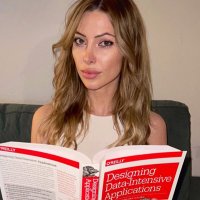
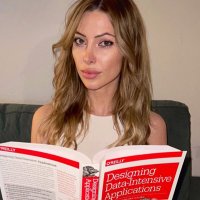
John Connor
@connorsecurity
Cybersecurity from the future
ID: 1212057615259201538
31-12-2019 17:07:16
376 Tweet
427 Followers
1,1K Following
















@connorsecurity
Cybersecurity from the future
ID: 1212057615259201538
31-12-2019 17:07:16
376 Tweet
427 Followers
1,1K Following