Ennkasa
@ennkasa
Ennkasa
ID: 1425206272631222278
10-08-2021 21:24:07
922 Tweet
116 Followers
412 Following

Expert Witness- Nana Sei Anyemedu Fails to deliver - Getting the Right Info for your Digital Forensics Journey x.com/i/spaces/1kvJp…
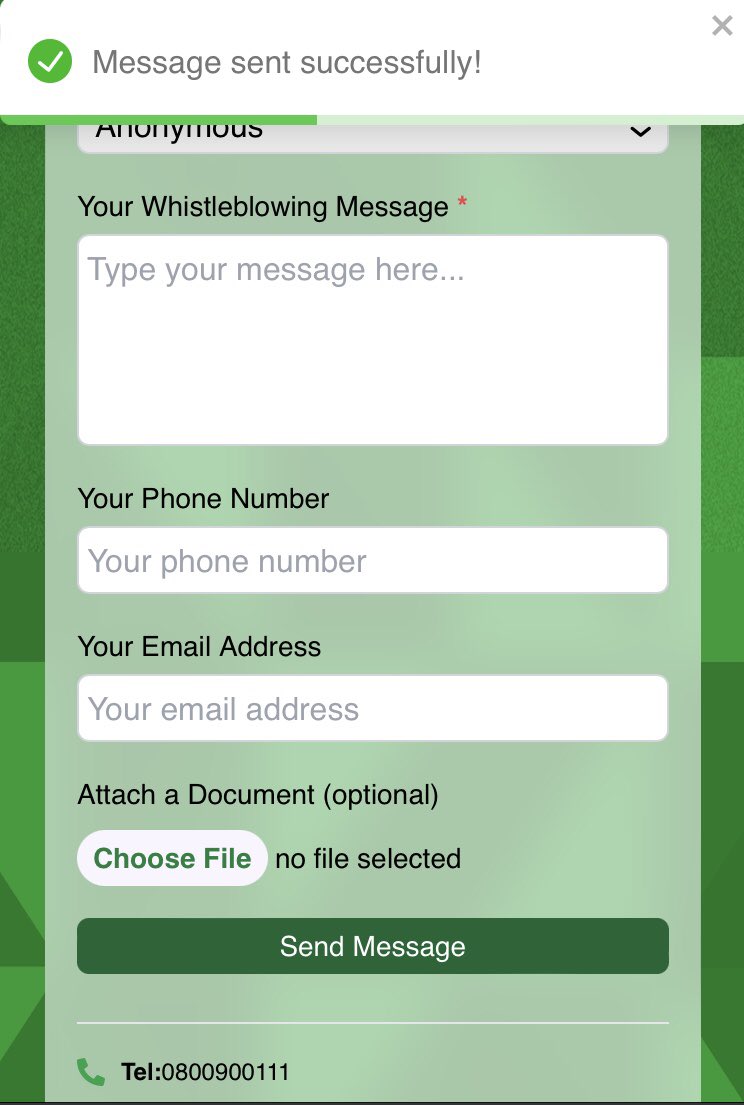
CYBER INTEGRITY 7/19/24: Pic1-Dunstan Guba breaks the news of a DVLA web subdomain hack. Pic2-A "pentester" posts the same story, citing Dunstan Guba's IG as the source. 7/21/24: Video-This "pentester" claims on a spaces, a mysterious "FBI" friend tipped him off a day earlier 🤔
A MUST WATCH: Ryan M. Montgomery on PBD Podcast. youtu.be/3_tZ7i1j3Tg?si…


Cisco Data Breach – Authenticity of 4.45GB Data Leak Confirmed! cybersecuritynews.com/cisco-data-aut… #Cisco #vulnerability #2fa #RCE #ZeroTrust #ZeroDay #cybercrime #hacker #privacy #APT #bot #CISO #DDoS #hacking #phishing #CyberAttack #cybersecurity #Security #infosec #AppSec #CyberSec



I wrote an Article several years ago about Cellebrite UFED Reader (UFDR) reports entitled "You Don't Know What You're Missing." Following up from a recent post about the practice of "pump & dump" which garnered a lot of comments, I wanted take these two points and illustrate





Let's run the Entire Internet on our laptop 😂 ≈ 1,000,000 BGP routes in his lab 😀 #Sponsored #ccna #docker #bgp #ccnp #ccie Cisco Live EMEA Cisco Learn with Cisco Ralph 🐘 @[email protected]