Amila P.
@amilamx
Senior Associate | Managed Cyber Defence, Cyber Threat Operations at PwC
ID: 66775687
18-08-2009 19:35:23
424 Tweet
248 Followers
583 Following




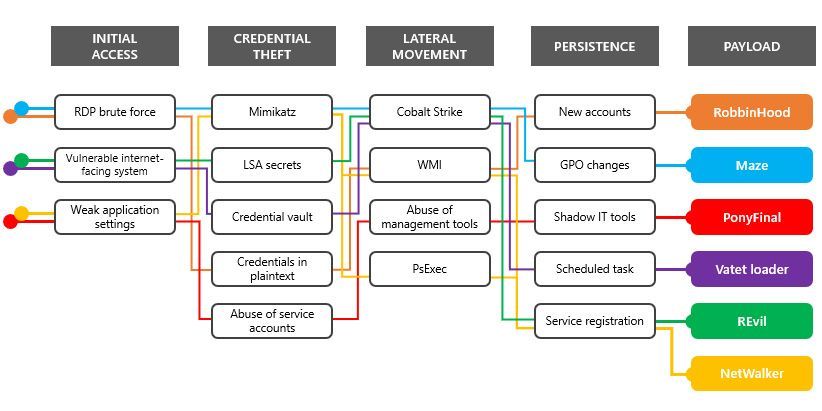
How to thwart human-operated ransomware campaigns? - Help Net Security j.mp/3ovdXqf #Infosec #CyberSecurity #CyberAttack #Hacking #Privacy #Threat #Malware #Ransomware #Cyberwarning #Phishing #SpyWare #Tech #Technology Mauricio Amaro L. 🇨🇱🇲🇽

Cisco Zero-Day in AnyConnect Secure Mobility Client Remains Unpatched(Exploit Code Available): threatpost.com/cisco-zero-day… via Threatpost


Delighted to see our commitment has recognised to become one of the eight ACE-CSEs in the country. Well done USW Cyber Security USW Cyber Security & Digital Forensics.


Our own USW Cyber Security student Jack Tabash(Jack) University of South Wales featured in Charted Institute of Information Security @CIISecHQ magazine under outstanding Cyber students in 2020. Proud of you Jack. 👋👋👋 ⭐️🏅 #CyberSecurity







Good luck Sam Chapman Skinner working hard with his team #QuantumOfPolicy to prepare for the #Cyber912 finals next week. A great opportunity for Keele University 🐿️ Durham University University of Bristol University of South Wales students to experience cyber security at the highest level UK Cyber 9/12 Strategy Challenge Atlantic Council