bitcoinblinker
@bitcoinblinker
twitch.tv/bitcoinblinker #bitcoin #cybersecurity
ID: 1576309566337417217
01-10-2022 20:34:52
256 Tweet
25 Followers
101 Following




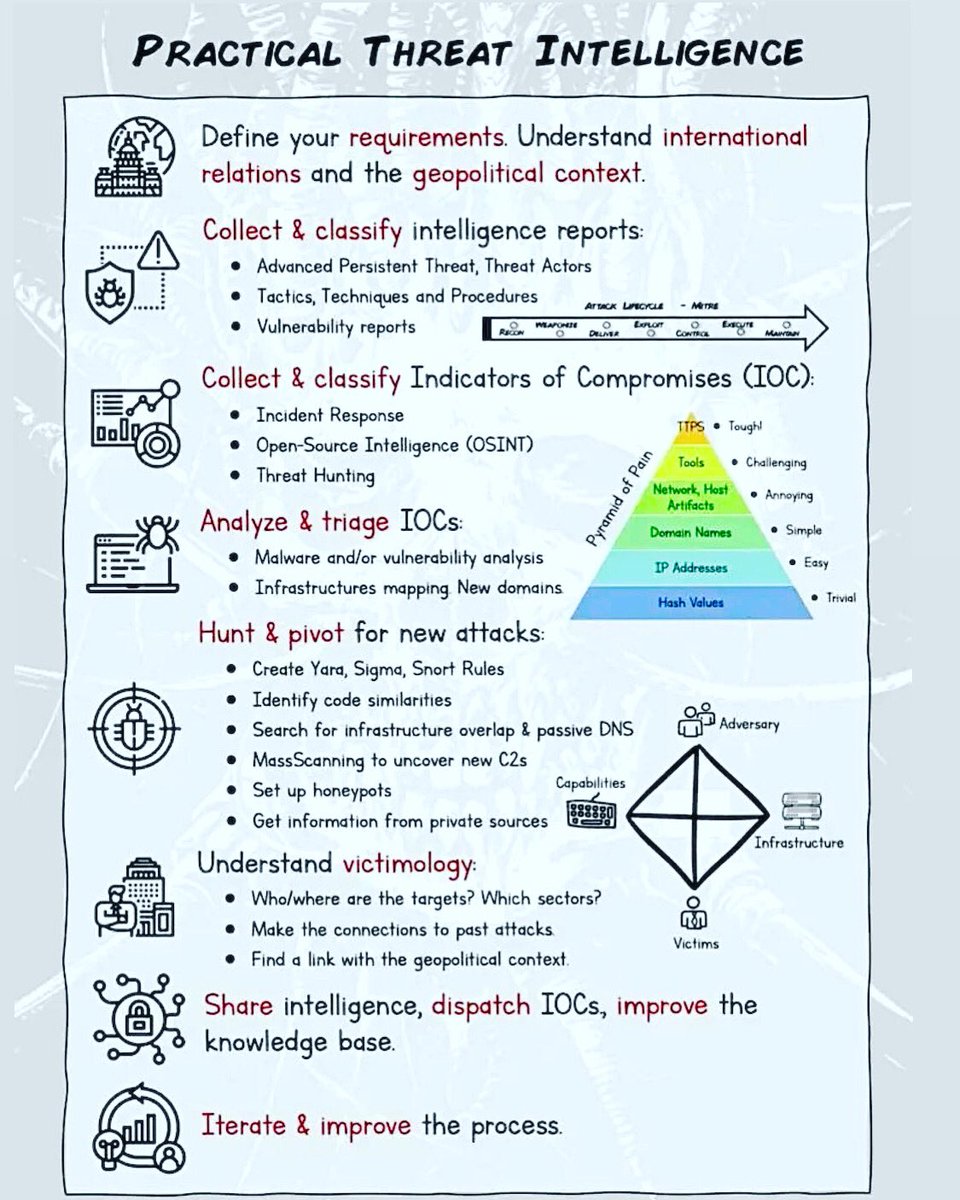
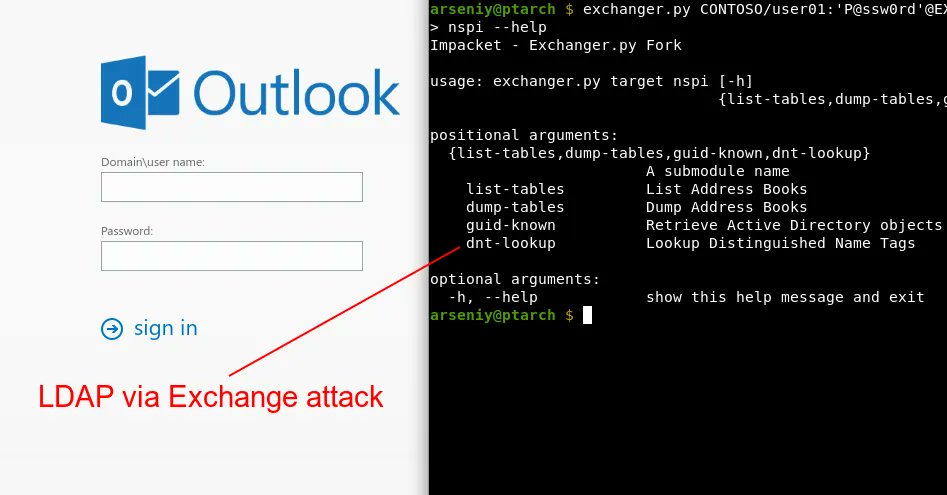
GitHub warns of Lazarus hackers targeting devs with malicious projects - Lawrence Abrams bleepingcomputer.com/news/security/…












I love this beautiful and extraordinarily well published book: "Better Data Visualizations" by Jon Schwabish Get it at amzn.to/3s2jIMX —————— #DataViz #DataStorytelling #Statistics #VisualAnalytics #DataScience #DataScientists #BeDataBrilliant