𝕚𝕟𝕕𝕚𝕧𝕚𝕕𝕦𝕒𝕝 𝕓
@bumbl3r
i name pot strains and hack shit
ID: 1277034460232507392
28-06-2020 00:23:19
4,4K Tweet
794 Followers
320 Following


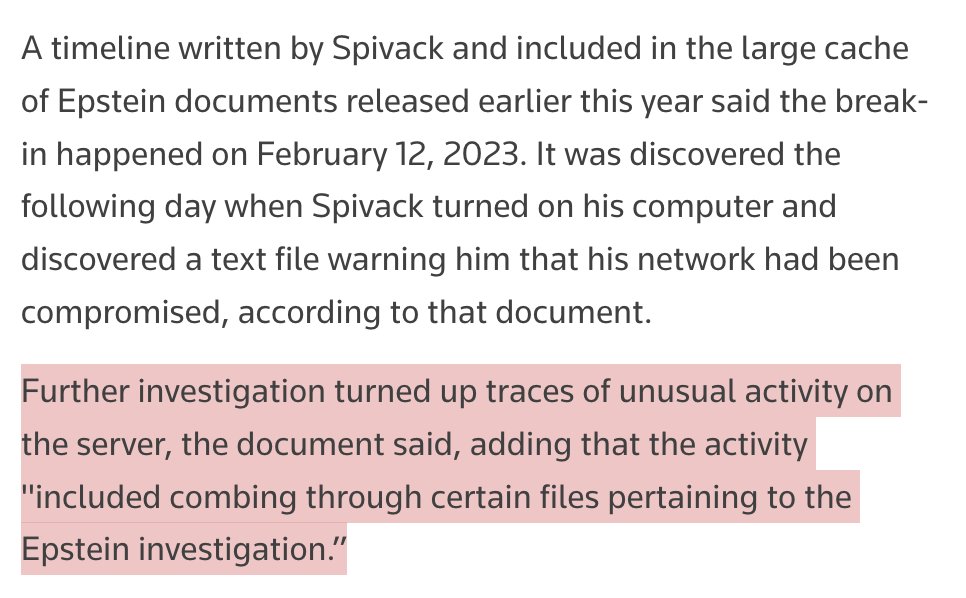
IcedID malware developer faked his own death to avoid being arrested Ukrainian police officers were bribed to fake his death certificate. He was arrested in December A 2nd IcedID malware developer has also been arrested in Ukraine c/o Catalin Cimpanu na01.safelinks.protection.outlook.com/?url=https%3A%…


