Cloud Deb
@cloudsarefunny
Just another cloud wrangler at some tech company
ID: 919273972352421888
14-10-2017 18:49:29
188 Tweet
35 Followers
19 Following
















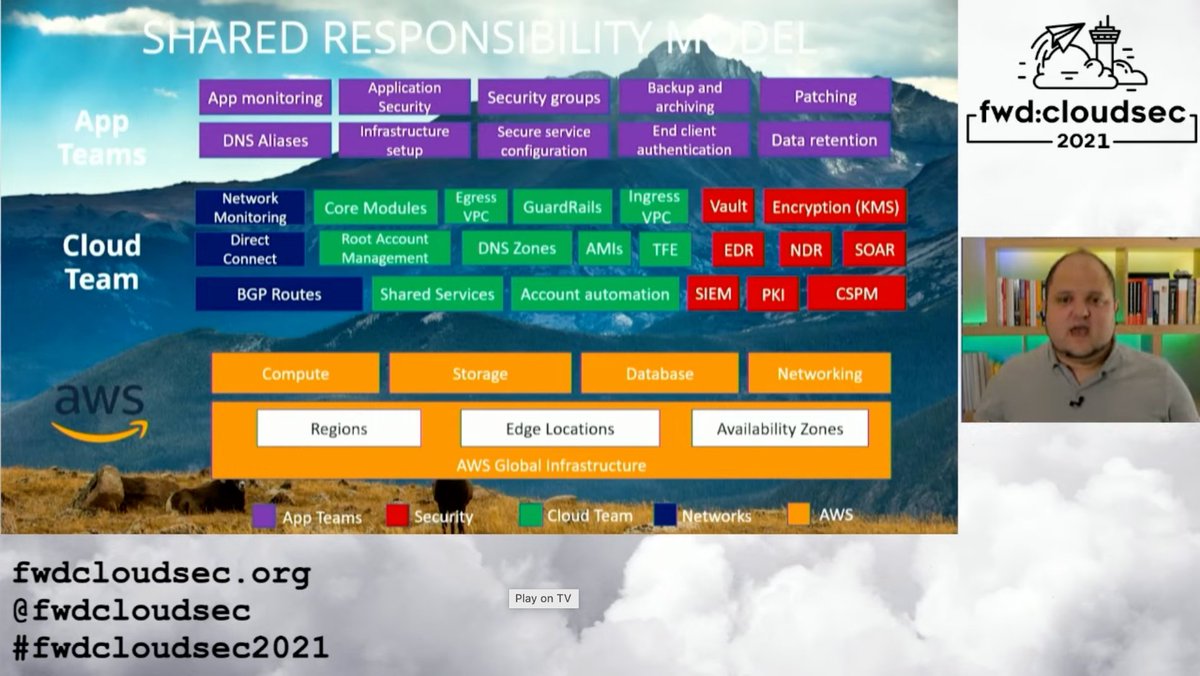
Just watched Jared Naude's talk at fwd:cloudsec . Glad to see he's had some success expanding the shared responsibility model to separate app and infrastructure/platform teams in his work. May be the inspiration I need to help drive this ahead at my company.