TomU | I'm still here... til the end 🕊️🇨🇭
@c_apt_ure
#InfoSec professional, husband & father of two (in random order). #BlueTeam #DFIR #APT #CTI #RedTeaming #BSidesZH (RT/Likes ≠ endorsement) 👀➡️#MalwareChallenge
ID: 205435856
http://c-apt-ure.blogspot.com/ 20-10-2010 21:56:04
15,15K Tweet
8,8K Followers
5,5K Following









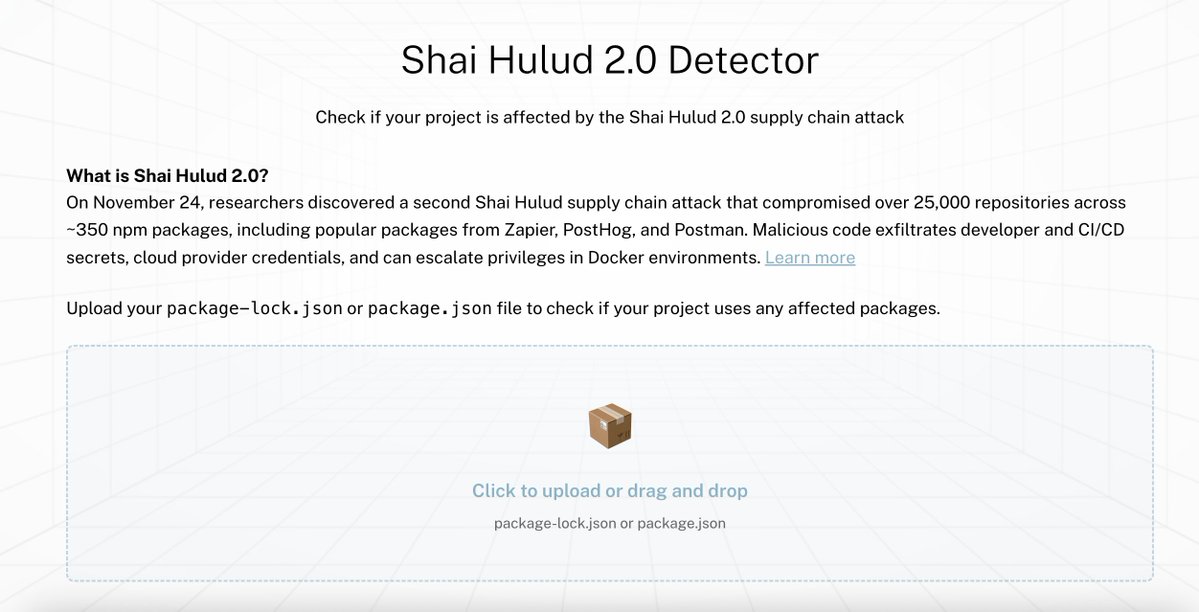
👀Blog with full details & more updates can be found here: reversinglabs.com/blog/another-s… #npm #OSS #SoftwareSupplyChainSecurity #Shaihulud Tomislav Pericin


The SHA1-Hulud npm mess keeps growing, so we added additional detections for it today - new YARA rules by my colleague Marius Benthin in our public signature-base - cover bun_environment.js / setup_bun.js and the malicious preinstall script variants from the Wiz / Aikido




