ahmed
@ahmedang3l
You will never break me
ID: 160927384
29-06-2010 13:55:16
1,1K Tweet
2,2K Followers
867 Following






[BLOG] An investigation on open reverse proxy misconfiguration and automating the misconfiguration using nuclei templates by our own Chris Sullo Part: 1 blog.projectdiscovery.io/abusing-revers… Part: 2 blog.projectdiscovery.io/abusing-revers… #hackwithautomation #infosec #security #bugbounty
![ProjectDiscovery (@pdiscoveryio) on Twitter photo [BLOG] An investigation on open reverse proxy misconfiguration and automating the misconfiguration using nuclei templates by our own <a href="/chrissullo/">Chris Sullo</a>
Part: 1 blog.projectdiscovery.io/abusing-revers…
Part: 2 blog.projectdiscovery.io/abusing-revers…
#hackwithautomation #infosec #security #bugbounty [BLOG] An investigation on open reverse proxy misconfiguration and automating the misconfiguration using nuclei templates by our own <a href="/chrissullo/">Chris Sullo</a>
Part: 1 blog.projectdiscovery.io/abusing-revers…
Part: 2 blog.projectdiscovery.io/abusing-revers…
#hackwithautomation #infosec #security #bugbounty](https://pbs.twimg.com/media/FJSpRIhaMAAqmBt.jpg)

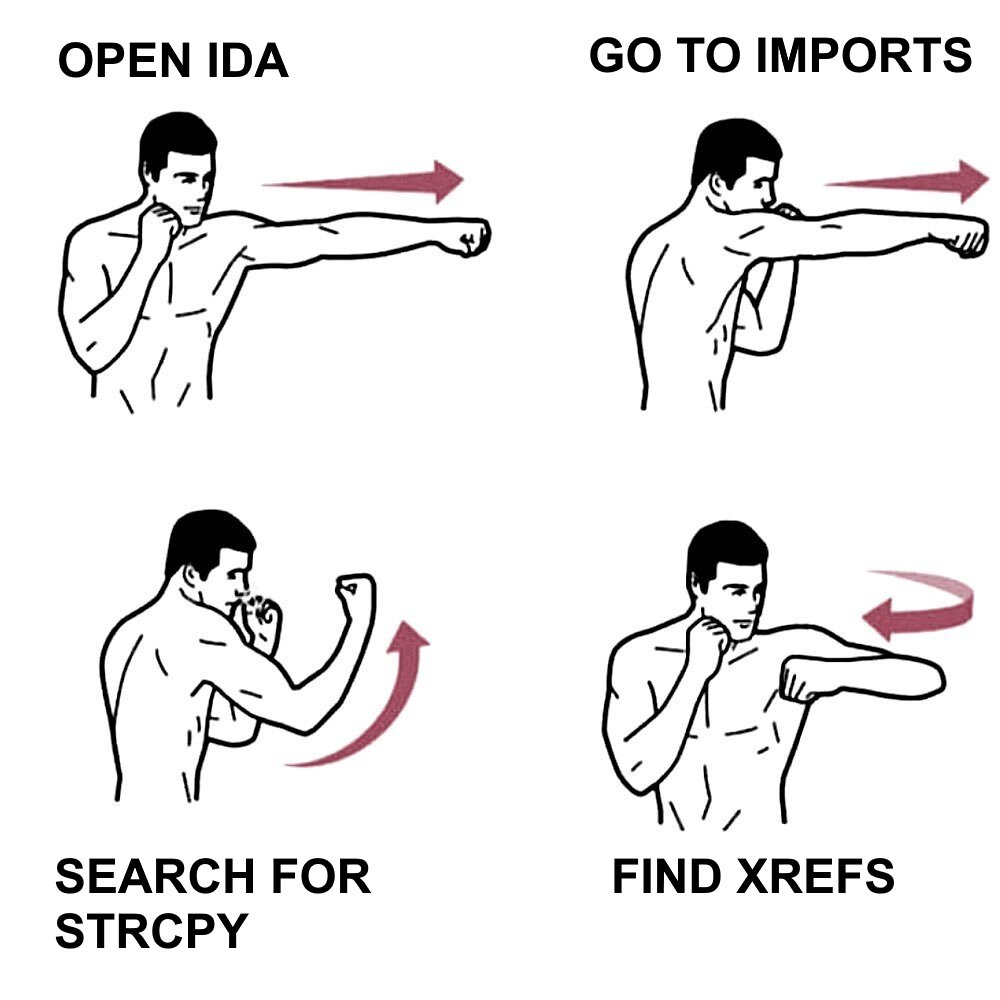
Revisiting the ESC7 AD CS attack, which can lead to Active Directory privesc from ManageCA permissions. Our #RedTeam has automated this attack by adding new features to SpecterOps' Certify /cc Kurosh Dabbagh Marcos Díaz blackarrow.net/adcs-weaponizi…




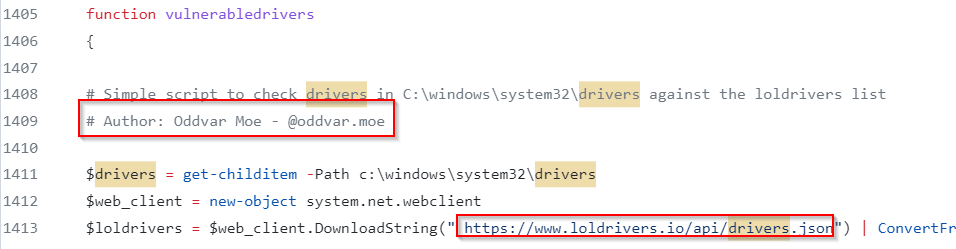
I created this quick and dirty Powershell script to check your current system drivers against the awesome loldrivers.io list from The Haag™ Jose Enrique Hernandez Nasreddine Bencherchali Hope you find it useful gist.github.com/api0cradle/d52…



We took a Cobalt Strike profile, modified it, and bypassed Crowdstrike & Sophos without encrypting the shellcode. Also bypassed all published YARA rules, sleep detections, and string detections around a CS beacon. Blog: whiteknightlabs.com/2023/05/23/unl… #CyberSecurity #redteam #infosec