Ben Actis
@ben_ra
Former Red Team at Facebook/Meta.
My tweets are my own and not my employer.
ID: 14623175
http://cybermerchantsofdeath.com 02-05-2008 06:38:49
11,11K Tweet
3,3K Takipçi
1,1K Takip Edilen








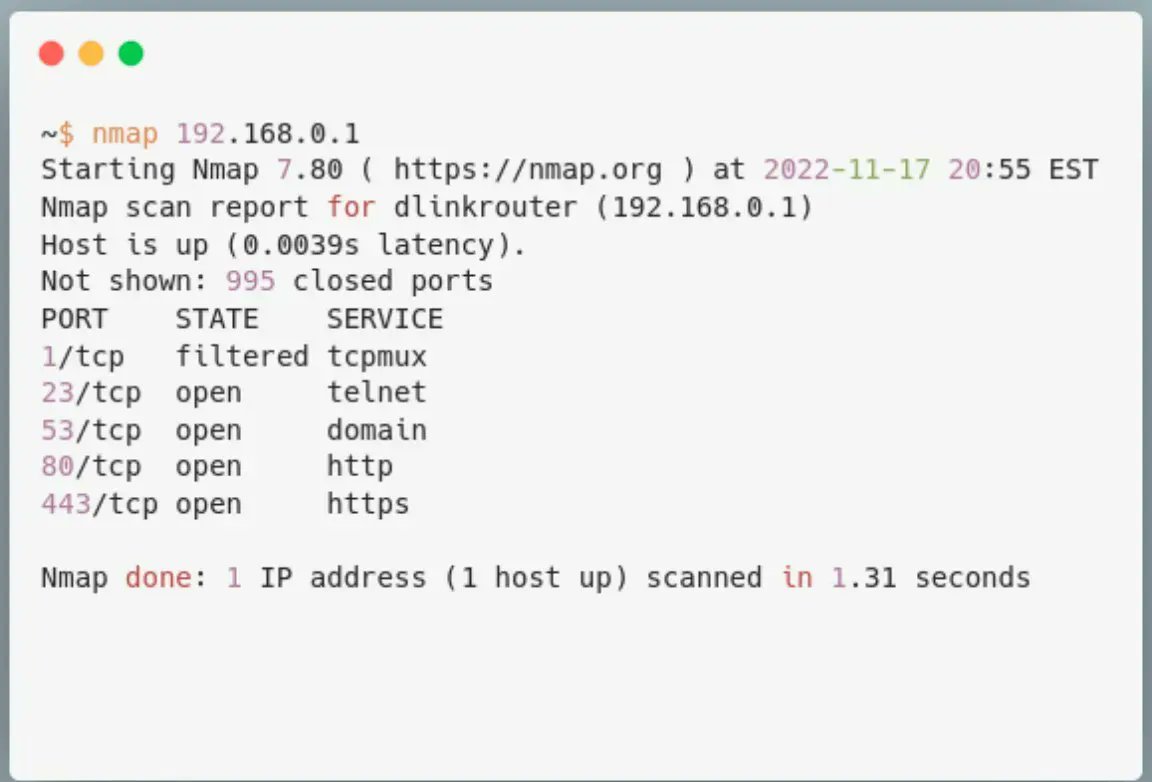
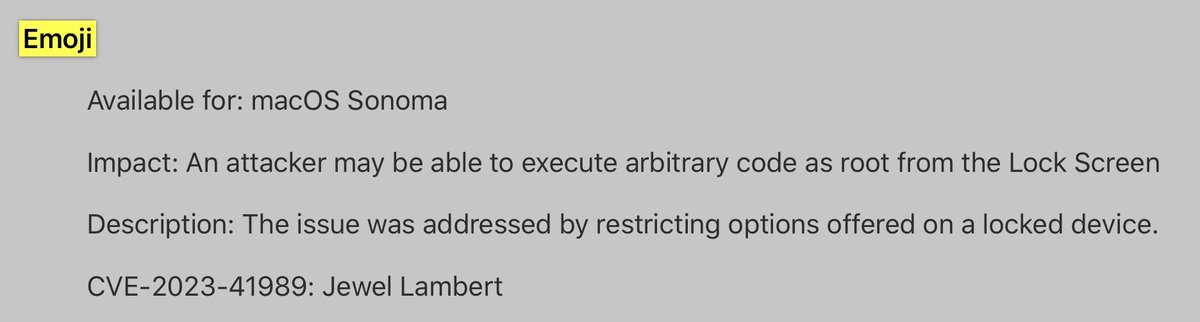
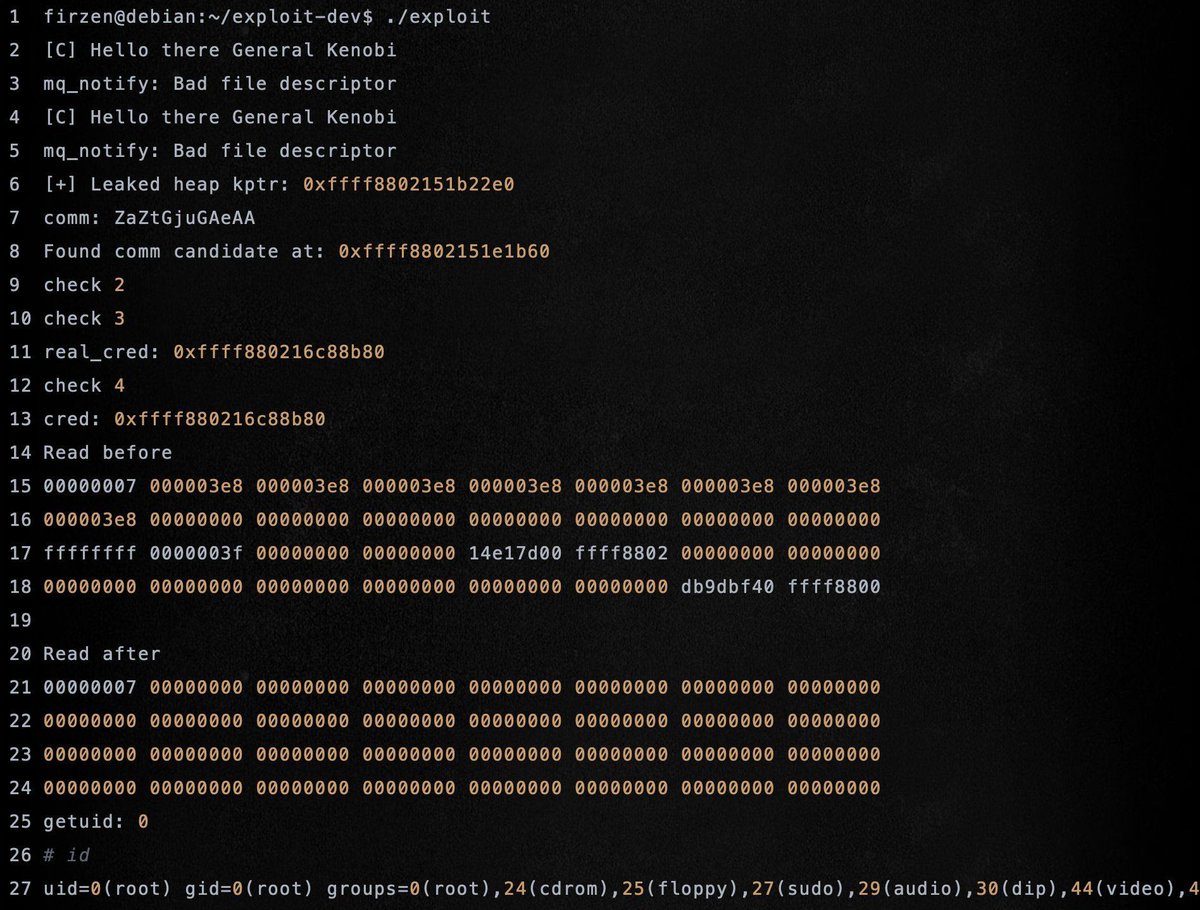
Excellent blog post for learning Linux (Android) kernel exploitation (Analysis and exploitation of CVE-2017-11176) Credits Nils Ole Timm (Blue Frost Security) labs.bluefrostsecurity.de/revisiting-cve… #Linux #android #cybersecurity





President Trump’s attempt to use the wartime law, Alien Enemies Act of 1798, to deport noncitizens without due process is yet another unlawful and brazen power grab. Read my full statement with Senator Dick Durbin, Sen. Cory Booker, and Senator Peter Welch below: