August
@0xaugust
ID: 1284173122988437504
17-07-2020 17:09:03
17 Tweet
7 Followers
220 Following






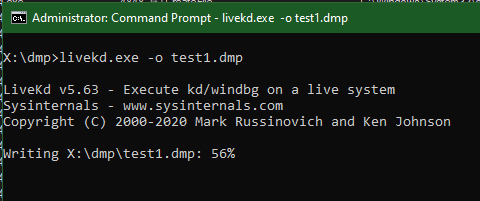
Added a small update to nanodump, you can now create a snapshot of LSASS with PssNtCaptureSnapshot. Thanks to matteo malvica ⭕ for "Evading WinDefender ATP credential-theft: a hit after a hit-and-miss start" github.com/helpsystems/na…

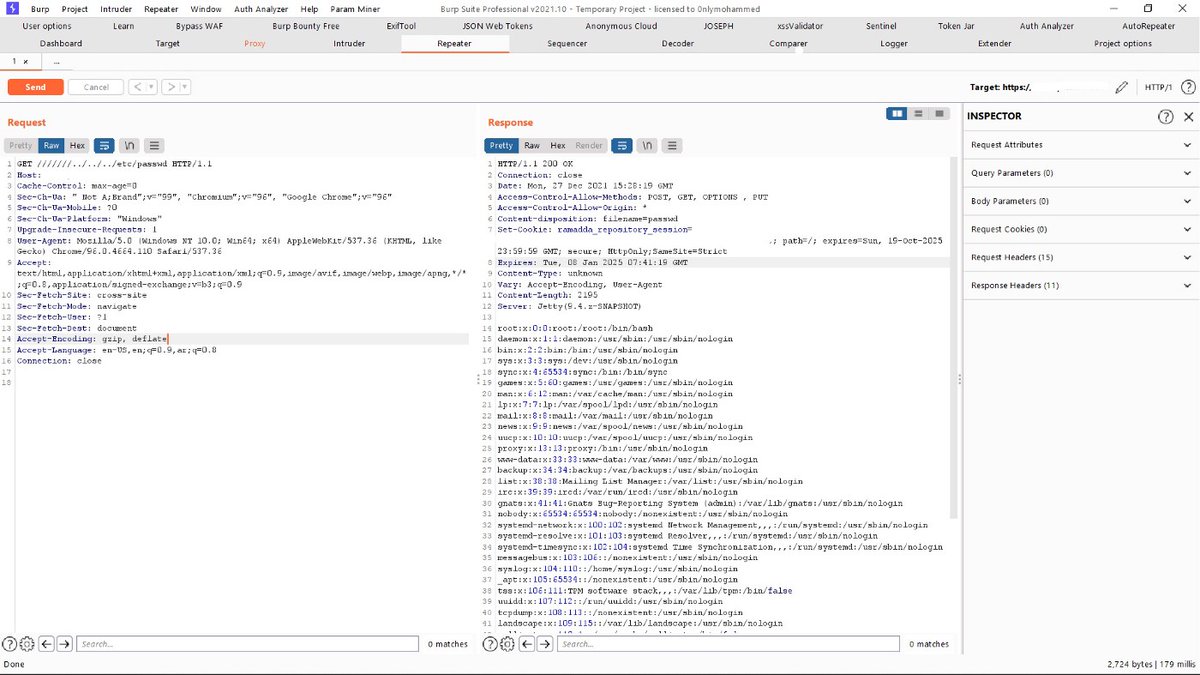
Cas van Cooten LuemmelSec This is a brilliant resource: github.com/commial/experi…


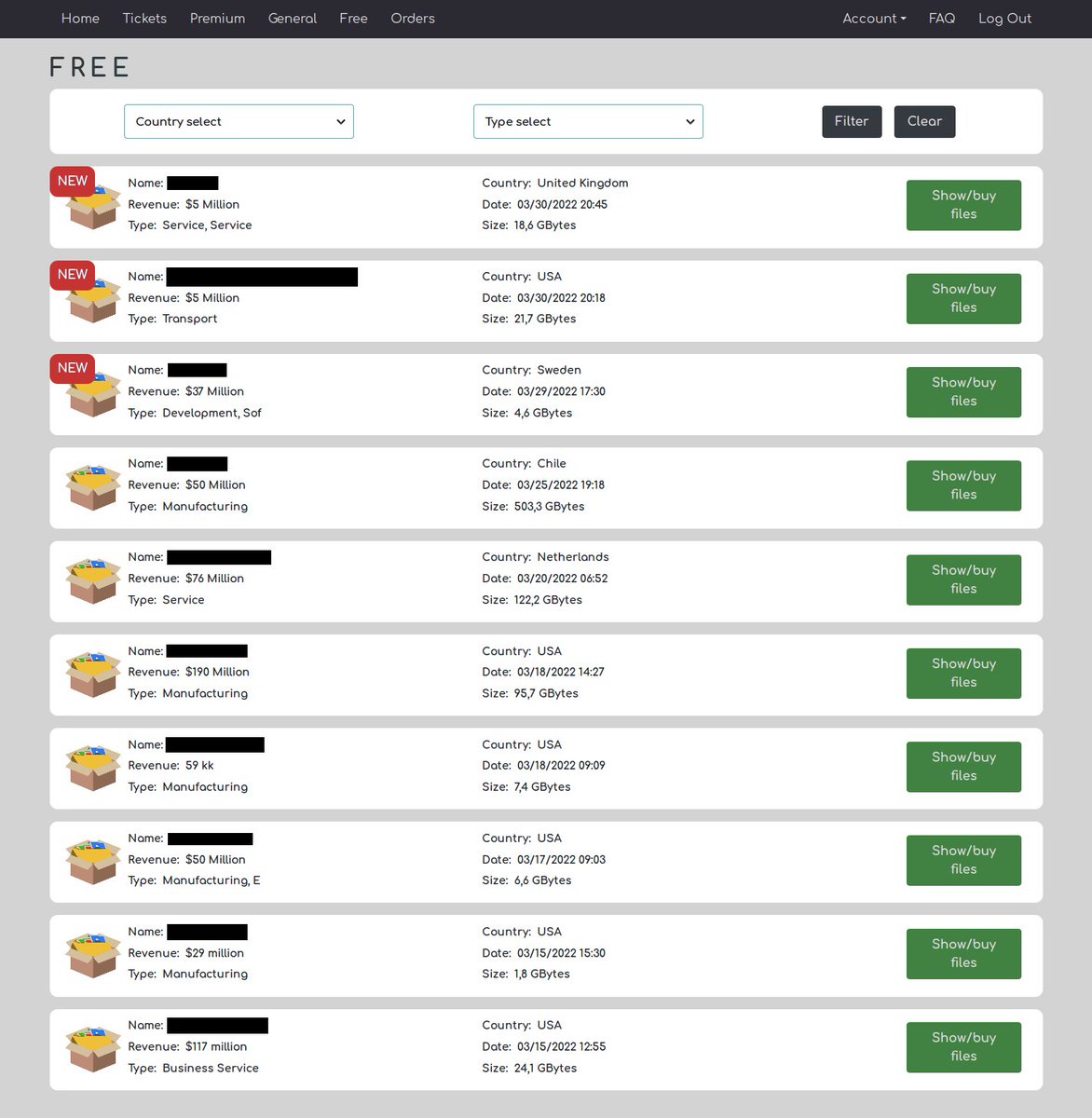
Not really understand this "Industrial Spy" gang. They pwn networks, steals files, then instead of clearly asking a ransom, they leave something more like an ad for their leak/market site? 🤔 Michael Gillespie