Ankit saini
@d3afh3av3n
Security Engineer @Tekion |Ex-Blinkit |DevSecOps |Python | Automation |Learner
ID: 801770489848872960
24-11-2016 12:52:35
167 Tweet
169 Followers
760 Following



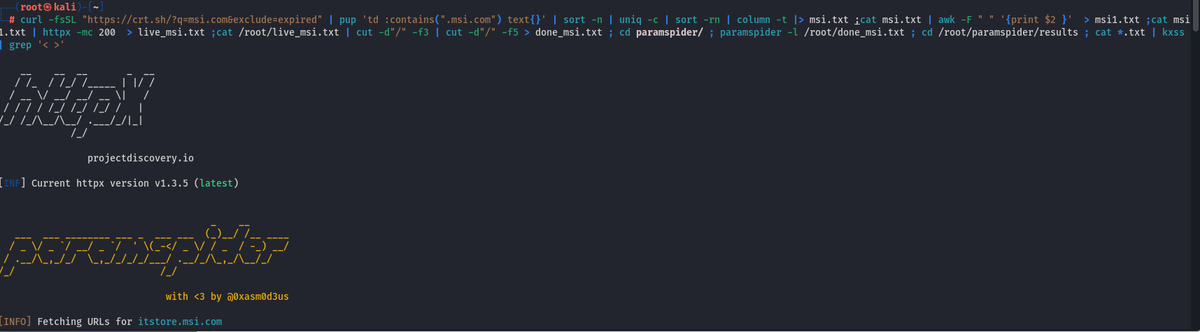
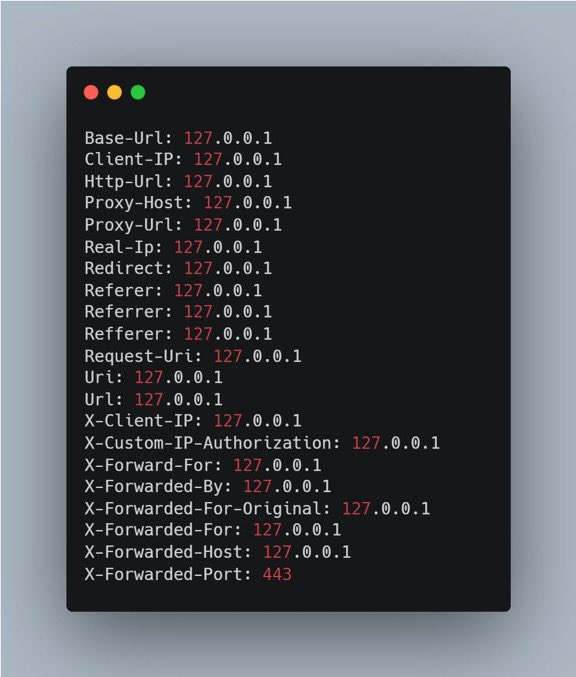
autoSSRF (Automatic SSRF Testing) - Smart fuzzing on relevant SSRF GET parameters and Context-based dynamic payload generation - Repo: github.com/Th0h0/autossrf - Creator: Thomas Houhou - - #CyberSecurity #bugbountytips #infosec #CTF #tools














Hakoriginfinder by Luke Stephens (hakluke) is a simple tool to quickly identify the origin hosts of targets behind firewalls, CDNs, and other types of reverse proxies! 🤠 🔗 github.com/hakluke/hakori…