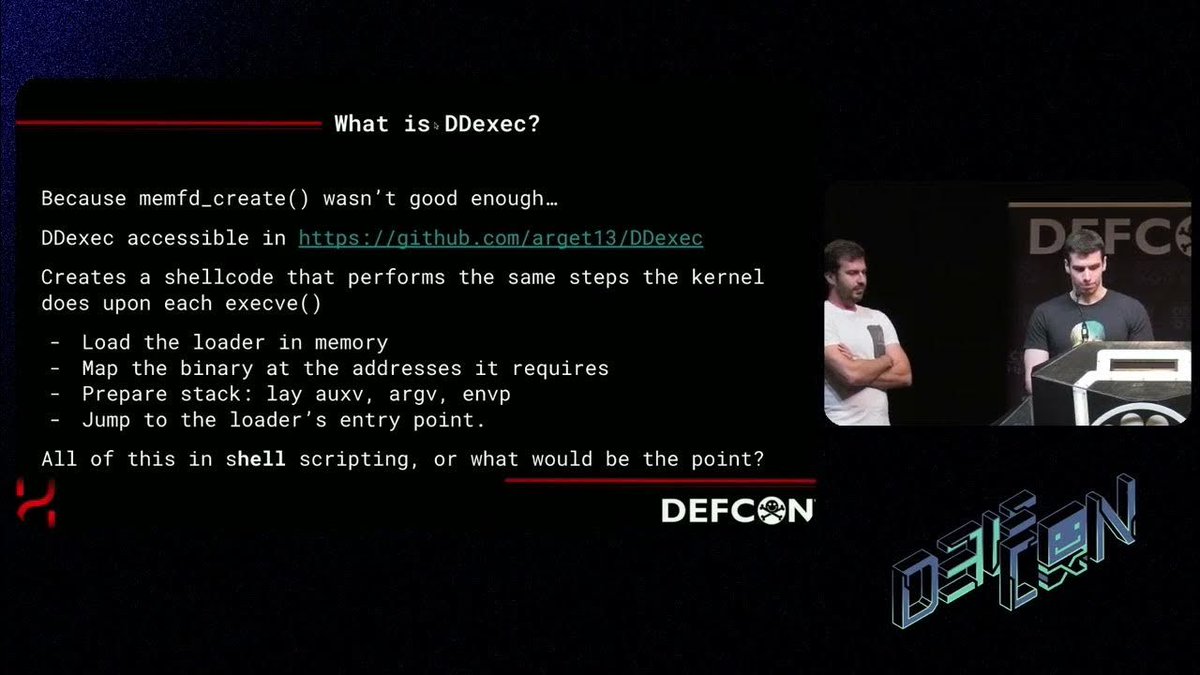
Arget
@arget1313
Telecomm. Eng. Low level stuff, pwn, C programmer and Linux internals. When you get to heaven, look me up, I won't be there, but my code will!
ID: 1441510194270244865
http://github.com/arget13 24-09-2021 21:10:13
110 Tweet
224 Followers
213 Following