Cyber_Ravan
@cyber_ra1
Just An Another Person Who Is Still Trying To Learn.
ID: 908596498748854274
15-09-2017 07:41:01
213 Tweet
1,1K Followers
450 Following

new #eCh0raix #ransomware #linux sample elf: db87238952aced3e20c364956426cd1b script: 9d5c556eaf28973513d40a167273a2d6 (drop from -> 211[.36.1[.152 ) ip: 1[.220.92.198[:8899 7zvu7njrx7q734kvk435ntuf37gfll2pu46fmrfoweczwpk2rhp444yd[.]onion MalwareHunterTeam Fox_threatintel
![Cyber_Ravan (@cyber_ra1) on Twitter photo new #eCh0raix #ransomware #linux sample
elf: db87238952aced3e20c364956426cd1b
script: 9d5c556eaf28973513d40a167273a2d6 (drop from -> 211[.36.1[.152 )
ip: 1[.220.92.198[:8899
7zvu7njrx7q734kvk435ntuf37gfll2pu46fmrfoweczwpk2rhp444yd[.]onion
<a href="/malwrhunterteam/">MalwareHunterTeam</a> <a href="/banthisguy9349/">Fox_threatintel</a> new #eCh0raix #ransomware #linux sample
elf: db87238952aced3e20c364956426cd1b
script: 9d5c556eaf28973513d40a167273a2d6 (drop from -> 211[.36.1[.152 )
ip: 1[.220.92.198[:8899
7zvu7njrx7q734kvk435ntuf37gfll2pu46fmrfoweczwpk2rhp444yd[.]onion
<a href="/malwrhunterteam/">MalwareHunterTeam</a> <a href="/banthisguy9349/">Fox_threatintel</a>](https://pbs.twimg.com/media/GS05IddaYAAqkg3.jpg)

#KematianStealer C2 ip's 95[.]211[.]96[.]106[:]8080 45[.]145[.]41[.]231[:]8080 103[.]190[.]81[.]201[:]8080 64[.]52[.]80[.]191[:]8080 82[.]117[.]255[.]71[:]8080 FOFA query: title="Kematian-Stealer" Fox_threatintel Mikhail Kasimov
![Cyber_Ravan (@cyber_ra1) on Twitter photo #KematianStealer C2 ip's
95[.]211[.]96[.]106[:]8080
45[.]145[.]41[.]231[:]8080
103[.]190[.]81[.]201[:]8080
64[.]52[.]80[.]191[:]8080
82[.]117[.]255[.]71[:]8080
<a href="/fofabot/">FOFA</a> query: title="Kematian-Stealer"
<a href="/banthisguy9349/">Fox_threatintel</a> <a href="/500mk500/">Mikhail Kasimov</a> #KematianStealer C2 ip's
95[.]211[.]96[.]106[:]8080
45[.]145[.]41[.]231[:]8080
103[.]190[.]81[.]201[:]8080
64[.]52[.]80[.]191[:]8080
82[.]117[.]255[.]71[:]8080
<a href="/fofabot/">FOFA</a> query: title="Kematian-Stealer"
<a href="/banthisguy9349/">Fox_threatintel</a> <a href="/500mk500/">Mikhail Kasimov</a>](https://pbs.twimg.com/media/GTO13N2aQAAWRKU.jpg)

Intresing observation with the help of just single string i am able to collect 300+ sample of #lummac and #Stealc #Stealer String: "C:\Windowsterminatedowner" IOC's: pastebin.com/raw/QMbiTacZ RussianPanda 🐼 🇺🇦 MalwareHunterTeam James


Last Monday I woke up and notice that my GitHub account is been suspended! I don't know the reason why they did this, i tried to recover but no reply from github 😕 My git was having awesome project now i lots all of them Fox_threatintel MalwareHunterTeam RussianPanda 🐼 🇺🇦

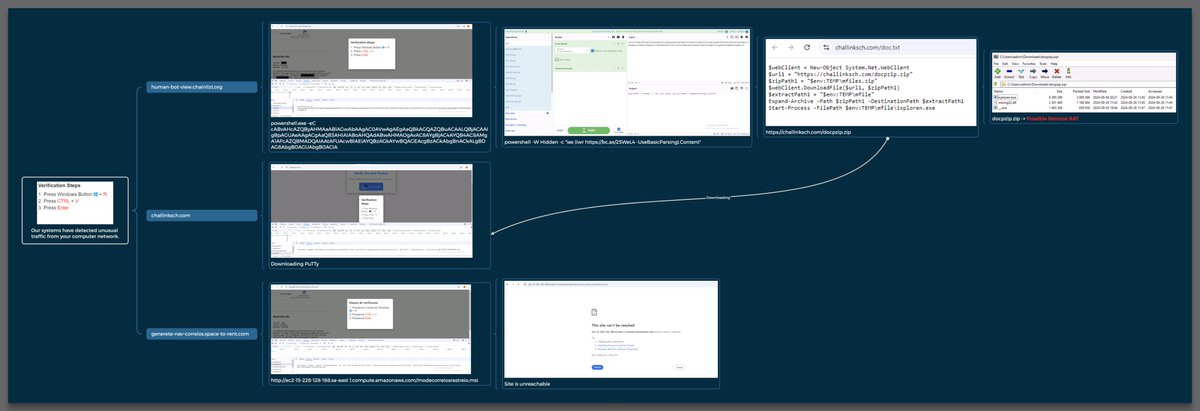
Malicous websit ask you to do following steps whic #downloads the #Remcos 1. Press Windows Button "🪟" + R 2. Press CTRL + V 3. Press Enter ioc: paste4btc.com/pjRexqBr FOFA query :title=="Custom reCAPTCHA Checkbox" RussianPanda 🐼 🇺🇦 Fox_threatintel MalwareHunterTeam




Discovered 2.5K+ #telegram based #phishing and #CryptoScam IOC's IOC: hastebin.com/share/qevudumu… Fox_threatintel RussianPanda 🐼 🇺🇦 Mikhail Kasimov MalwareHunterTeam


Folks, I discovered a surprising thing today: We can search the comments on #VirusTotal without logging in. Is this a new feature from VirusTotal 🤔🤔 MalwareHunterTeam James Florian Roth ⚡️ Fox_threatintel RussianPanda 🐼 🇺🇦 vx-underground



The metioned #Remcos in this artical been loaded by #KLoader #Malware, Additionally, you may see that the threat actor used and shared the same #C2 ( mytaxclientcopy[.]com ) mentioned in this blog in the sample video. Fox_threatintel RussianPanda 🐼 🇺🇦 MalwareHunterTeam 0x6rss


![Cyber_Ravan (@cyber_ra1) on Twitter photo 7777 #botnet is back and here how you can hunt
<a href="/censysio/">Censys</a> search query:
1] - services.banner_hex="786c6f67696e3a"
2] - services.software.vendor="7777 Botnet"
7777 Botner C2: pastebin.com/AQDTDEvg 7777 #botnet is back and here how you can hunt
<a href="/censysio/">Censys</a> search query:
1] - services.banner_hex="786c6f67696e3a"
2] - services.software.vendor="7777 Botnet"
7777 Botner C2: pastebin.com/AQDTDEvg](https://pbs.twimg.com/media/Gdx6oNubsAAJAyW.jpg)