bakki
@avx128
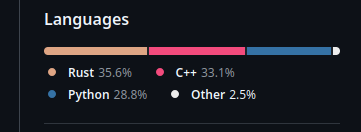
19yo \\\ b2b saas cyberweapon engineer \\\ github.com/xrombar
ID: 1601319091373064192
https://sillywa.re 09-12-2022 20:53:42
639 Tweet
811 Followers
92 Following






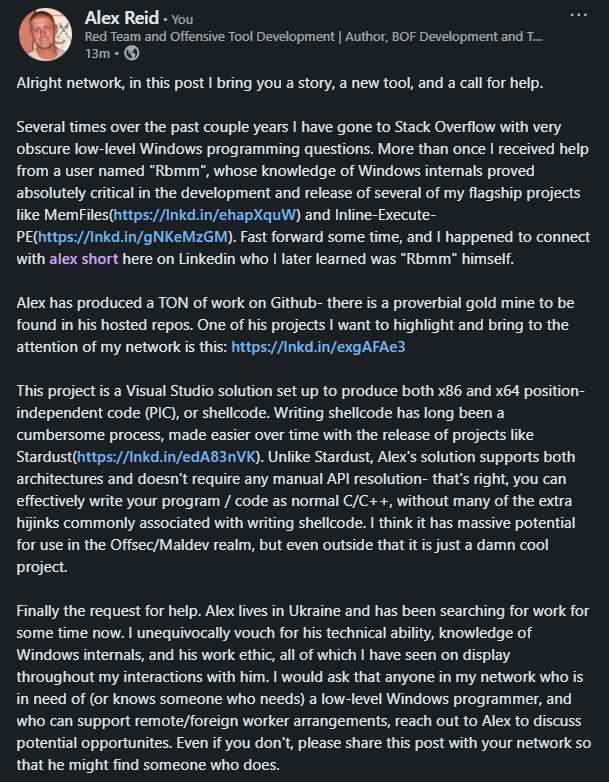
I don't pay for premium, so please read the longform in the picture. TLDR: Cool new VS x86/x64 shellcode template from alex short 🇺🇦 at github.com/rbmm/SC_DEMO, he lives in Ukraine and is looking for remote work, help him make a connection if you can.







With some guidance from DebugPrivilege I've found a way to easily dump clear text implants even while they sleep. Bad day for sleep obfuscation 💤 blog.felixm.pw/rude_awakening…