Marc
@cti_marc
ID: 1186542753699766273
http://blog.sekoia.io 22-10-2019 07:20:30
216 Tweet
466 Takipçi
258 Takip Edilen





Awesome report from The DFIR Report! C2 for #CobaltStrike and #Metasploit were in Sekoia.io CTI feed since October 2022! To learn more about our #C2Trackers capabilities: blog.sekoia.io/command-contro… Shoutout to C2IntelFeedsBot for reporting CobaltStrike C2 first in open-source










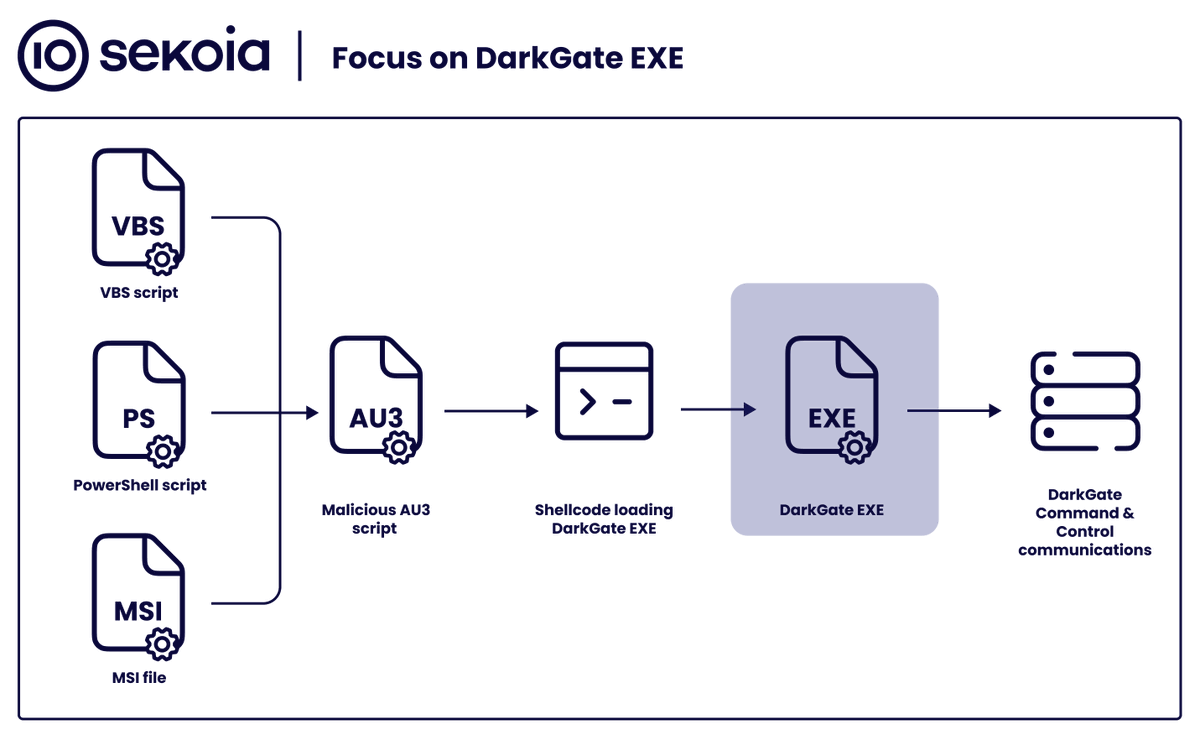
🚨 Sekoia TDR uncovered key insights into the infrastructure behind #Emmenthal Loader distribution using #WebDAV as a service! Thanks to CERT Orange Cyberdefense & Mandiant (part of Google Cloud) for their research, which helped shed light on this! 🙏 Read the full report here: blog.sekoia.io/webdav-as-a-se…





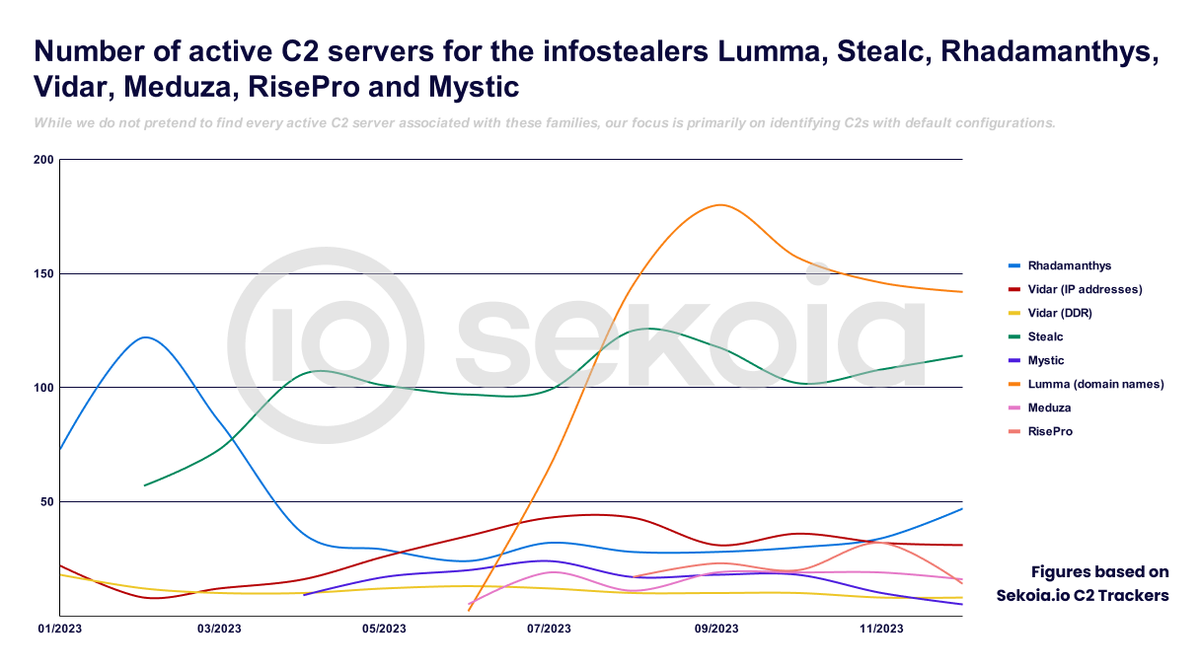
![crep1x (@crep1x) on Twitter photo The indicator of compromise mentioned in the Google TAG report that corresponds to a C2 server of #Rhadamanthys is 104.156.149[.]126, active at least from January 16, 2023 to end of March according to our <a href="/sekoia_io/">Sekoia.io</a> C2 trackers.
It was also publicly shared by <a href="/0xrb/">R.</a> on ThreatFox! The indicator of compromise mentioned in the Google TAG report that corresponds to a C2 server of #Rhadamanthys is 104.156.149[.]126, active at least from January 16, 2023 to end of March according to our <a href="/sekoia_io/">Sekoia.io</a> C2 trackers.
It was also publicly shared by <a href="/0xrb/">R.</a> on ThreatFox!](https://pbs.twimg.com/media/FuKpAl2WAAIjUB7.jpg)