Piosky
@piosky1

Our latest post explains how a TRUSTED forest/domain can be compromised by a TRUSTING forest/domain (a one-way trust). Thanks to Will Schroeder whose question inspired us, to 📔 Michael Grafnetter & @JosephRyanRies for Keys container info, and to Yuval Gordon for GoldenGMSA. improsec.com/tech-blog/sid-…











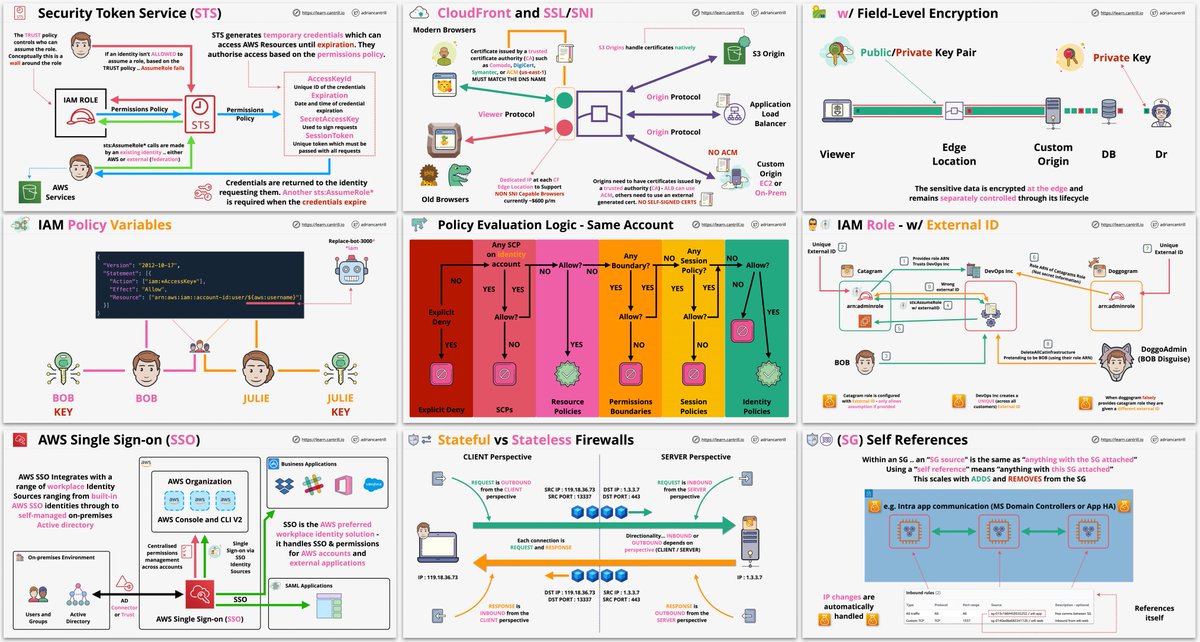
I've just opened early access for my AWS Security Specialty course (details on this thread reddit.com/r/AWSCertifica…) direct link to the course learn.cantrill.io/p/aws-certifie… and a new bundle learn.cantrill.io/p/aws-security… - new demos/lessons coming - Please Retweet #100daysofcloud #labEveryday

Hey, do you like tokens? Have you always wanted to "harvest" tokens for offensive purposes? If so check out my new post posts.specterops.io/koh-the-token-… where I show I can (finally) write a technical post without memes, and then check out the Koh toolset at github.com/GhostPack/Koh