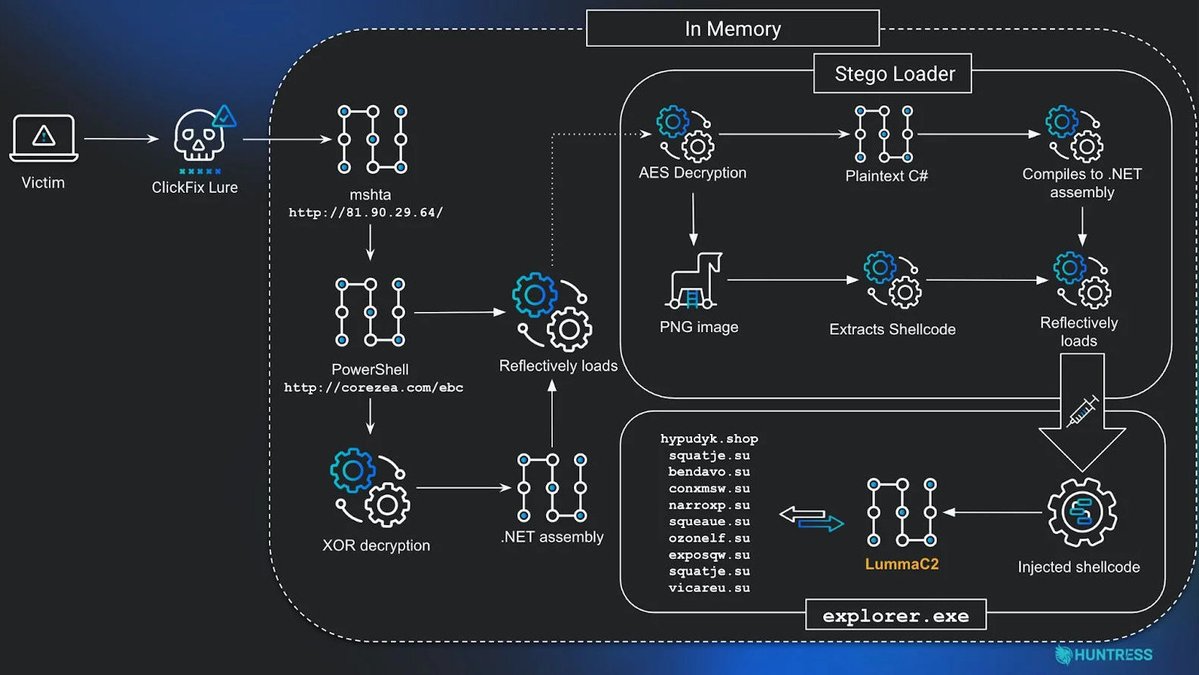
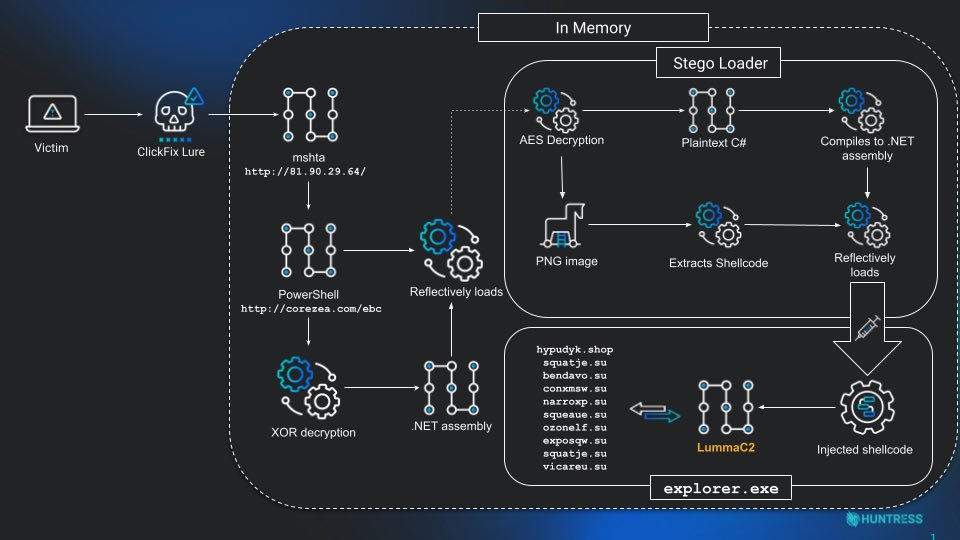
Huntress researchers Anna Pham (RussianPanda 🐼 🇺🇦) & Ben Folland detail a multi-stage malware execution chain, originating from a ClickFix lure, that leads to the delivery of infostealing malware, including LummaC2 & Rhadamanthys. huntress.com/blog/clickfix-…






![Stephan Berger (@malmoeb) on Twitter photo I was reading an older report from CrowdStrike the other day:
"CrowdStrike was able to reconstruct the PowerShell script from the PowerShell Operational event log as the script’s execution was logged automatically due to the use of specific keywords." [1]
Which reminded me of I was reading an older report from CrowdStrike the other day:
"CrowdStrike was able to reconstruct the PowerShell script from the PowerShell Operational event log as the script’s execution was logged automatically due to the use of specific keywords." [1]
Which reminded me of](https://pbs.twimg.com/media/G6l0qe3XwAAywyo.jpg)