Dominic Wang
@d0mzw
...
ID: 386133750
06-10-2011 18:32:20
3,3K Tweet
395 Takipçi
476 Takip Edilen



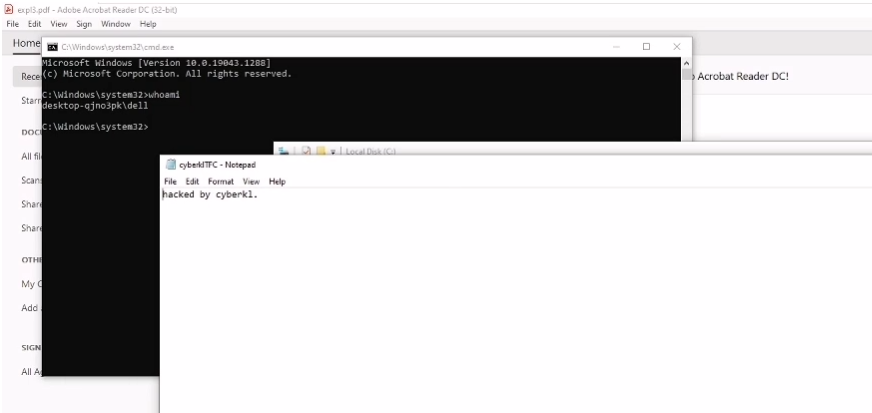
Had fun writing an exploit for CVE-2022-1802 TrendAI Zero Day Initiative github.com/mistymntncop/C…


Speaking of USENIX Association security ‘22, this paper is fascinating…Integration of a similar functionality in IDA/Ghidra/Binja would make much sense, to allow reversers to improve the pseudocode. Decomperson: How Humans Decompile and What We Can Learn From It usenix.org/conference/use…


Part 2 of the blog describing the #Firefox bug used by Manfred Paul at #Pwn2Own Vancouver is live. Hossein Lotfi continues looking at the code execution bug with sandbox escape that won $100K at the event. Read the details (and watch the video demo) at zerodayinitiative.com/blog/2022/8/23…



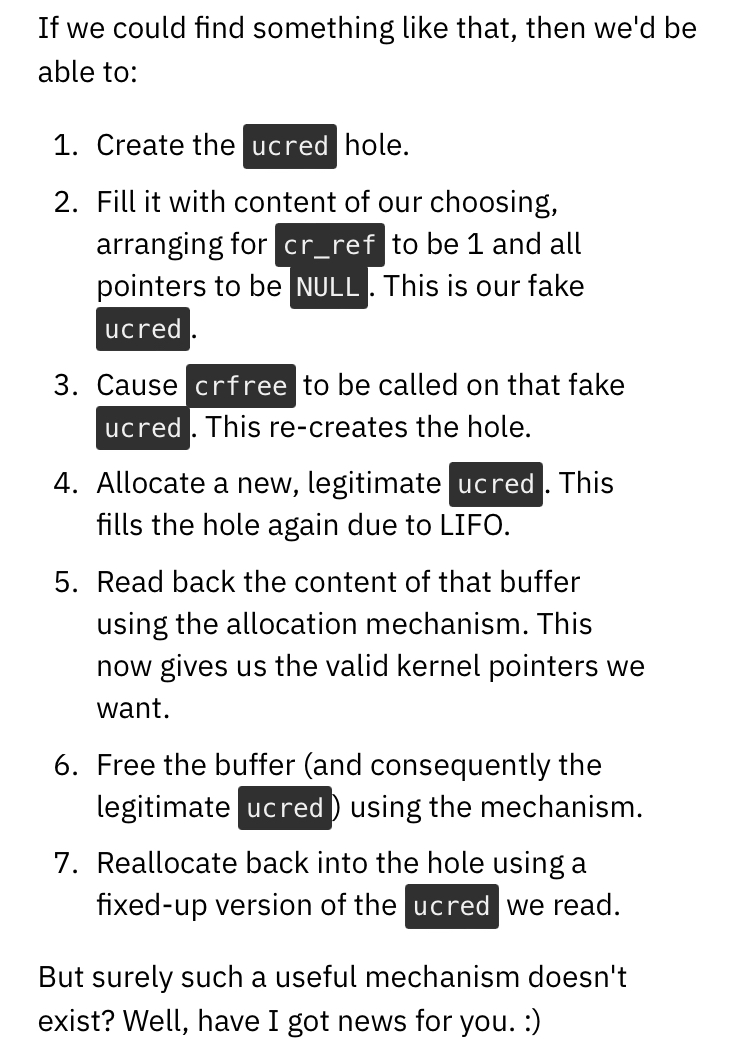
Recently @fidgetingbits presented at HITCON on a 6 year old Linux kernel use-after-free vulnerability (CVE-2022-32250) which we exploited to gain reliable priv esc on Ubuntu 22.04. research.nccgroup.com/wp-content/upl… by @nccgroupinfosec EDG Cedric Halbronn @fidgetingbits Alex Plaskett"






