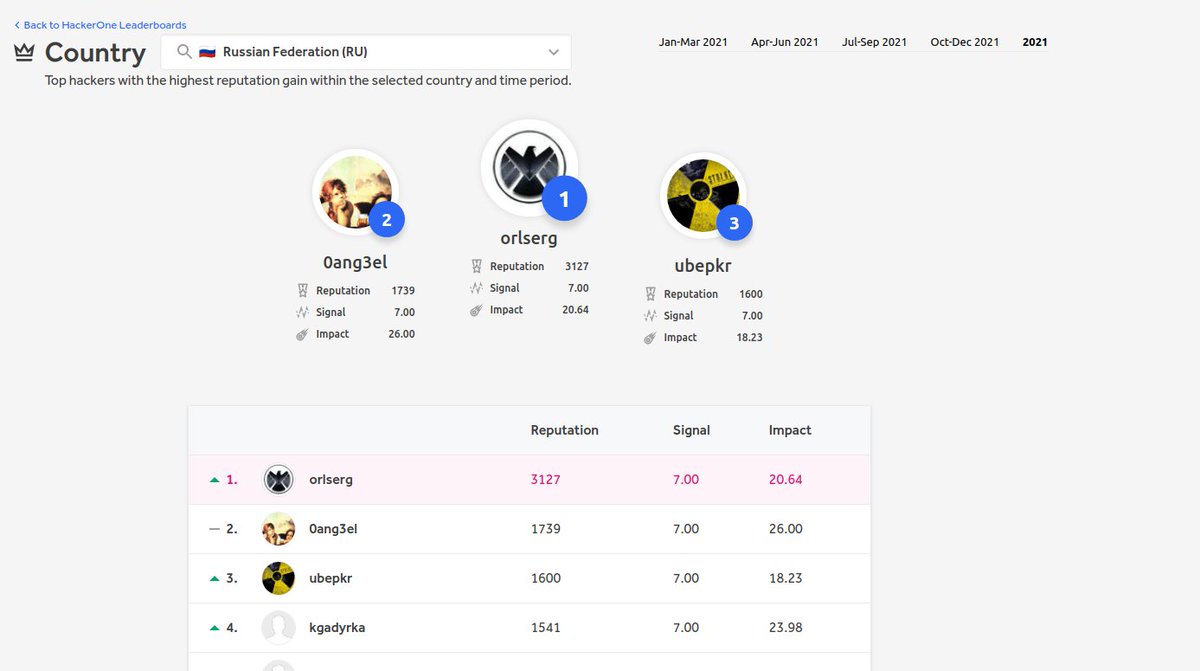
Sergey
@or_serg
HackerOne hackerone.com/orlserg, prev @Robocash1, @replit
ID: 1956592988
12-10-2013 12:50:47
41 Tweet
13 Followers
48 Following

xargs -a domain -I@ -P500 sh -c 'shuffledns -d "@" -silent -w words.txt -r resolvers.txt' | httpx -silent -threads 1000 | nuclei -t /root/nuclei-templates/ -o re1 💀 Nuclei by ProjectDiscovery ProjectDiscovery #bugbounty #bugbountytips









Articles worth reading discovered last week: 🗞 blog.pksecurity.io/2023/01/16/202… 🗞 about.gitlab.com/blog/2023/01/2… 🗞 blog.viettelcybersecurity.com/saml-show-stop… 🗞 synacktiv.com/sites/default/… 🗞 blog.assetnote.io/2023/01/24/yel… 🗞 pathonproject.com/zb/?196945362f… 🗞 github.blog/2023-01-27-byp… #PentesterLabWeekly




I recently developed and posted about a technique called "First sequence sync", expanding James Kettle's single packet attack. This technique allowed me to send 10,000 requests in 166ms, which breaks the packet size limitation of the single packet attack. flatt.tech/research/posts…



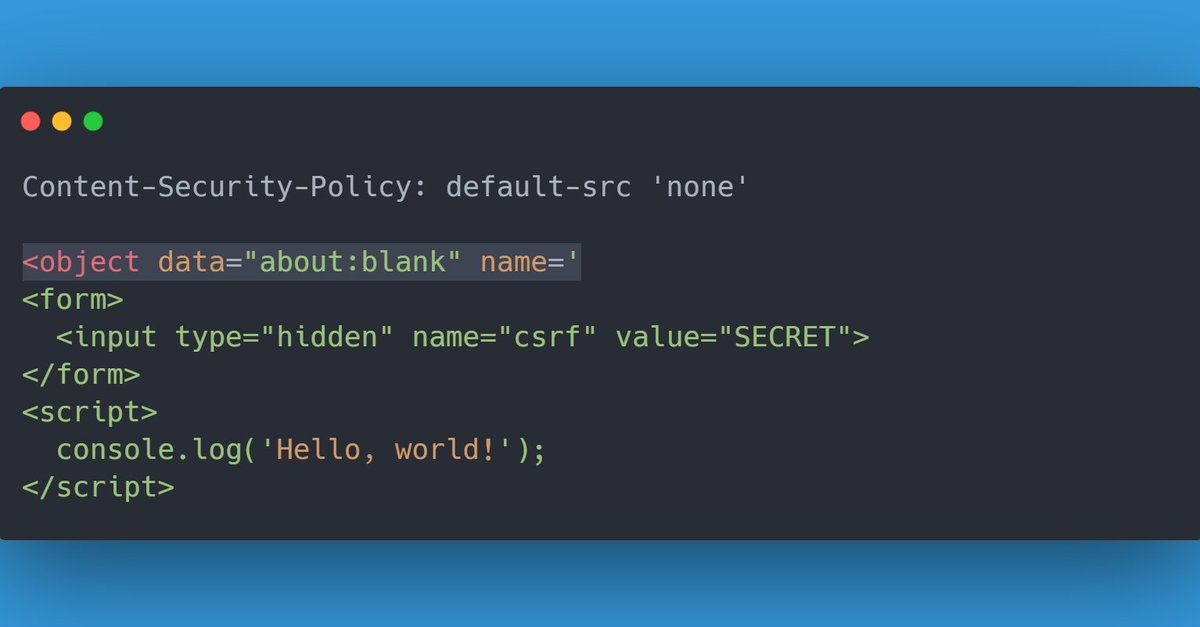
While playing a challenge by Salvatore Abello, I found a pretty interesting way to exploit Dangling Markup with a strict CSP. All you need is an <iframe>, <object> or <embed> set to about:blank, with a dangling name= attribute. This vulnerable page should be iframable.