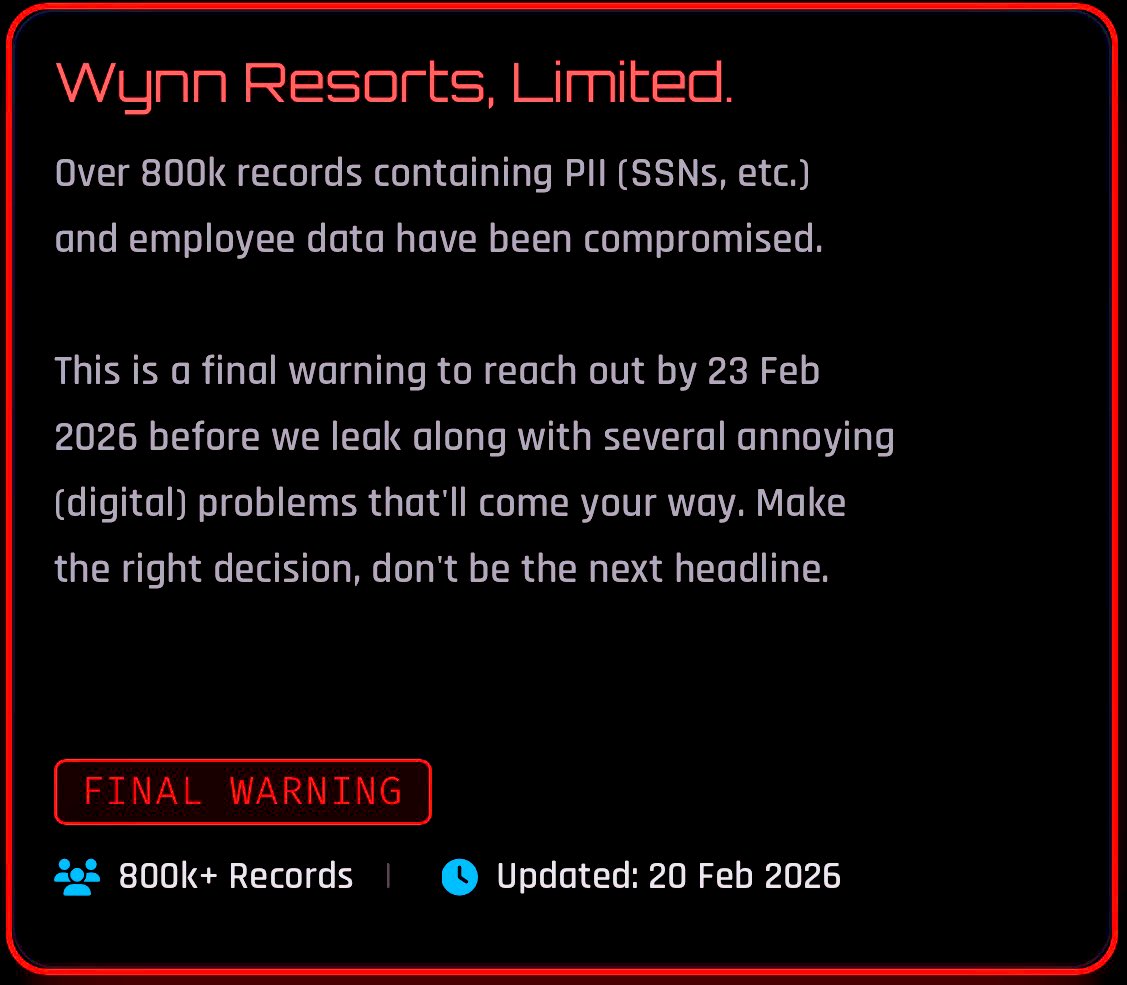
True IP, fresh build. #shinyhunters IP LEAK 91.202.4[.]68 38.69.12[.]23 toolatedhs5dtr2pv6h5kdraneak5gs3sxrecqhoufc5e45edior7mqd[.]onion shinypogk4jjniry5qi7247tznop6mxdrdte2k6pdu5cyo43vdzmrwid[.]onion Dominic Alvieri Dark Web Informer
![t43cr0wl3r (@t43cr0wl3r) on Twitter photo True IP, fresh build.
#shinyhunters IP LEAK
91.202.4[.]68
38.69.12[.]23
toolatedhs5dtr2pv6h5kdraneak5gs3sxrecqhoufc5e45edior7mqd[.]onion
shinypogk4jjniry5qi7247tznop6mxdrdte2k6pdu5cyo43vdzmrwid[.]onion
<a href="/AlvieriD/">Dominic Alvieri</a> <a href="/DarkWebInformer/">Dark Web Informer</a> True IP, fresh build.
#shinyhunters IP LEAK
91.202.4[.]68
38.69.12[.]23
toolatedhs5dtr2pv6h5kdraneak5gs3sxrecqhoufc5e45edior7mqd[.]onion
shinypogk4jjniry5qi7247tznop6mxdrdte2k6pdu5cyo43vdzmrwid[.]onion
<a href="/AlvieriD/">Dominic Alvieri</a> <a href="/DarkWebInformer/">Dark Web Informer</a>](https://pbs.twimg.com/media/HBFY4uHW4AAKcsZ.jpg)


Police arrests 651 suspects in African cybercrime crackdown - Sergiu Gatlan bleepingcomputer.com/news/security/… bleepingcomputer.com/news/security/…
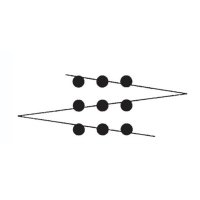

Breaking Las Vegas Wynn Resorts has allegedly been breached by ShinyHunters Over 800K records of personally identifiable information has allegedly been compromised Wynn Las Vegas


PayPal discloses data breach that exposed user info for 6 months - Sergiu Gatlan bleepingcomputer.com/news/security/… bleepingcomputer.com/news/security/…









![Dark Web Informer - Cyber Threat Intelligence (@darkwebinformer) on Twitter photo ‼️ New BreachForums .BF clearnet domain:
breachforums[.]as
Looks like they may have lost .bf again 🤷♀️ ‼️ New BreachForums .BF clearnet domain:
breachforums[.]as
Looks like they may have lost .bf again 🤷♀️](https://pbs.twimg.com/media/HBFI9cuXEAAPL71.jpg)
![𝕚𝕟𝕕𝕚𝕧𝕚𝕕𝕦𝕒𝕝 𝕓 (@bumbl3r) on Twitter photo LockBit still on vacation breaching spas
1 in Mauritius - gangster /sands[.]mu
1 in the Turks and Caicos LockBit still on vacation breaching spas
1 in Mauritius - gangster /sands[.]mu
1 in the Turks and Caicos](https://pbs.twimg.com/media/HBHICDiXwAA0ZdS.jpg)