimized OS instance in kCTF but sadly was very late to the party. Here is my exploit write-up for it. I learned a lot during the process, let me know what you think. I'll post TL;DR in thread h0mbre.github.io/Patch_Gapping_…



Here are my slides from BSides Reykjavik * Backdooring a container image (Vault) * Exfiltrate secrets via DNS * Update to pillage registry tool (originally created by Josh Makinen) canva.com/design/DAGgrY1…


My keynote at offensivecon 2025, "How Offensive Security Made Me Better at Defense": Video: youtu.be/60BcjiChncE Slides: docs.google.com/presentation/d…














The 1st alpha of OpenTelemetry eBPF instrumentation (OBI) is live 🎉 Originally Grafana Beyla, OBI brings zero-code, zero-downtime telemetry to any app. Read the blog post: opentelemetry.io/blog/2025/obi-…