CertifyCyber
@certifycyber1
Posts about cyber security, digital forensics, phishing, malware, password management, and technology topics.
#cybersecurity #phishing #malware #dfir
ID: 1566435783606616064
04-09-2022 14:39:59
66 Tweet
135 Followers
583 Following














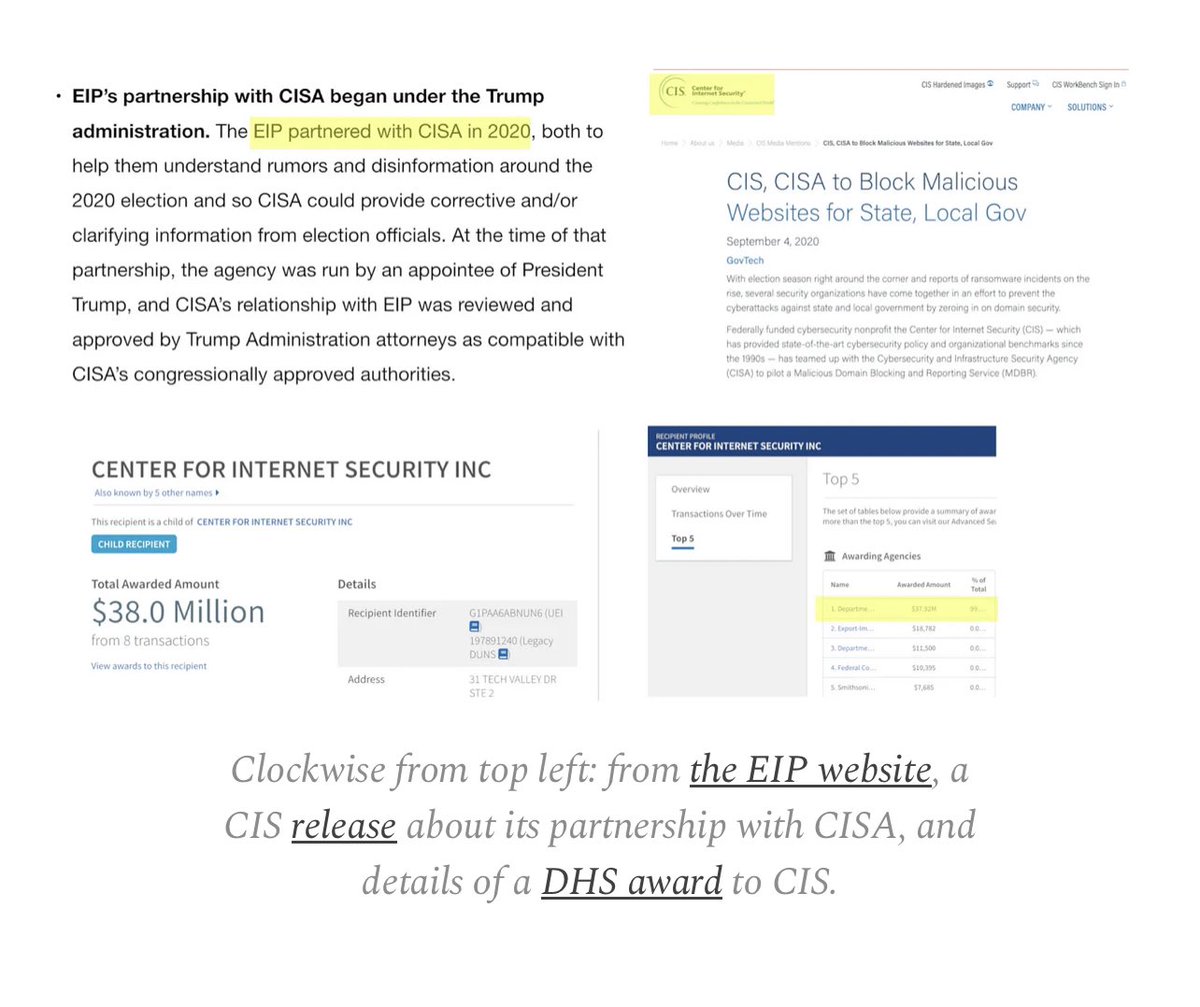
Dear Mehdi Hasan: here’s the EIP website saying it partnered with CISA, the CIS site saying the same thing, and the award showing CIS is a DHS contractor. You’re wrong on this and you convinced a politician to threaten me with jail as a result. This has gone too far.