Aman Sachdev
@admin_login
I make code, I break code, I make code that breaks code and I break code that makes code. #hacker #coder #infosecTrainer #redTeamer
ID: 1083089251997085696
09-01-2019 19:52:55
150 Tweet
295 Followers
324 Following



Thanks Pentester Academy for the nice experience. PS. I wish there was a lab extension option as i wasn't able to try the lab due to covid complications. Had to rush for the exam on the last date without any real practice.



⚠️ In macOS 12 (beta 6), Apple patched an intriguing flaw. Discovered by Gordon Long (Gordon Long), CVE-2021-30853 allowed attackers to bypass: ▫️Gatekeeper ▫️Notarization ▫️File Quarantine Interested in exactly how? Read: "Where's the Interpreter!?" objective-see.com/blog/blog_0x6A…





Thanks THREAT CON for inviting us. We had a wonderful time :) #securityconference #threatcon #nepal #kathmandu #cybersecurity






Just recreated this awesome SpecterOps (Nick Powers, Steven) technique for initial access by #backdooring a random #ClickOnce application with a Cobalt Strike stager. While I became a ClickOnce addict🙃, compiled a short writeup about my journey: an0n-r0.medium.com/backdooring-cl…


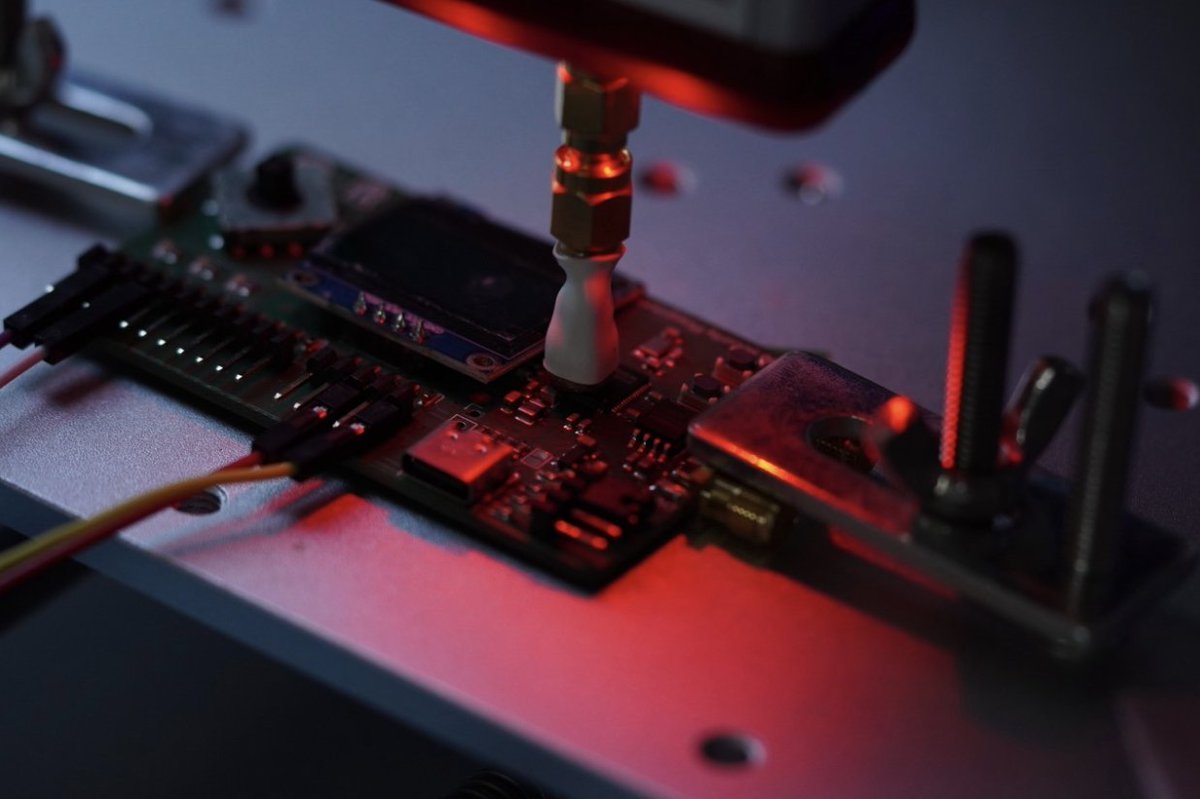
Last year, Raspberry Pi hired us to test the security of the RP2350 - and using electro-magnetic fault-injection we were able to successfully bypass the OTP security measures! This allowed us to read and modify the OTP locks, essentially bypassing the RP2350 secure-boot.