J.A.R.V.I.S
@peppermalware
Malware Analyst. Malware Addict.
ID: 948580944323194880
https://www.peppermalware.com 03-01-2018 15:44:55
7,7K Tweet
1,1K Followers
145 Following



The #GPUGate malware, distributed via GitHub and Google Ads, uses GPU encryption. Targets users in Western Europe. #GPUGate Arctic Wolf arcticwolf.com/resources/blog…





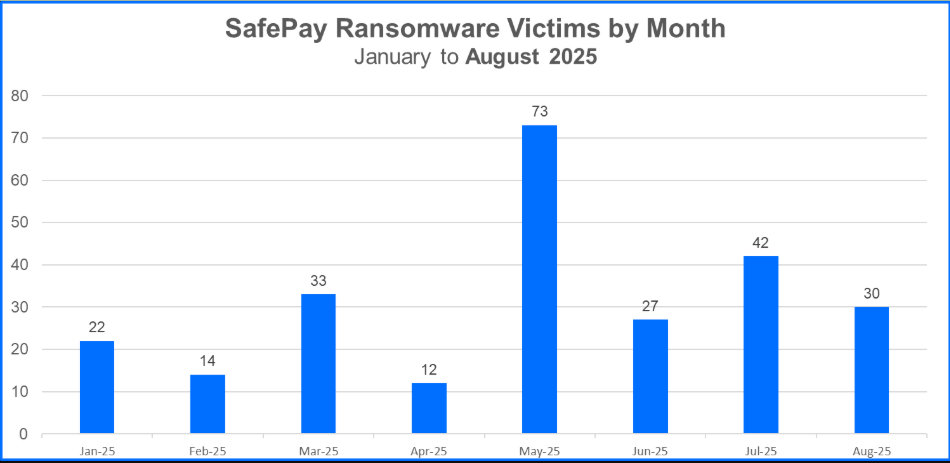
Bitdefender’s Jade Brown profiles SafePay, a non-RaaS ransomware group with hundreds of victims. TTPs include credential compromise, VPN exploitation, IT-staff impersonation, PsExec for lateral movement, and data exfiltration via WinRAR and FileZilla. businessinsights.bitdefender.com/safepay-ransom…










New blog from WKL: WinDbg Time Travel Debugging vs. Intel Processor Trace CPU instruction tracing is insanely powerful for RE + threat hunting but still underused. Alan Sguigna breaks down the tradeoffs, strengths, and when to use each. whiteknightlabs.com/2025/10/14/mic…