Sandipan Roy
@bytehackr
Senior Product Security Engineer @RedHat | SDE @Fedora | #PSIRT #RHEL | Ex @parrotsec
ID: 978668951822635009
https://linktr.ee/bytehackr 27-03-2018 16:23:55
417 Tweet
204 Followers
1,1K Following




.Michael Ferris is making bold statements 💪 See why the largest orgs in almost every sector depend on Red Hat Enterprise #Linux: red.ht/4ha2Caf.












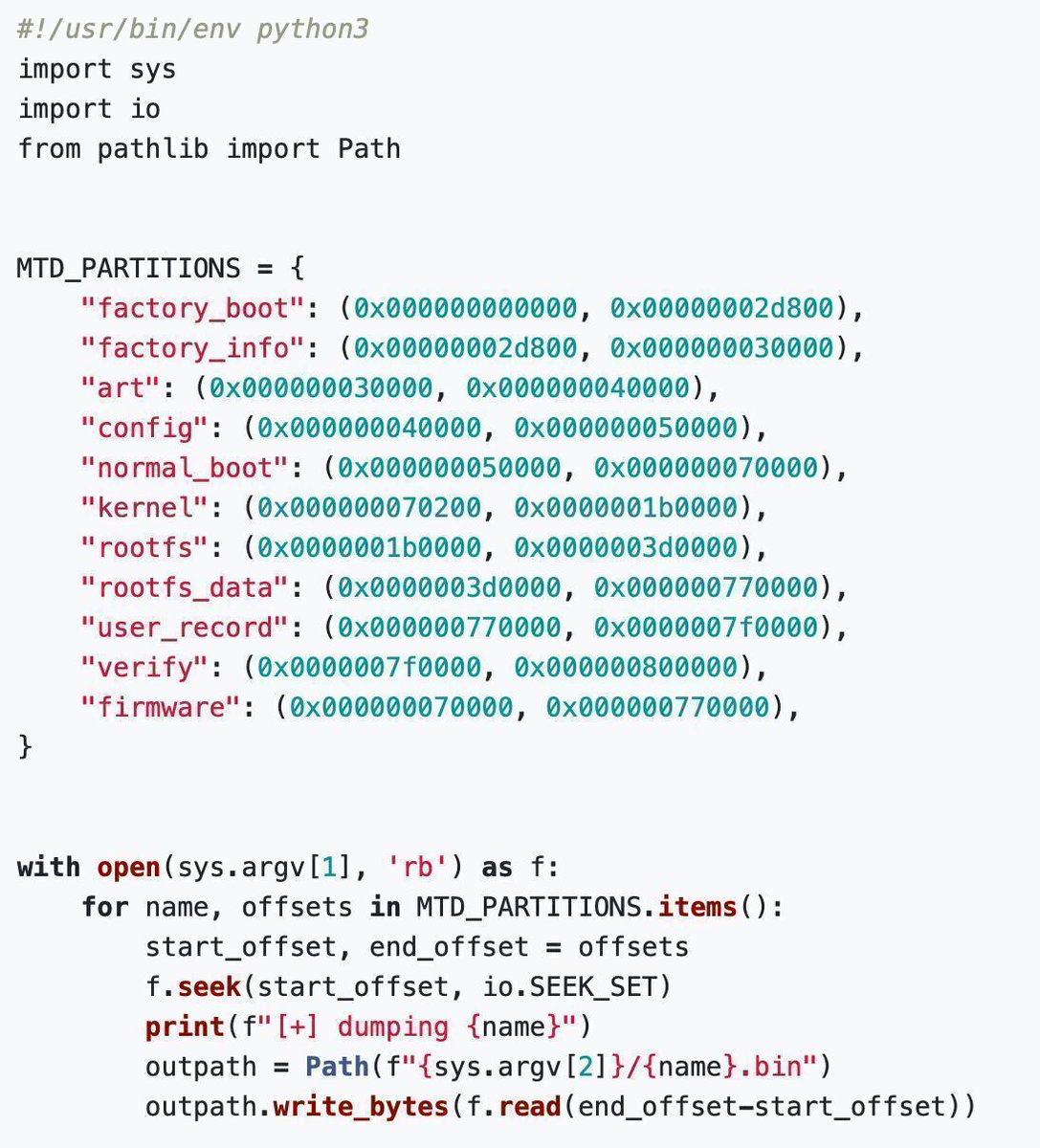
Reverse engineer and get full root access on the TP-Link Tapo C200 (2025) quentinkaiser.be/security/2025/… Research by Quentin Kaiser #infosec