Bruno
@brunopujos
CEO & Founder @Reverse_Tactics | Tweets are from my employer.
ID: 1227548154
https://www.reversetactics.com/ 28-02-2013 13:33:06
185 Tweet
626 Takipçi
358 Takip Edilen





We closed the 15th edition of #Pwn2Own by demonstrating a LPE vulnerability in the Windows kernel! The vulnerability existed for almost 10 years! Thank you TrendAI Zero Day Initiative for an amazing contest and stay tuned for technical details once Microsoft has patched! #P2O15

Après 3 ans de pause, BeeRumP 2022 aura lieu le 16 septembre dans les locaux du @GroupeESIEA à Ivry ! Vous pouvez d'ores et déjà envoyer vos soumissions de rump à [email protected] (le meilleur moyen d'avoir une place 😁) !




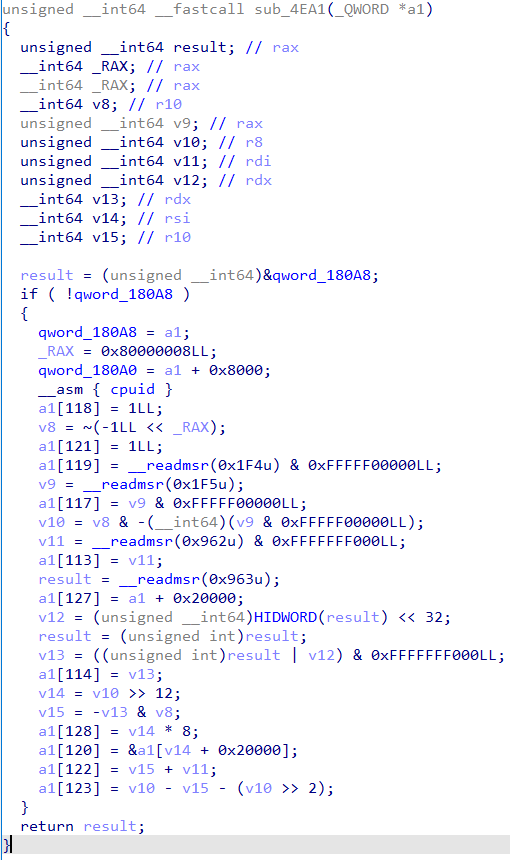
The LPE vulnerability in the windows kernel we reported during #Pwn2Own 2022 in May has been patched by Microsoft on August 9: CVE-2022-34699. Leave us some time to reverse the patch and we are going to publish the technical details for the vulnerability! zerodayinitiative.com/advisories/ZDI…

So an AMD engineer and 2 Google engineers walk into a bar... and write an article about how "Hello World" in #Python works. The article turns out to be 26 pages. From Python, through C, WinAPI/Kernel, font rendering, to GPU. Enjoy! gynvael.coldwind.pl/?lang=en&id=754 asawicki.info/news_1762_hell…









Slides and video of our talk at offensivecon are already online ! Thanks to Binary Gecko for the amazing event reversetactics.com/publications/2…