Anton Kutepov
@aw350m33
Security Researcher @attackdetection | Threat Hunting | Network Forensics | @oscd_initiative
ID: 1106974619125334017
16-03-2019 17:44:50
40 Tweet
38 Followers
109 Following










Tomorrow, Rohan Vazarkar and I are releasing the newest version of #BloodHound: 4.0. See the new features, new GUI, and new attack primitives first during our SO-CON presentation called "Six Degrees of Global Admin". Register here: specterops.io/so-con2020/eve…



finally, the video has been released: youtube.com/watch?v=Jv558o… thank you for your continuous support, John Lambert!

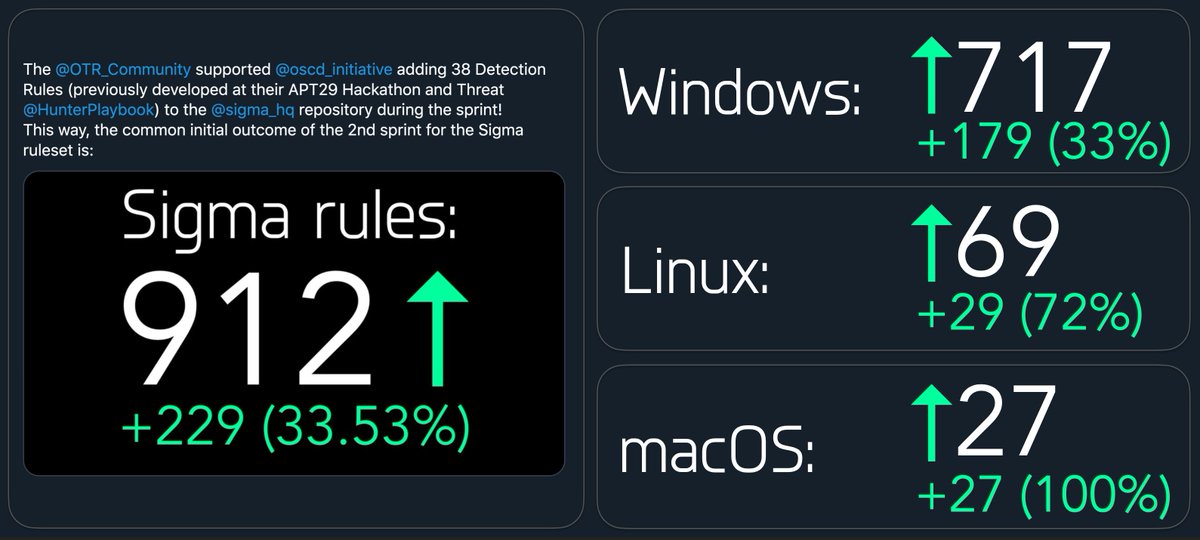
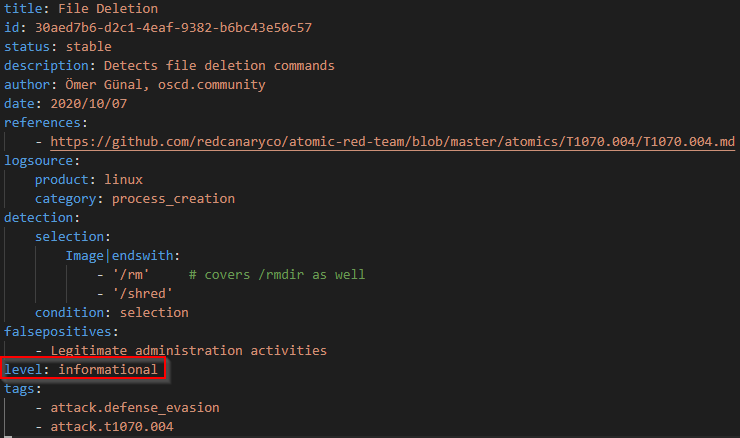
We've transferred Florian Roth ⚡️'s repository into SigmaHQ's organisation account Next steps: ./rules > separate repo ./tools > separate repo Add the 2 new repos as sub repos in the original one github.com/SigmaHQ/sigma/