cd80
@cd8020
ID: 1236931622743584769
09-03-2020 08:27:43
163 Tweet
173 Takipçi
375 Takip Edilen

Reading papers is no doubt the best way to stay up to date in things like machine learning that are always evolving. I came across this repo that contains annotated papers. Very easy to read and understand. github.com/AakashKumarNai… Awesome work Aakash Kumar Nain 👏



The Sensory Neuron as a Transformer: Permutation-Invariant Neural Networks for Reinforcement Learning We explore RL agents that still work even when their observations get shuffled around a lot! A fun paper w/ Yujin Tang web attentionneuron.github.io pdf arxiv.org/abs/2109.02869




#reversefuzzing did you see this concept somewhere else? h0mbre dmnk.bsky.social Brandon Falk is-eqv.bsky.social github.com/dapphub/dappto…










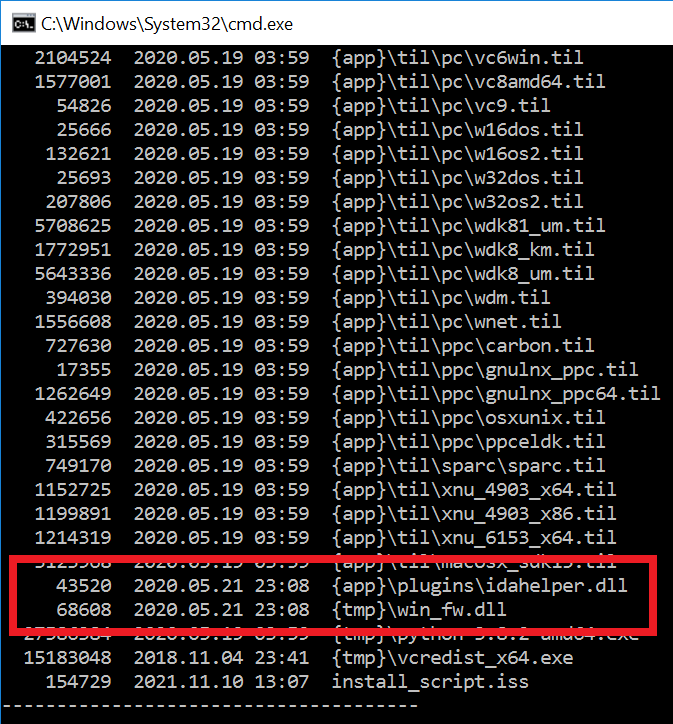
#ESETresearch discovered a trojanized IDA Pro installer, distributed by the #Lazarus APT group. Attackers bundled the original IDA Pro 7.5 software developed by Hex-Rays SA with two malicious components. Anton Cherepanov 1/5