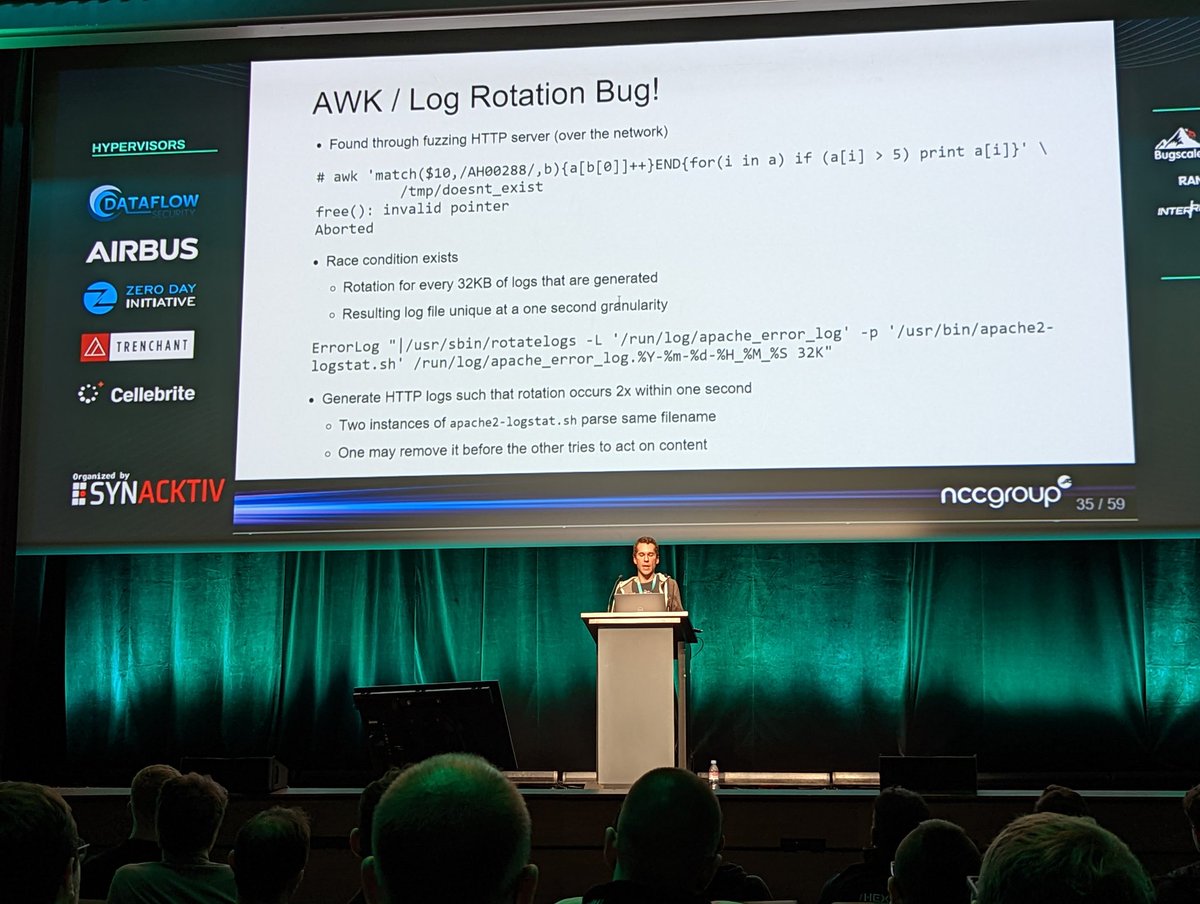
Learn how we discovered 5 distinct vulnerabilities on WatchGuard #Firebox/#XTM firewalls, and obtained a pre-auth Remote Code Execution as root #0day (CVE-2022-31789, CVE-2022-31790). ambionics.io/blog/hacking-w…



The slides for Toner Deaf – Printing your next persistence at Hexacon by Cedric Halbronn and Alex Plaskett demonstrating remote compromise of a Lexmark printer and a persistence backdoor are now available research.nccgroup.com/2022/10/17/ton…

Video now out for our Lexmark printer exploitation and persistence research by Alex Plaskett Cedric Halbronn and fidgeting bits in the talk titled 'Toner Deaf – Printing your next persistence (Hexacon 2022)' research.nccgroup.com/2022/10/17/ton… youtube.com/watch?v=TUHcZp…