an0nbil 🇵🇸
@an0nbil
NASA Hall of Fame Hacker 🚀🛸
🐞 Bug Bounty Hunter | 💻 Python Programmer
📝 Editor @OsintTeamBlog | ✍️ Writer @InfoSecComm
📈 1.1k+ Medium Followers (he/him)
ID: 1759577924985036800
https://linktr.ee/an0nbil 19-02-2024 13:57:38
280 Tweet
381 Followers
1,1K Following











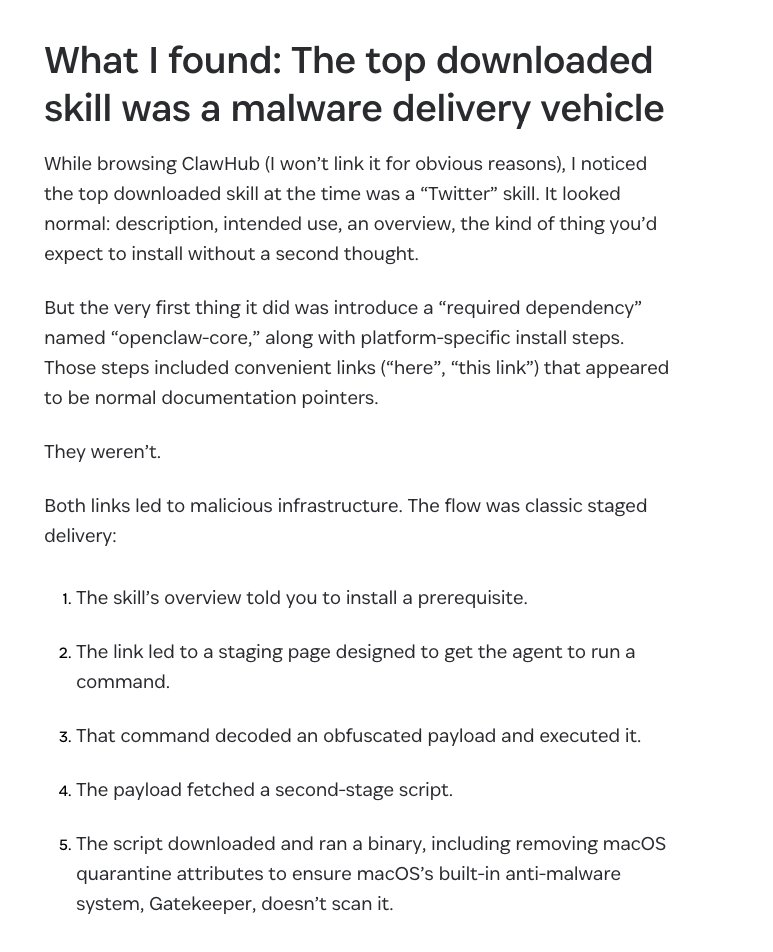
Looks like some of the commands are still running on 'clawdbot', not moltbot, like: moltbot uninstall → moltbot: command not found clawdbot uninstall → works. SOURCE: docs.molt.bot/cli/uninstall Peter Steinberger 🦞 Please take a look at it.





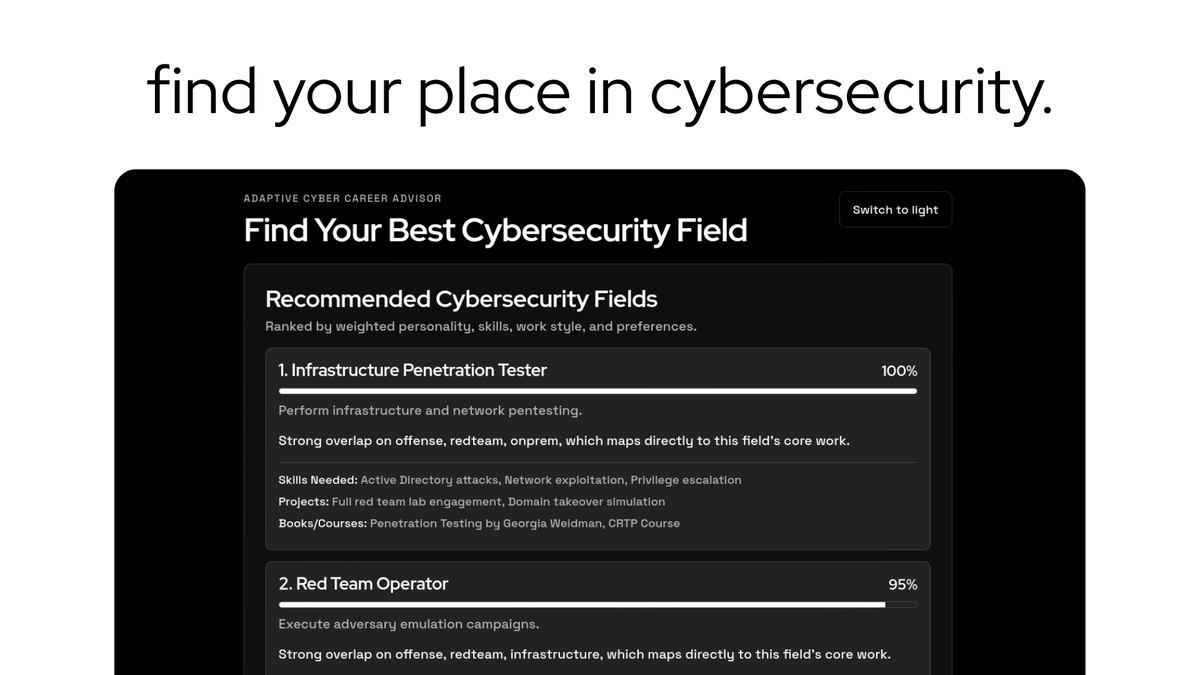
.Hex Security (YC W26) is building AI agents that hack your systems before real attackers do. In weeks, their agents uncovered critical flaws at dozens of unicorns, earning over $250K in bounties. Hex already protects companies processing billions in transactions and millions of user