
Andre Gironda
@andregironda
He/Him; Pre-/Post-breach Cyber Responder
ID: 327015253
30-06-2011 21:21:26
56,56K Tweet
2,2K Takipçi
6,6K Takip Edilen




Oh, you had me for this Executive Summary! Security Response Congrats Michael.Gorelik and team for the discovery.:) msrc.microsoft.com/update-guide/v…
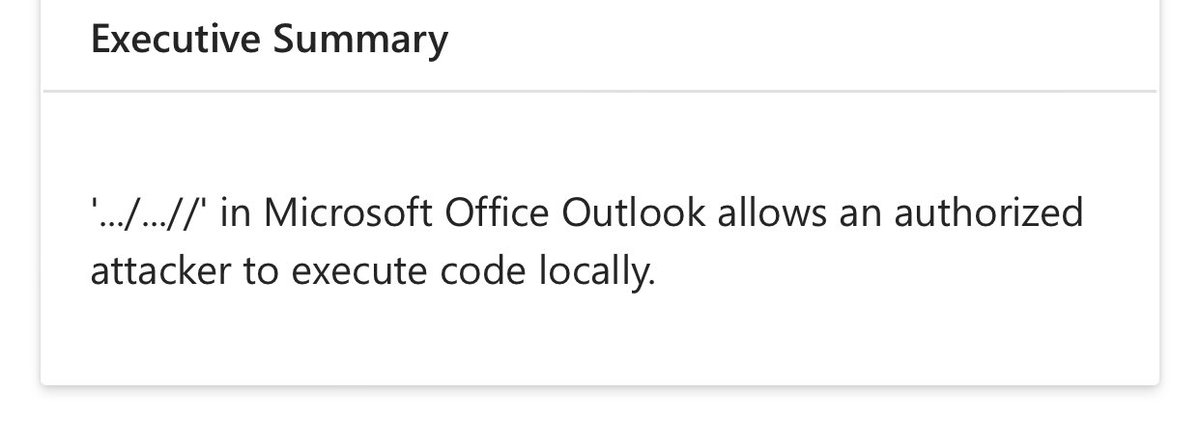

Details published research.checkpoint.com/2025/stealth-f…. To summarize: the "WorkingDirectory" problem within .url files. Oh, .url files, my old friend (I previously discovered another .url/IE 0day itw last year).. My thoughts/opinion: no organization should allow any inbound .url files in




⚠️ New threat detected: @yoti-web-share/[email protected] ⚠️ The code is suspicious as it collects environment variables, compresses them, and sends them via DNS queries to a hardcoded server. This behavior indicates potential data exfiltration, ... socket.dev/npm/package/@y…



ConnectWise rotating code signing certificates over security concerns - Bill Toulas bleepingcomputer.com/news/security/… bleepingcomputer.com/news/security/…


DanaBot malware operators exposed via C2 bug added in 2022 - Bill Toulas bleepingcomputer.com/news/security/… bleepingcomputer.com/news/security/…







![Unit 42 (@unit42_intel) on Twitter photo Cybersecurity Alert: Registered on June 7th, wwdc25[.]com hosts a #scam site impersonating the official WWDC25 event. It promotes a fake #cryptocurrency giveaway to steal funds. Do not send any cryptocurrency to the wallet addresses listed! Details at bit.ly/4mN0RCK Cybersecurity Alert: Registered on June 7th, wwdc25[.]com hosts a #scam site impersonating the official WWDC25 event. It promotes a fake #cryptocurrency giveaway to steal funds. Do not send any cryptocurrency to the wallet addresses listed! Details at bit.ly/4mN0RCK](https://pbs.twimg.com/media/GtHGYn0WIAAxwpt.jpg)
![Germán Fernández (@1zrr4h) on Twitter photo ♦️ Meta ad leads to a website that impersonates "TradingView" and downloads an MSI signed by "LLC Torgovyi Dom Energia" (now revoked).
⚠️ Final URL is different from the one shown in the ad.
https://apps-download-pc[.]com/ (malicious site is only displayed if you come from ♦️ Meta ad leads to a website that impersonates "TradingView" and downloads an MSI signed by "LLC Torgovyi Dom Energia" (now revoked).
⚠️ Final URL is different from the one shown in the ad.
https://apps-download-pc[.]com/ (malicious site is only displayed if you come from](https://pbs.twimg.com/media/GtHLPPZXAAArB49.png)


