Grace
@euphoricfall
Cofounder @pulsedive cybersecurity #threatintel | watercolorist | hyperserious board gamer | still borrows books from the public library
ID: 1159431794187493376
08-08-2019 11:50:55
1,1K Tweet
1,1K Followers
1,1K Following









We're tracking the new DodgeBox (loader) & MoonWalk (backdoor) tools researched by the Zscaler ThreatLabz team as related threat pages in our free Community Platform. DodgeBox: pulsedive.com/threat/DodgeBox MoonWalk: pulsedive.com/threat/MoonWalk APT41: pulsedive.com/threat/APT41



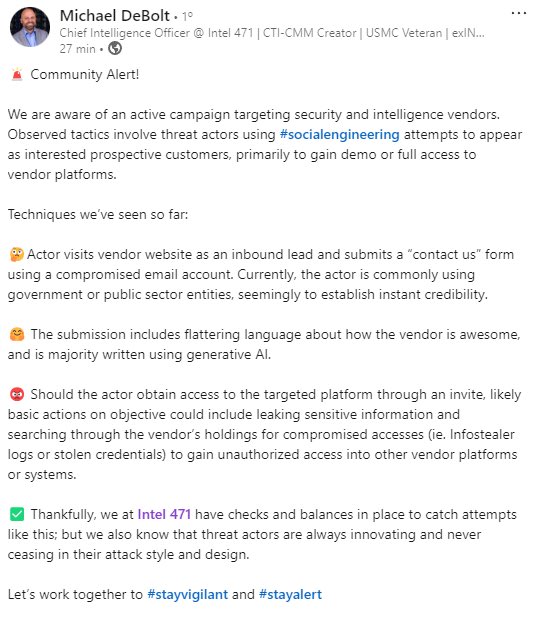
PSA from the Curated Intelligence Community to the CTI industry — watch out for cybercrime groups seeking access to your vendor platforms ⚠️

I'm coming for you #BSidesNYC



Community Resource Share: Curated Intelligence's CTI Research Guide curatedintel.org/2024/10/the-ct… Start with this guide if you're finding it difficult to consistently and appropriately perform intelligence collection for your stakeholders.