Gordon Long
@ethicalhax
Founder, Researcher, Red Teamer, History Nerd
ID: 1031545684372144128
20-08-2018 14:17:11
92 Tweet
144 Takipçi
90 Takip Edilen

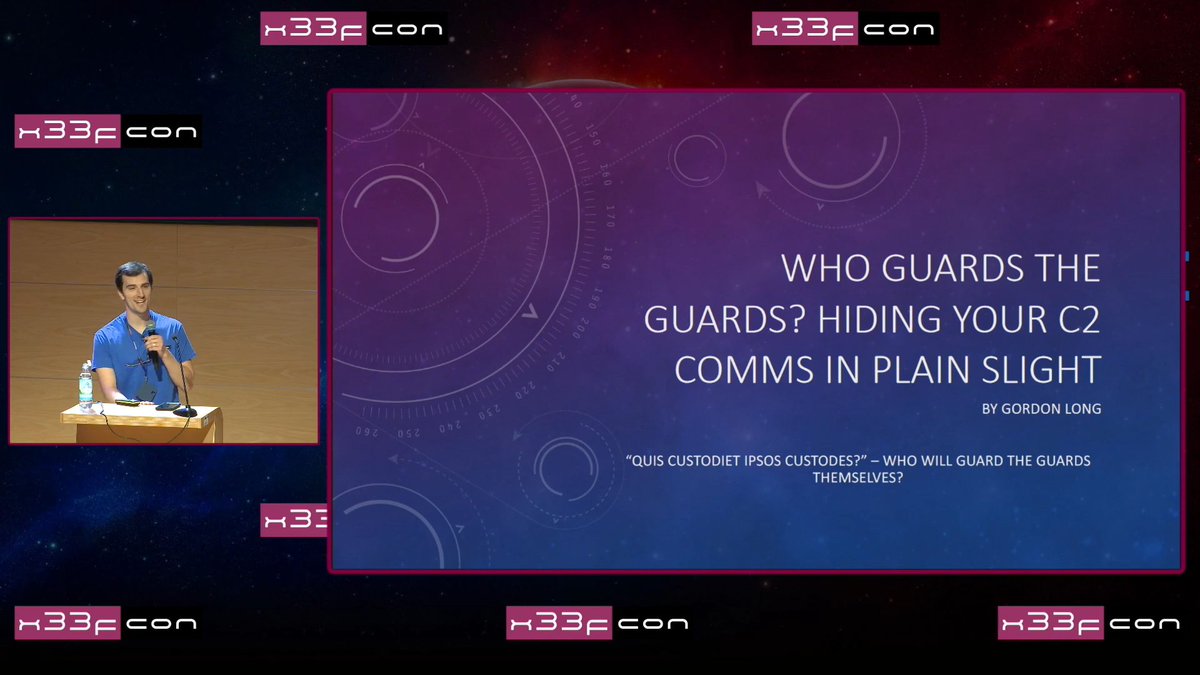
Unlock the secrets of hiding C2 communications in plain sight on Windows! Join Gordon Long's talk at #x33fcon where he'll delve into new research and techniques for stealthy C2 design. Don't miss out! More info: x33fcon.com/#!s/GordonLong…



🆕🍎In the heat of WWDC week, I'm releasing a writeup about a new persistence method I was investigating on macOS. Widgets. I also wrote a few tools which can be used for widget forensics and also some limited offensive tooling. Links in the blog post. theevilbit.github.io/beyond/beyond_…

We just learned how to hide #C2 in plain sight, Who Guards the Guards? talk by Gordon Long at #x33fcon #EDR #redteam


#x33fcon 2024 interviews are ready. Shorter ones will be published on X. All on YT and linkedin. We are starting from Gordon Long

I had such a great time presenting /ˈziːf-kɒn/ last month! Great to meet so many new folks and make some friends. I am releasing my PoCs for the two techniques I spoke about at x33fcon, Guard Comms and Guard Stomping. Check out github.com/asaurusrex/Gua…, presentation slides included!



I was rather skeptical that this wasn't an elaborate joke, but yes, CrowdStrike has apparently emailed its customers & offered a ~$10 UberEats gift card/coupon for any "inconvenience" ...and yes, it errors out when one goes to redeem it, saying it has been cancelled 🫠


Happy to announce I’ve been accepted to speak at Security BSides Northern Virginia 🥳. Come check out my talk on some MacOS bugs: bsidesnova2024.sessionize.com/session/712965