Bug Bounty Recon
@bugbountyrecon
ID: 1282584823056470016
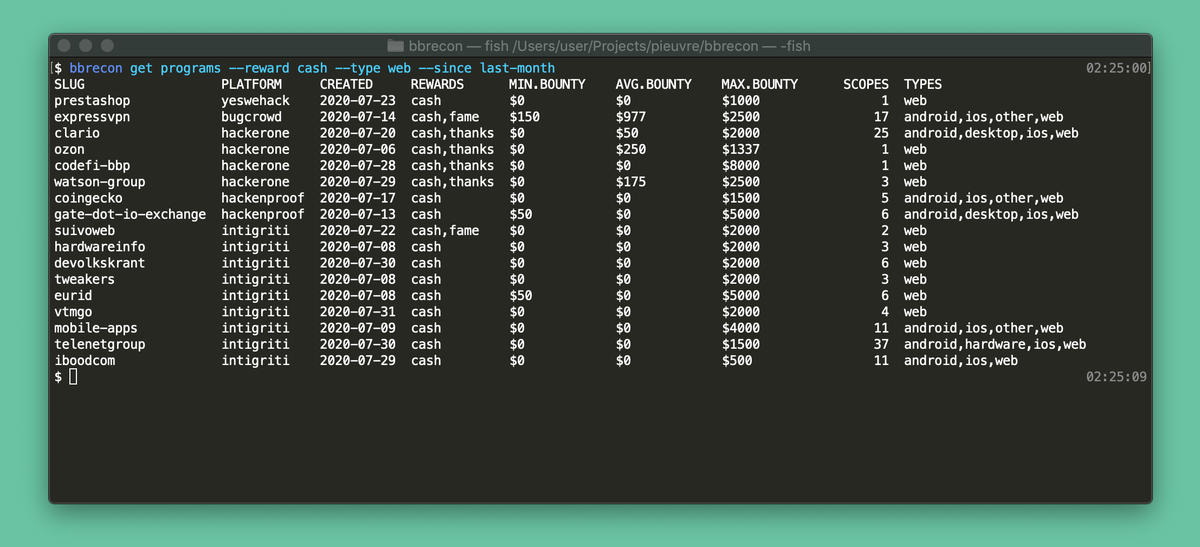
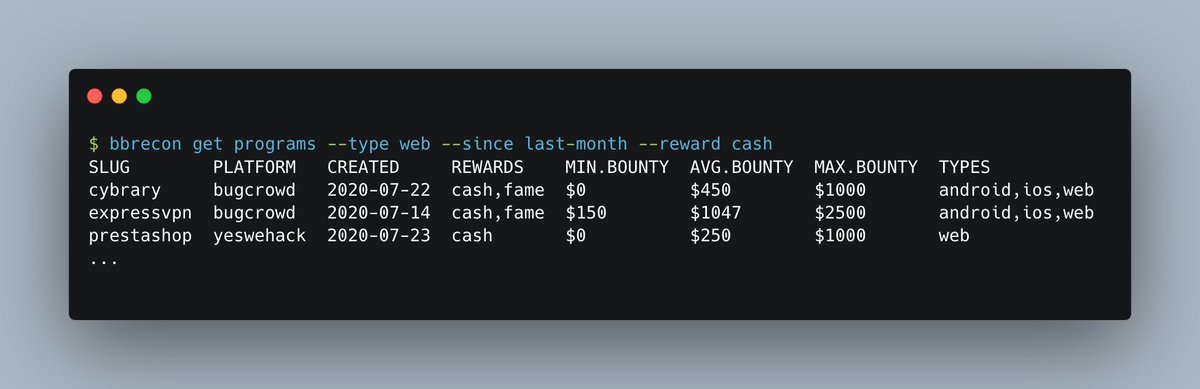
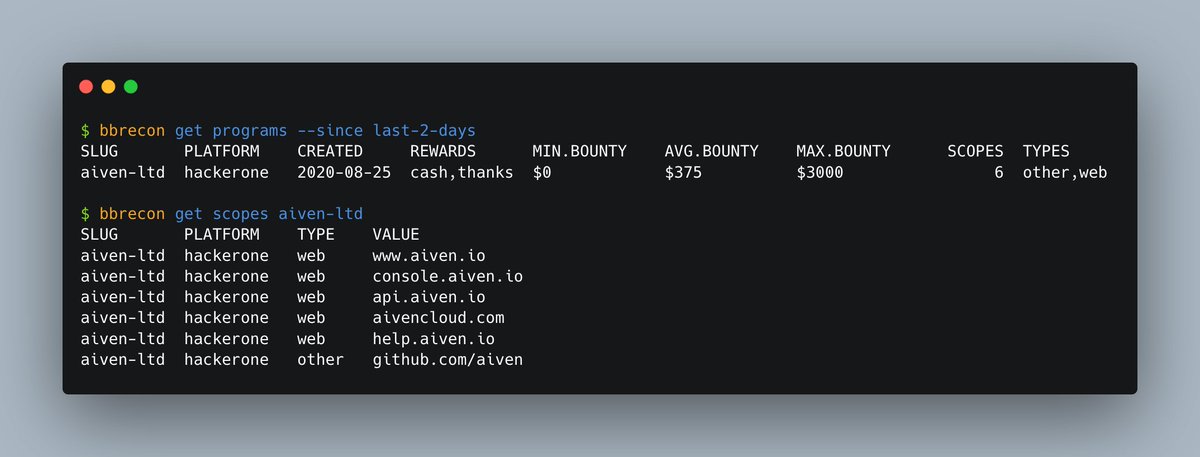
https://github.com/serain/bbrecon 13-07-2020 07:57:29
36 Tweet
1,1K Followers
1,1K Following

