
Michael Cherny
@chernymi
Programmer, Security Researcher, Architect, Tech enthusiast, now Chief Architect @aquasecteam
ID: 576221049
10-05-2012 11:03:16
185 Tweet
325 Followers
205 Following





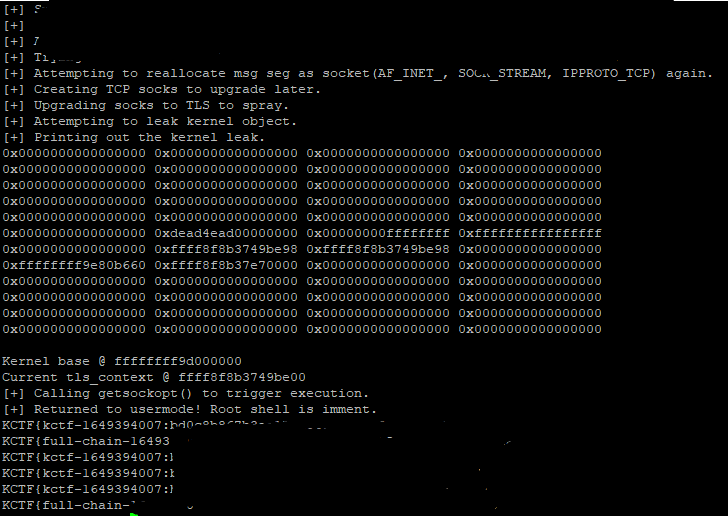
Well that was a very difficult but fun exploit to write. We've reported to Linux and will do a write-up soon (David Bouman and myself). Details redacted since it's not patched yet.






Diamond #kerberos attack now part of #Rubeus. Original research by Tal Be'ery & Michael Cherny



My awesome colleague Nick Frichette has found a cross-tenant vulnerability in AWS AppSync, allowing an attacker to access data in victim's accounts. Write-up: securitylabs.datadoghq.com/articles/appsy… AWS security bulletin: aws.amazon.com/security/secur…




Truly impressive and inspiring presentation it was. Kudos Benny Zeltser and Jonathan Lusky

Very interesting talk. Thank you Hyrum Anderson .