Very nice find Chirag Gupta ! Nice approach and straightforward automation. There's bound to be more of these out there folks, go hunt 🙃 #bugbountytips #BugBounty


DEFCON is free this year so definitely take advantage of it, Louis Nyffenegger is doing a workshop on JWT for AppSec Village ! and I can't wait to watch it, especially as JWTs are really common in service-based infrastructure + auth both on my 'to skill up' list

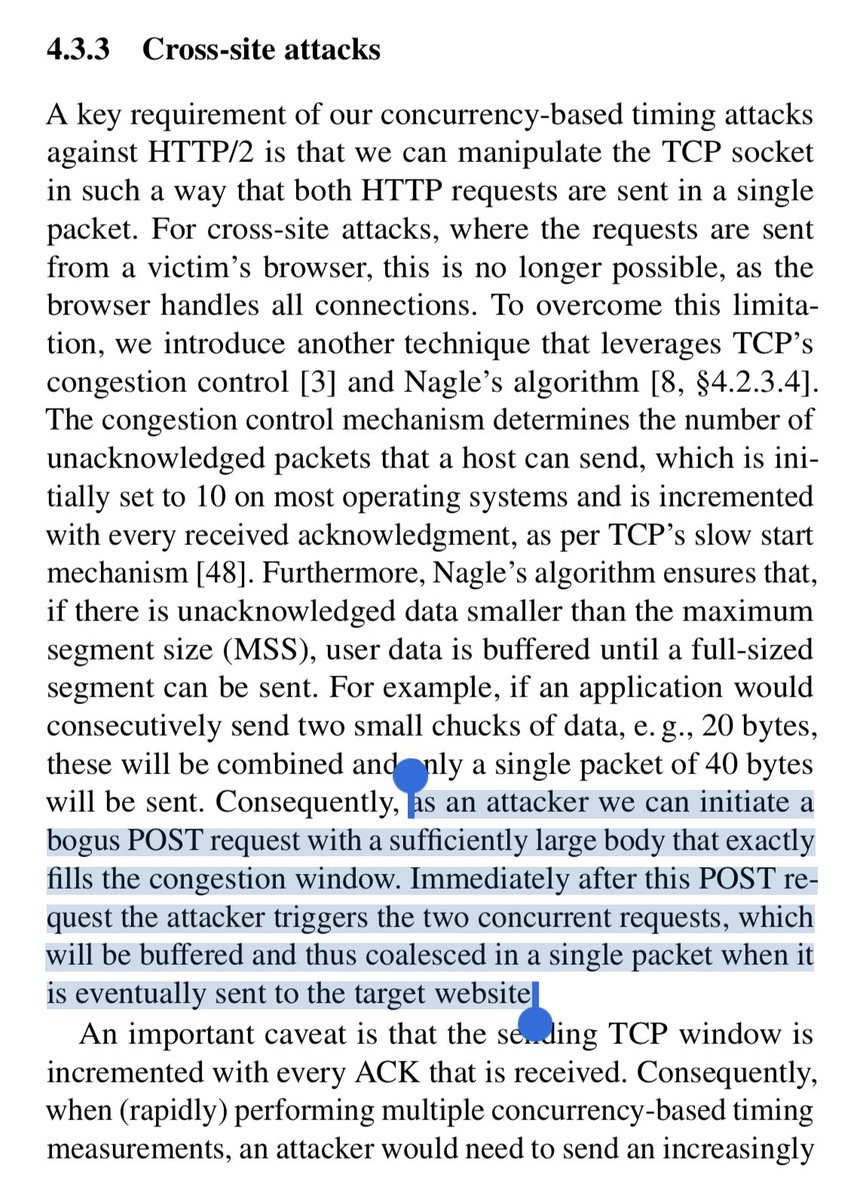
This paper on new timing attack technique based on HTTP2 multiplexing is beautiful! I’ve highlighted the key parts. Look at those request numbers! Now that Burp Suite supporte HTTP2 perhaps we can hope to have a hacker friendly HTTP2 stack available via API to benefitn this

Next week Alvaro Muñoz will present full details about the many RCEs he discovered in CMS platforms such as Atlassian Confluence, Alfresco, Liferay, Crafter CMS, dotCMS, XWiki, and Apache Ofbiz github.co/3hP8Ahp














GitHub Recon - It’s Really Deep: medium.com/@shahjerry33/g… From SSRF to Compromise: Case Study: trustwave.com/en-us/resource… Bug Hunting with Param Miner: Cache poisoning with XSS, a peculiar case: medium.com/bugbountywrite… #PenTest #bugbountytip #OSINT #Hacking #redteam #BugBounty